Let’s face it. We live in an era of constant data breaches. And as unpleasant as they are, we are forced to adapt and learn to live with them.
But it’s incredibly frustrating seeing companies not caring about protecting your information. And the feeling only worsens when hacked companies don’t even face a proper penalty.
It’s probably what the 383 million people who were part of the Marriott hotel data breach from 2014 must feel right now.

That’s because the Information Commissioner’s Office in the UK has reduced Marriott’s fine for its data breach from the initial $123 million to a mere $23.8 million.
Keep reading for the full story.
How the Marriott data breach came to be
The Marriot data breach is one of the biggest ever.
It all begins in 2014, when the Starwood hotel chain, part of Marriott, suffered a security breach.
An unknown attacker got a web shell into a Starwood device. A web shell is a malicious script used to escalate and maintain access to an already compromised web application.
The hotel’s hacker was able to access and edit this device’s contents remotely. He then installed malware on it, ultimately gathering users’ login credentials within the Starwood network.
Later on, the attacker accessed and exported Starwood’s database with all the reservation details from customers.
Marriott purchased Starwood in 2016. Yet, two years later, Starwood was still using its own reservation system and IT infrastructure, which proved not to be secured enough.
In September 2018, an internal security tool found a suspicious attempt to access Starwood’s guest reservation database. The warning led to an internal investigation that discovered somebody had exploited the Starwood network back in 2014.
So, four years after the attack, Marriott revealed the data breach.
The cyberattack exposed the records of 339 million guests worldwide, including their names, email addresses, phone numbers, and passport details.
Fining Marriott for the data breach
UK’s watchdog’s initial penalty for the Marriott breach would have been one of the most considerable fines issued under the General Data Protection Regulation (GDPR): $123 million.
The final decision to reduce the penalty to nearly $24 million only covers the portion of the breach that dates 25 May 2018, when the GDPR came into effect.
According to GDPR’s ‘The right to be informed,’ companies must inform their clients if a data breach happens, especially if it involves their data. The notification must come within 72 hours after a business becomes aware of a breach.
But Marriott’s breach remained undisclosed for four years, and the victims couldn’t do anything. Had they known about it sooner, they would have a chance to do their due diligence, change their passwords, protect their payment details, and increase their cybersecurity.
Based on another GDPR principle, ‘privacy by design,’ any company that stores personal data needs to have IT systems that can reasonably manage people’s information and keep the risks of data breaches at a minimum.
However, the UK Information Commissioner’s Office investigation concluded that Marriott didn’t put the “appropriate technical or organizational measures in place to protect people’s data” — as required by the law.
The sad reality is, as a client or simple user online, no law or regulation can fully protect you from becoming a data breach victim. And regardless of companies’ efforts to enforce secure networks, hackers can still find a loophole if they want to break in and steal data.
Check if you’ve been affected
With one hacking attack occurring every 39 seconds, billions of people worldwide have already been affected.
But with CyberGhost ID Guard, you can check if your email addresses have been compromised and get an overview of your accounts, all in one place.
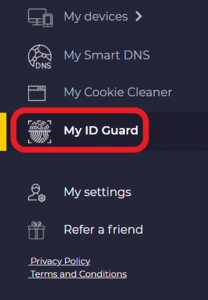
The process is simple. You just need to log into your CyberGhost VPN account, and we will do all the heavy lifting for you.
What’s more, we offer ongoing monitoring services. This way, if your email addresses are ever involved in a breach, we alert you, allowing you to change your password quickly.
Has your personal information ever been exposed in a data breach? Did you do anything to avoid this from happening in the future?
Let me know in the comments below.

Leave a comment