Booter
Booter Definition
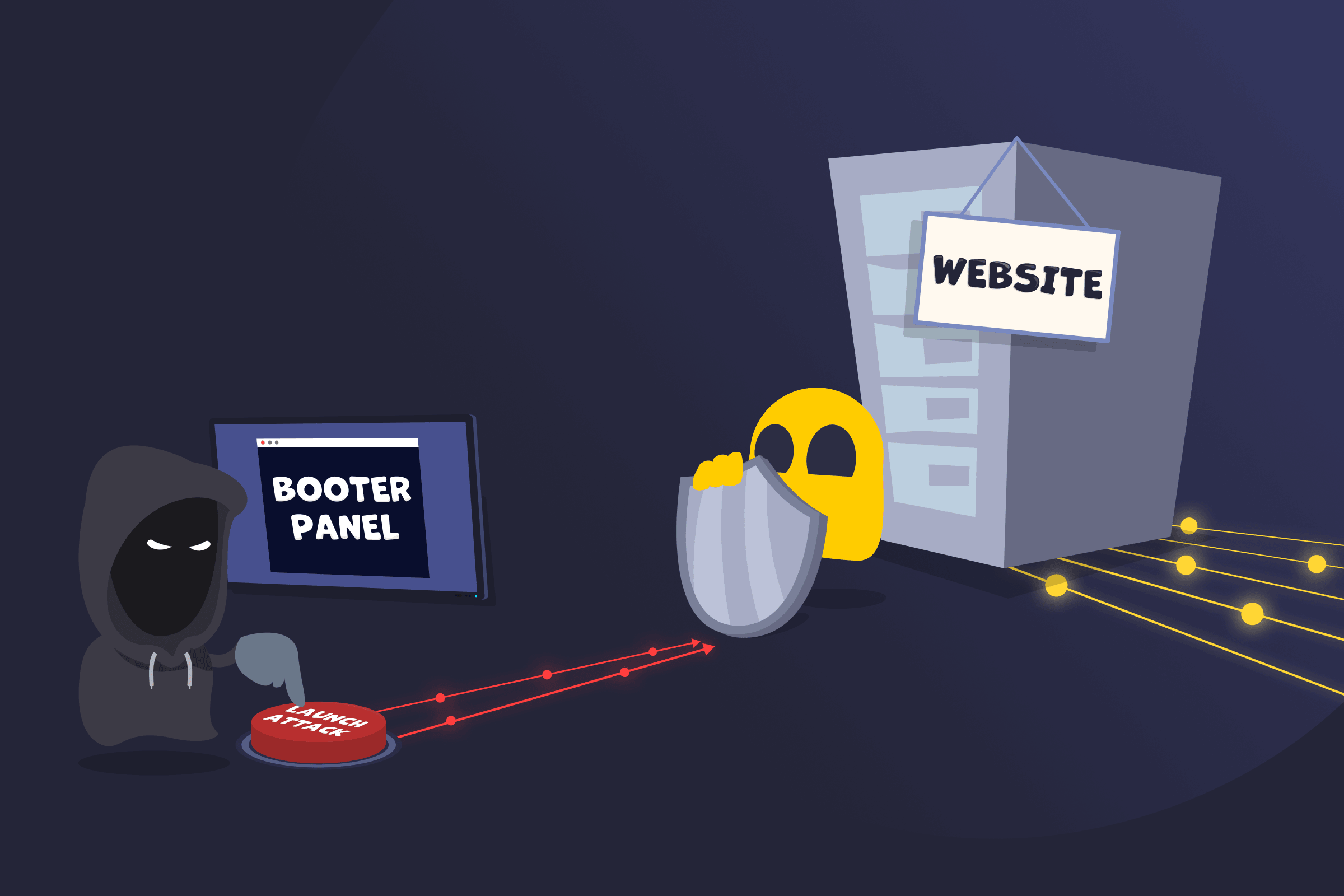
A booter is a service used to launch distributed denial-of-service (DDoS) attacks against websites, servers, or networks. It allows attackers to send large volumes of traffic to a target system, causing slowdowns or complete service disruption.
These services are often offered through online platforms that allow users to initiate attacks without building their own tools. Some providers present them as IP stressers intended for network testing, but they’re frequently associated with unauthorized DDoS activity.
How Booters Work
Booter services are designed to generate and direct large amounts of network traffic toward a target system. They typically rely on distributed sources of traffic, which may include multiple servers or compromised devices. This distributed nature makes the traffic harder to filter and increases the likelihood of overwhelming the target’s capacity.
Some services use amplification techniques, where small requests sent to external systems trigger much larger responses toward the victim. As traffic levels increase, the targeted system may experience slower performance, connection failures, or full service disruption.
What Booters Are Typically Used For
- Gaming disruption: Attacks may interrupt matches or disconnect players.
- Online harassment: Personal websites, forums, or community platforms may be disrupted during conflicts.
- Business interference: Websites may be affected during periods of high activity, such as product launches or promotional events.
- Misuse of testing tools: Services marketed for performance testing may be used against systems without authorization.
Differences Between a Booter and a Botnet
A booter and a botnet can both be part of a DDoS attack. A booter is a service that provides a way to initiate an attack, often through a web-based interface. A botnet is the underlying network of devices that generates the traffic used in the attack. In many cases, booter services rely on botnets to produce the volume of traffic required to overwhelm a target.
Read More
FAQ
The difference mostly comes down to intent. A booter disrupts a website or server by sending large amounts of traffic. An IP stresser is software used for testing how much traffic a network can handle. Network administrators may run stress tests on their own systems. When the same type of software is used to disrupt systems without permission, it’s referred to as a booter.
In many countries, launching a booter attack against a website or network is illegal. These attacks can interrupt online services and cause damage, and both operators and users of such services have been subject to legal action.
Security teams often trace booter attacks by analyzing traffic patterns, server logs, and network routing data. They can review traffic logs, server records, and network patterns to find where the traffic came from. Booter platforms may also keep payment details, user accounts, or activity logs. These can help connect an attack to the attacker. Tracing an attack can still take time, especially when the traffic passes through many different systems.
Websites can reduce the risk of booter attacks by filtering unusual traffic and blocking suspicious requests. Many use DDoS protection services to handle large spikes in traffic. Rate limiting can help, too, as it restricts how many requests one source can send in a short time. Monitoring network activity is also a good way to identify unusual traffic patterns and respond more effectively to potential attacks.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee