When you sign up for a new service, send customer feedback, or register for an online contest, security is probably the last thing you think about. The keystrokes you make while filling out forms on a website aren’t a big deal, right? Especially if you end up changing or deleting that information. Now it seems that might not be true.
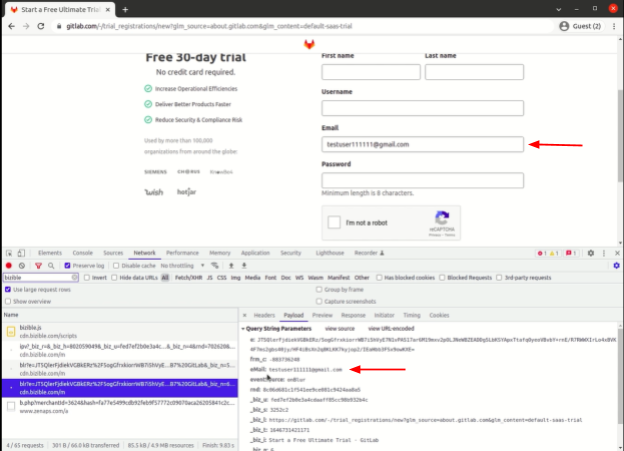
New research finds that both popular websites and third parties across the web are tracking everything you type before you hit the submit button. That includes email and password forms. Apparently, some log every keystroke you type while others log the complete field whenever you click somewhere else on the website.
Websites and Third Parties Track Your Keystrokes
Researchers from KU Leuven, Radboud University, and the University of Lausanne analyzed the top 100,000 websites in the US and UK. They found that thousands of websites are tracking everything you type.
Some websites seemingly don’t purposely conduct the keylogging themselves but have third-party marketing integrations that track visitors’ keystrokes. These third-party trackers secretly collect all that information without having to adhere to data protection laws.
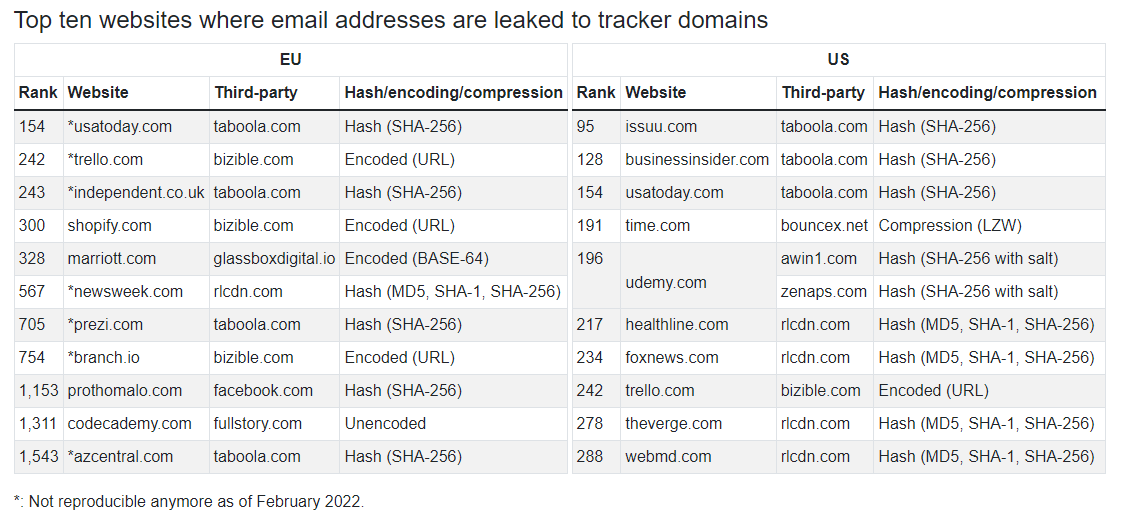
This type of personal data invasion has been dubbed “leaky forms.” As of yet, it is unclear how prevalent the issue is. The paper released by the researchers mainly focuses on email and password leaks but says the keyloggers track across all forms. That may include payment form submissions, which has potentially disastrous implications.
What Are Keyloggers?
Keyloggers are traditionally malicious programs used by cybercriminals to capture everything you type. Different types of keyloggers exist and can be used to log what you type into a website, app, or even your device if it’s infected with malware.
The keyloggers that websites and third-party add-ons use can vary as well. Some appear to be session replay scripts that log users’ entire session on the page including keystrokes and mouse movements.
How is This Happening on Top Websites?
While websites themselves also log keystrokes and mouse movements, most of the leaks involved third-party trackers. Websites generally use third-party trackers to log how users interact with the website for page optimization, bug reports, and marketing purposes. The problem is, website owners/administrators often don’t vet how these trackers collect or store user information.
In edge cases, extensive logging can also result from configuration errors, as was the case with 52 of the websites the researchers analyzed. Russian tech giant Yandex was responsible for 50 of these leaks. After investigating, they found Yandex Metrica’s code showed that it has filters to exclude password fields from the collection.
It seems that almost all of the Yandex leaks resulted from websites that were built using the React framework. The researchers informed Yandex of the leaks and all 52 instances have been resolved. Most of the keylogging leaks aren’t accidental though. Companies like Meta and TikTok use invisible trackers to log users’ email addresses and follow them around the web.
Two of the Biggest Culprits: Meta and TikTok
While investigating third-party keylogging, the researchers discovered trackers dubbed Meta Pixel and TikTok Pixel. These invisible marketing trackers offer an “automatic advanced matching” option that triggers data collection when a user submits a form.
In reality, the Pixel trackers log people’s hashed email addresses to identify a user across websites and platforms. Hashing involves encoding information using a cryptographic function to make information unreadable. That means, the trackers can’t necessarily see people’s real email addresses (although they likely… still do).
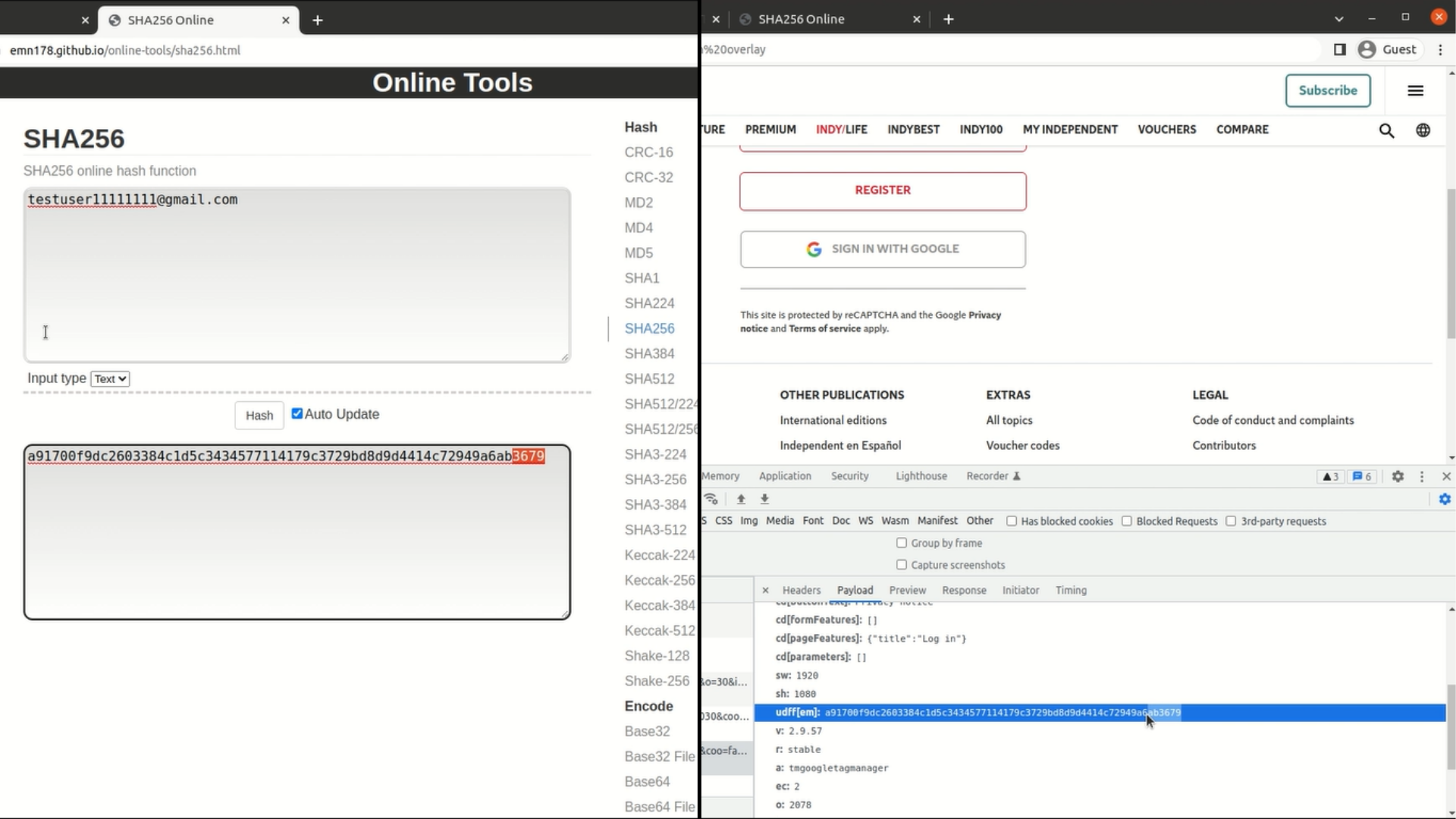
Meta & TikTok can use these hashed email addresses to follow your every move online as they’re a unique identifier like a mobile number. They can also possibly link those hashed email addresses with people’s IP addresses and other data gathered across various websites, including their own platforms.
That allows them to create incredibly detailed – read invasive – digital profiles of almost anyone on the planet. The researchers reached out to both companies about the issue in March and April respectively. Meta indicated it has assigned an engineer to investigate the problem but has not provided any further feedback while TikTok is yet to respond.
Data Protection Initiatives Offer a Trivial Buffer
Right now, there are very limited protections in place that prioritize personal privacy online. These mainly come in the form of data protection laws like California’s Consumer Privacy Act and consent management laws like the EU’s GDPR.
The problem is, companies have already found ways around consent and cookie-based data protection requirements. The research paper mentions a recent study by Papadogiannakis et al. that examines how websites bypass GDPR rules. It found that websites are more likely to use sophisticated tracking techniques such as ID syncing and fingerprinting when users reject cookies.
The researchers found the opposite is true for form submissions, but only to a small degree. “When we reject all data processing, the number of sites with leaks to trackers decreases by 13% in the US, [and by] 0.05% in the EU. The reduction in leaks in both cases is limited, thus confirming Papadogiannakis et al.’s conclusion that cookie consent choices are not effective in preventing tracking,” the researchers said.
Meta and TikTok’s Pixel trackers are another example of how companies keep finding ways to track people online despite data privacy laws.
Besides campaigning for more data privacy, you can’t prevent companies from tracking what you do on websites or from following you all over the web. Especially since you have little to no control over the trackers websites use.
Protect Your Digital Identity
You can improve your online privacy by installing a VPN to prevent websites from tracking your online activity using your IP address. It won’t stop websites from logging your keystrokes, but it can protect your online identity against many different digital trackers. CyberGhost VPN improves your privacy thanks to our strong encryption, No Logs policy, and RAM-only servers.
As long as you’re mindful of what you do online, you can avoid handing over too much information to companies – and by extension, cybercriminals. Keep in mind, websites can’t log any personal information you don’t willingly put in.

Leave a comment
maxter
Posted on 23/10/2022 at 21:11
sir my name is hafix JB can you plz gave me the info about logs how to find anyother logs and how to relocate via rubber ducky and key loggers
Ghostie
Posted on 24/10/2022 at 10:55
Hi JB, are you looking for more information about the technology that logs your online browsing? These are varied, and includes various trackers used by the browser you use and the websites you visit. Many websites use multiple plugins to track your time on the site – some even track you after you close the page. Unfortunately, we don’t have a comprehensive guide on the various types of trackers that log your online data, but we do have a guide for picking a privacy browser like duckduckgo: most secure private browsers.