Media Access Control
Media Access Control Definition
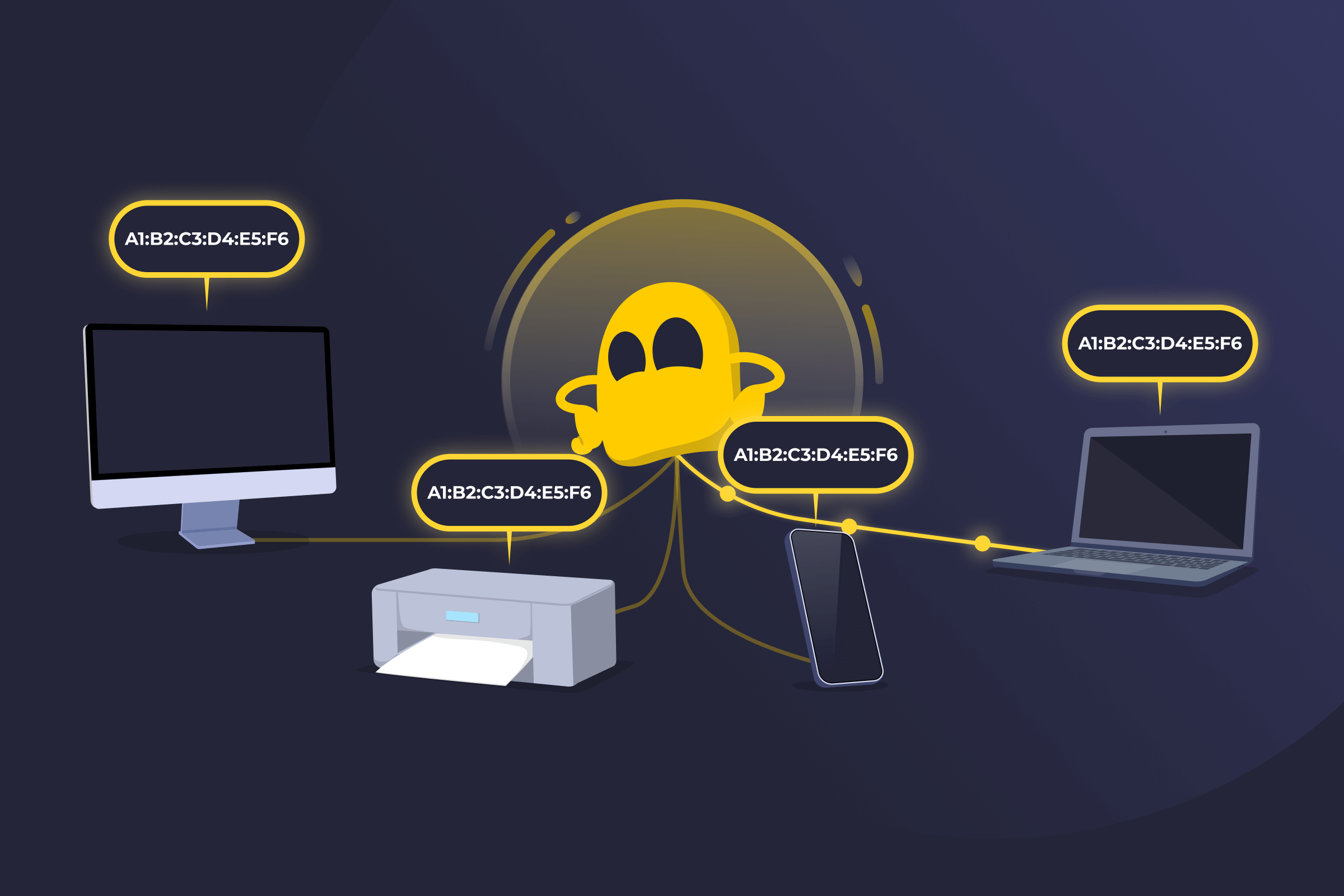
Media Access Control (also known as MAC) is a networking system that helps devices on the same network recognize each other and take turns sending data. Every device that connects to a network, like a laptop, phone, or printer, has a MAC address that acts as its built-in network ID.
This address helps the network know where data should go and prevents devices from talking over each other. Media Access Control works behind the scenes in both wired and wireless networks to keep local communication organized and running smoothly. MAC filtering is also used to add an extra layer of security and manage access for small, non-complex networks.
How Media Access Control Works
Each network device has a network interface, such as an Ethernet card or Wi-Fi adapter. That interface contains a MAC address, which is a hardware-based identifier assigned during manufacturing. A MAC address is typically written as six pairs of letters and numbers. The first half identifies the manufacturer of the network interface, and the second half uniquely identifies that specific device.
When a device joins a local network, it uses its MAC address to communicate at the Data Link Layer (Layer 2) of the OSI model. When data is sent, it’s packaged into frames that include both a source MAC address and a destination MAC address. Network switches read these addresses to decide where the frame should go, forwarding it only to the correct device instead of broadcasting it everywhere.
Benefits of Media Access Control
- Local device identification: Helps networks recognize individual devices using hardware-based addresses.
- Efficient data delivery: Allows switches to forward data directly to the correct device instead of broadcasting it to everyone.
- Collision management: Supports rules that control when devices transmit data on shared connections.
- Compatible with wired and wireless networks: Operates consistently in Ethernet and Wi-Fi environments.
- Simple access controls: Can support basic device-level filtering in smaller or controlled networks.
Limitations of Media Access Control
- Limited security: MAC addresses can be spoofed, which makes them unreliable as a sole security measure.
- Local network scope only: MAC addresses work within a local network and don’t route traffic across the internet.
- Scalability challenges: Managing device-level controls using MAC addresses becomes difficult in large networks.
- No built-in encryption: MAC identifies devices but doesn’t protect the content of transmitted data.
- Hardware dependency: Each network interface has its own MAC address, which can complicate tracking in virtualized or multi-interface environments.
Read More
FAQ
Media Access Control manages how devices use a shared network connection. It decides when a device can transmit data and helps prevent signal collisions. On modern switched networks, it also ensures data frames are delivered to the correct device within the local network.
Without Media Access Control, devices on the same network could transmit at the same time and interfere with each other. MAC keeps communication organized, reduces transmission conflicts, and ensures data moves efficiently across wired or wireless connections.
Ethernet and Wi-Fi both use Media Access Control methods. For example, Ethernet originally used a system that listened for activity before sending data to reduce collisions. Wi-Fi uses a similar principle, checking whether the channel is free before transmitting. These rules are part of the MAC sublayer at the Data Link Layer.
A MAC address is a factory-assigned, hardware-based identifier used inside a local network. It helps switches deliver data to the correct device within the same network segment. An IP (Internet Protocol) address is assigned by a network or internet service provider and is used to route data between different networks. IP addresses can change, while MAC addresses are typically fixed to a device’s network interface.
 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee