Biometric Spoofing
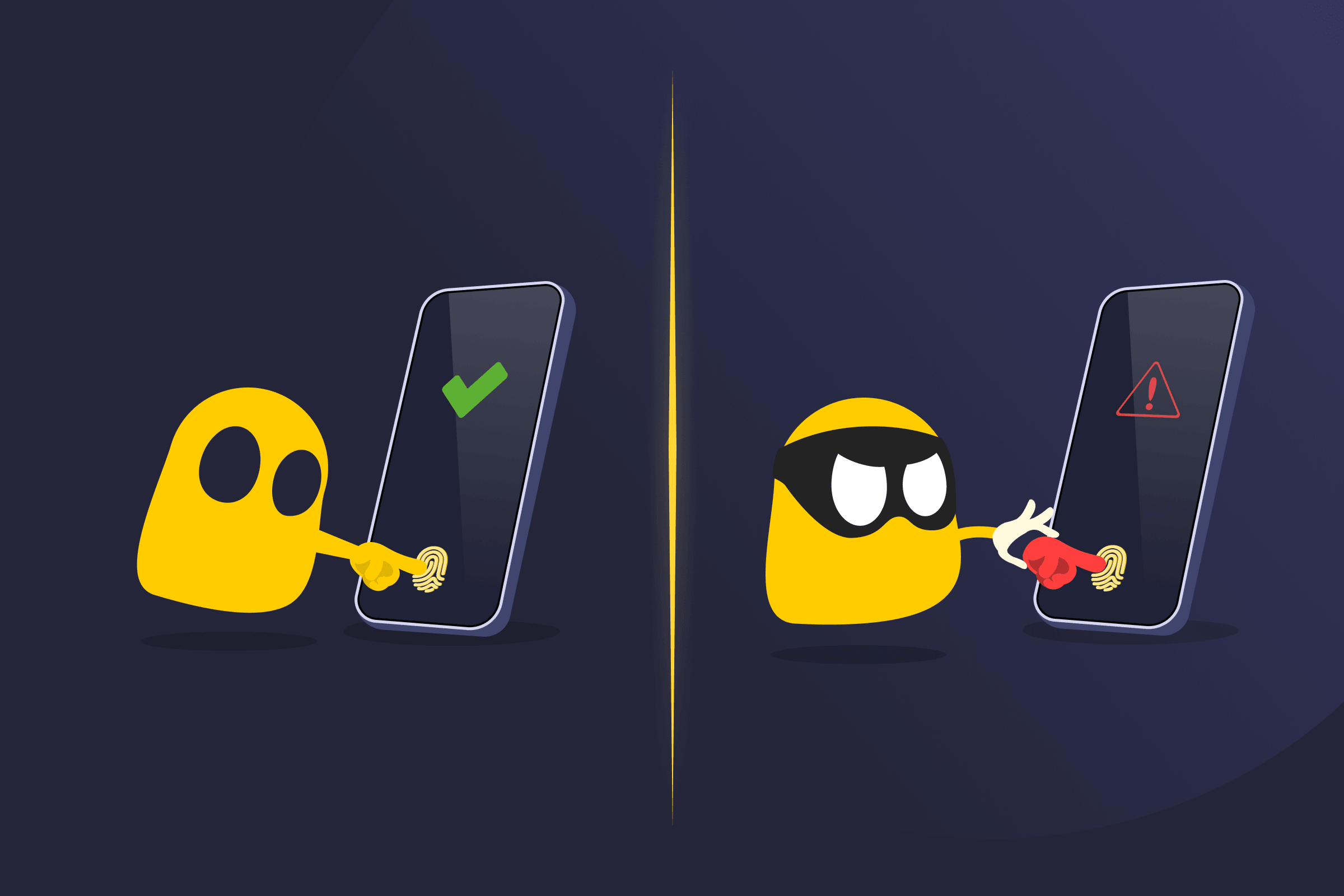
Biometric Spoofing Definition
Biometric spoofing is a type of cyberattack in which an attacker mimics a person’s unique biological traits, such as fingerprints, facial features, or voice, to bypass authentication systems. Rather than stealing passwords, attackers use fake physical or behavioral data to trick systems into granting unauthorized access to devices, accounts, or secure environments.
How Biometric Spoofing Works
Biometric systems authenticate users by comparing a live sample to stored biometric data. Spoofing occurs when an attacker presents a fake version of that trait. It typically follows this process:
- The system captures a biometric sample (e.g., fingerprint, face, voice).
- The sample is compared against stored data.
- A spoofed input mimics the real trait closely enough to pass verification.
- The system mistakenly grants access to the attacker.
Common Biometric Spoofing Techniques
- Fingerprint spoofing: Recreating fingerprints using lifted prints and materials like silicone or gelatin.
- Voice spoofing: Using recorded audio or AI-generated voice clones to bypass voice authentication.
- Iris spoofing: Presenting high-resolution or digitally altered iris images to scanners.
- Face spoofing: Using printed photos, 3D masks, or deepfake videos to bypass facial recognition.
Risks and Challenges of Biometric Spoofing
- Unauthorized access: Attackers may gain entry to secure systems or sensitive data.
- Device vulnerabilities: Weak or poorly configured systems are easier to exploit.
- Difficult recovery: Biometric traits are difficult to change if compromised.
- Loss of trust: Successful attacks can reduce confidence in biometric security.
- Rising sophistication: AI, deepfakes, and voice cloning make attacks more convincing.
Tips on Mitigating Biometric Spoofing Attacks
- Use liveness detection to verify real human presence (e.g., blinking, movement, heat signatures).
- Combine biometrics with multi-factor authentication (MFA) for added security.
- Implement anti-spoofing technologies such as depth sensing or infrared scanning.
- Regularly update biometric systems to address new vulnerabilities.
- Store biometric data securely using encryption and secure enclaves.
- Limit the number of failed authentication attempts to reduce abuse risk.
- Monitor for unusual access patterns or anomalies in authentication behavior.
- Use multiple biometric factors for higher assurance.
Read More
FAQ
Biometric spoofing is when someone pretends to be you by copying your physical traits, like your fingerprint or face, to trick a security system. Instead of stealing a password, the attacker uses a fake version of your identity, similar to using a realistic prop to unlock something that normally requires your presence.
Biometric systems are generally more secure than passwords because they rely on unique physical traits. However, they’re not impossible to bypass. The level of security depends on the quality of the system, such as whether it includes liveness detection or multiple authentication layers. Simpler systems are more vulnerable to spoofing attempts.
Organizations can reduce risk by using multi-factor authentication, combining biometrics with passwords or tokens, and implementing liveness detection to confirm the user is physically present. Regular system updates, advanced sensors, and AI-based fraud detection also help identify and block spoofing attempts more effectively.


 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee