ASLR
ASLR Definition
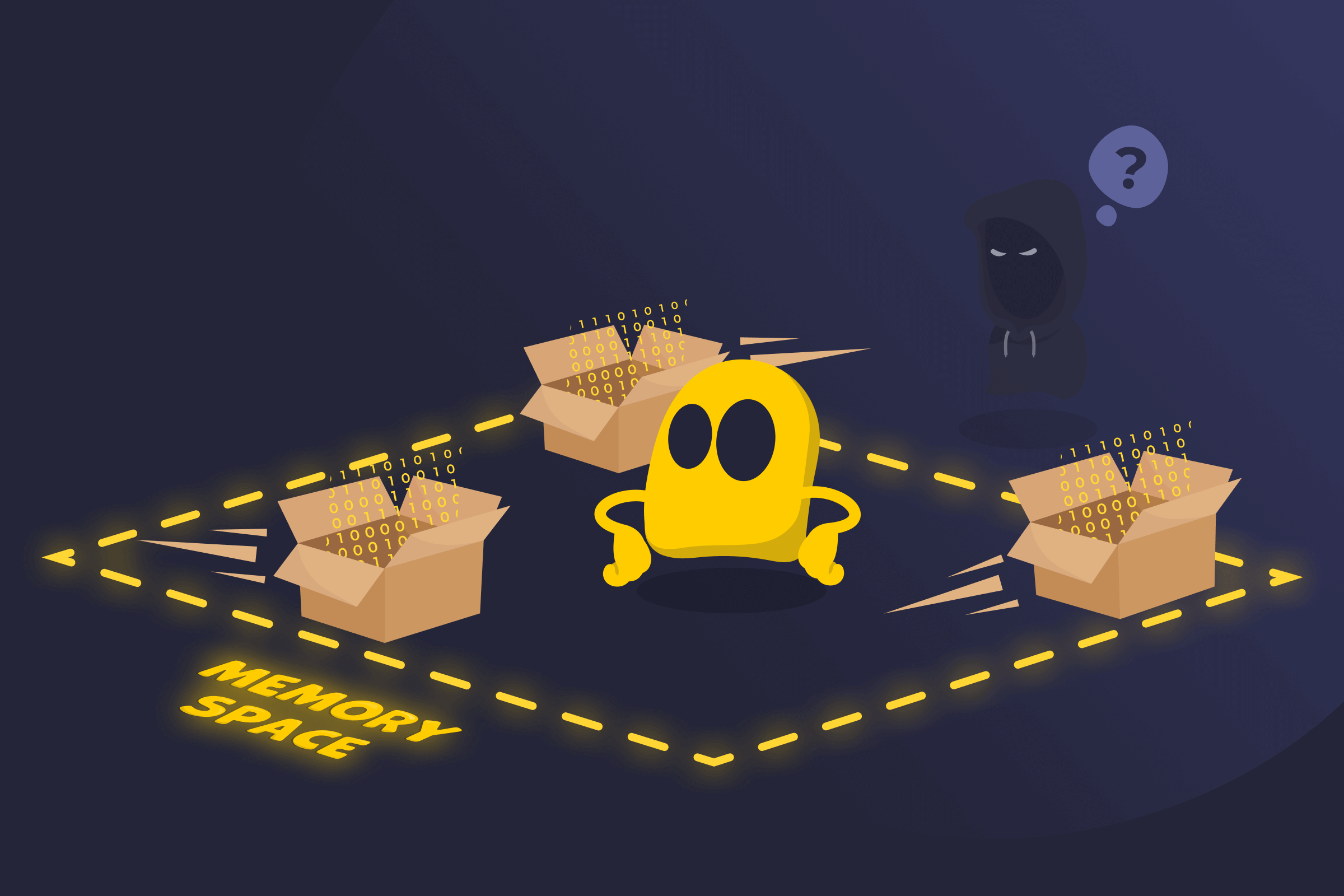
Address Space Layout Randomization (ASLR) is a built-in operating system security feature that helps protect against memory-based attacks. It works by randomizing where programs and system components are placed in memory each time they run.
By making memory layouts unpredictable, ASLR reduces the reliability of exploits that depend on knowing exact memory addresses. It doesn’t remove software vulnerabilities, but it makes them significantly harder to exploit. ASLR operates at the system level and protects supported applications automatically without changing how they function.
How ASLR Works
When a program starts, the operating system assigns it space in memory. With ASLR enabled, these memory locations are different each time the program runs.
Key parts of the program, such as executable code and shared files, load into different positions on each launch. The program works the same for the user, but its internal layout shifts in the background. Because the layout changes over time, the memory addresses aren't consistent between runs. This change happens automatically and doesn't require any action from the user or the software.
Pros of ASLR
- Lower exploit reliability: Makes memory corruption attacks harder to execute consistently.
- System-wide protection: Applies broadly across supported applications without requiring changes to each program.
- Compatibility with other defenses: Complements protections such as Data Execution Prevention (DEP).
- Transparency: Doesn’t affect normal application functionality or performance in most cases.
Cons of ASLR
- Information leaks: Exposure of memory addresses can weaken ASLR.
- Limited address space: Fewer possible layouts reduce its effectiveness on older systems.
- Incomplete support: Some programs still use fixed memory locations.
History of ASLR
- Early Linux hardening efforts (2001): The PaX project introduces practical memory randomization techniques as part of its security patches for Linux, laying the groundwork for what would become ASLR.
- OpenBSD implementation (2003): OpenBSD integrates address randomization into its operating system as part of its broader security-first approach.
- Linux kernel adoption (2005): ASLR support becomes part of the official Linux kernel, allowing mainstream distributions to use memory randomization without third-party patches.
- Windows integration (2007): Microsoft introduces ASLR in Windows Vista as part of a larger effort to reduce common memory exploitation techniques.
- Broader Apple platform support (2011): Apple expands ASLR use across macOS and iOS devices, increasing memory randomization coverage on both desktop and mobile devices.
Read More
FAQ
Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP) protect programs in different ways. ASLR changes where parts of a program sit in memory. This makes it harder for an attack to jump to a specific location.
DEP controls what memory can do. It blocks code from running in areas meant only for data, like the stack or the heap. In short, ASLR hides locations, while DEP blocks execution. They work best when used together.
Address Space Layout Randomization (ASLR) helps protect against buffer overflow attacks, stack smashing, heap overflow attacks, return-to-libc attacks, code injection attacks, and jump-oriented attacks. It also makes Return-Oriented Programming (ROP) harder to pull off.
Yes, Address Space Layout Randomization (ASLR) can be bypassed in some situations. This usually happens when another weakness leaks memory addresses. Once that information is exposed, the random layout loses much of its value.
Address Space Layout Randomization (ASLR) has little to no noticeable effect on performance. The memory changes happen when a program loads, not while it runs. Most users won’t notice any difference during normal use.
Yes, Address Space Layout Randomization (ASLR) works on 32-bit systems, but it offers less protection. There are fewer memory layout options, which makes guessing addresses easier. ASLR still helps, but it works much better on 64-bit systems.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee