Container Isolation
Container Isolation Definition
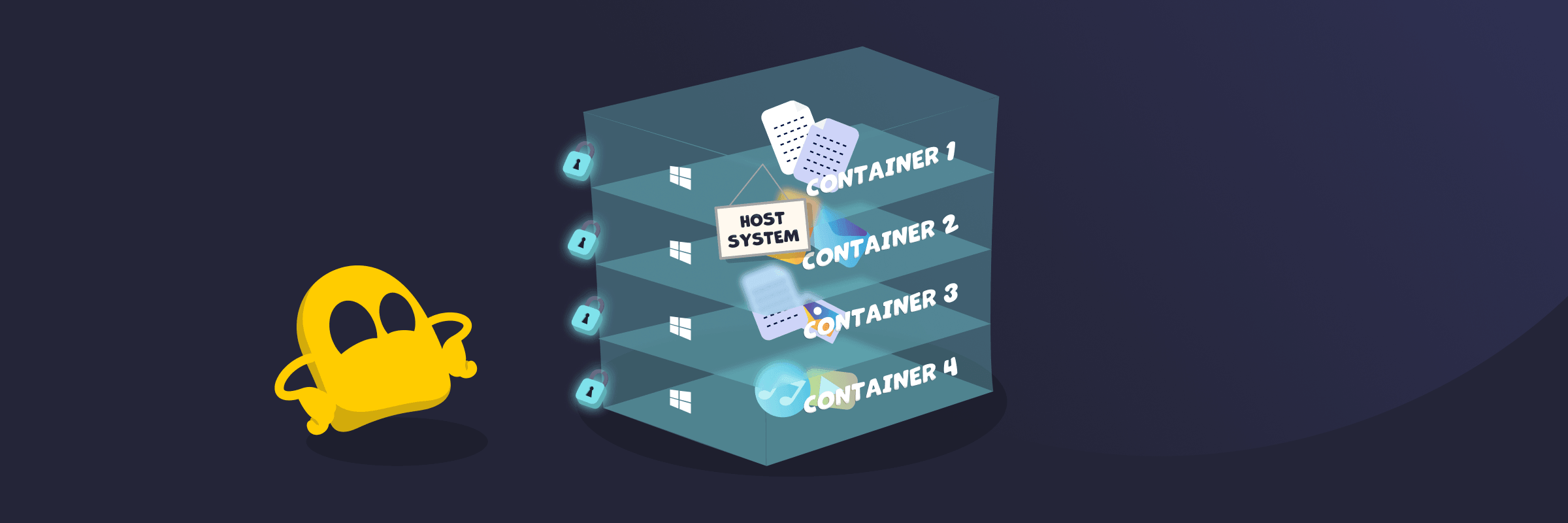
Container isolation is the practice of keeping each containerized application separate from other containers and from the host system it runs on. It ensures each container runs in its own controlled environment with limited access to processes, resources, and data outside it. This allows multiple containers to share the same operating system kernel while still acting as independent units, reducing the risk of interference or security issues.
How Container Isolation Works
Container isolation restricts what each container can access and control. The operating system kernel separates processes, file systems, and network resources so each container has its own isolated view of the system. It also limits how much CPU, memory, and storage each container can use. Permissions and security rules further control what actions a container can perform, helping maintain separation and stability across the system.
Key Components of Container Isolation
- Namespaces: Give each container its own view of the system, so it only “sees” its own processes, files, and network.
- cgroups (Control Groups): Control how much CPU, memory, and storage a container can use, preventing any single container from consuming too many resources.
- Filesystem isolation (Union/Overlay FS): Keeps each container's files separate, so changes made inside one container don't affect the host or other containers.
- Linux capabilities: Limit privileged operations within a container instead of granting full root access, reducing the risk of harmful system-level actions.
- Security modules and access controls (e.g., AppArmor, SELinux): Apply extra restrictions to control how containers interact with the system.
Container Isolation Security Benefits
- Independent execution: Applications run as separate processes in their own environments without interfering with each other.
- Restricted interactions: Containers limit communication with system resources and other containers, helping reduce unauthorized access and potential vulnerabilities.
- Defined permissions: Each container operates under specific permission settings that control which actions it can perform and reduce the risk of misuse.
- Controlled resource usage: CPU, memory, and other resources are allocated per container, helping maintain stable performance and preventing overuse.
- Issue containment: If a container is compromised, isolation helps keep it confined to that environment, reducing the chance of it spreading.
Limitations of Container Isolation
- Shared kernel risk: Containers share the same operating system kernel, so a deep system flaw can affect all of them.
- Weaker isolation than virtual machines: Containers provide less separation compared to virtual machines, which have their own OS.
- Configuration dependency: Misconfigurations can weaken isolation and expose containers to security risks.
Container Isolation vs Virtual Machines
Container isolation separates applications within the same operating system kernel, giving each one its own controlled space. Virtual machines go further by running a full operating system for each instance. This provides stronger separation, but also uses more resources.
Read More
FAQ
Container isolation improves security by keeping each application in a separate environment. This means one container can’t easily access another container’s data or the main system. If something goes wrong, the issue is more likely to stay contained instead of spreading.
Containers are separate by default and can’t directly access each other. However, they can communicate if you allow it through networks, shared volumes, or explicit configuration. This access must be set up and controlled to keep the environment secure.
If one container is compromised, isolation helps limit the damage to that container. The attacker usually can’t easily reach other containers or the main system. However, weak settings can increase the risk of the attack spreading.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee