Decapsulation
Decapsulation Definition
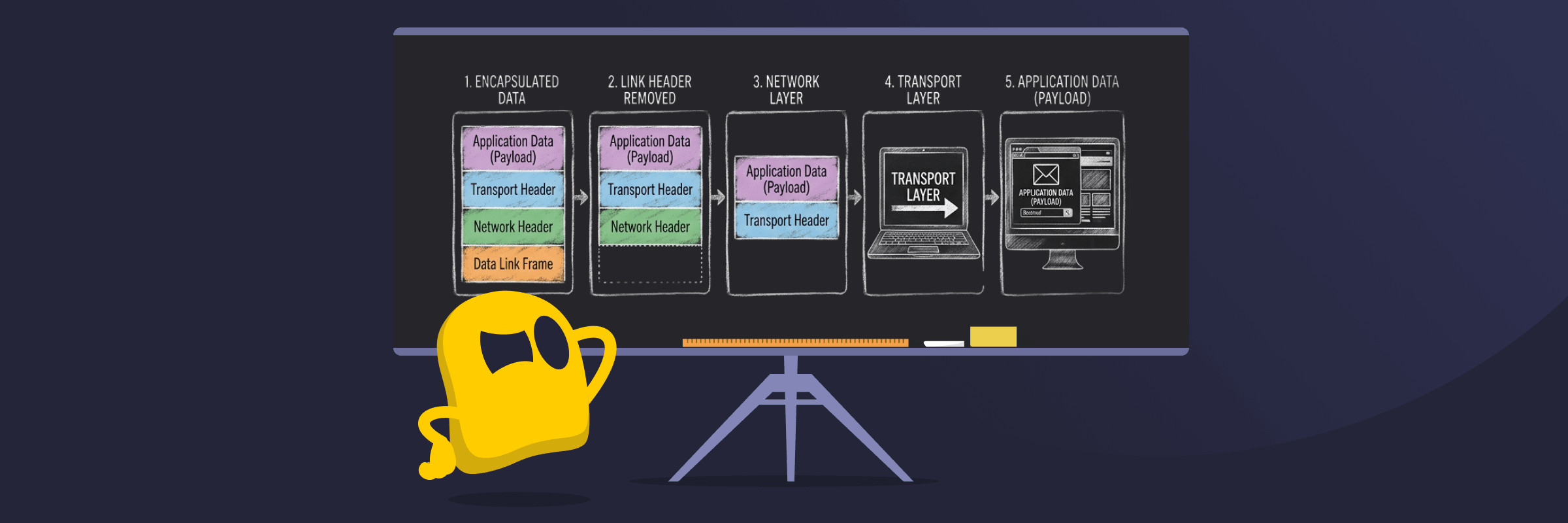
Decapsulation is the process of removing protocol headers and trailers from a data packet to reveal the original information. It’s the reverse of encapsulation and occurs as data moves through the layers of networking models, such as the OSI or TCP/IP model. Each layer removes the information it added earlier, allowing the data to be understood and delivered to the correct application.
How Decapsulation Works
When data is sent across a network, it’s wrapped in multiple layers of headers and sometimes trailers. These contain information such as addresses, routing details, and error-checking data. As the packet travels through the network, devices process only the parts relevant to them. For example, routers examine outer headers to decide where to send the packet next, but they don’t remove all the layers.
Full decapsulation typically happens at the receiving device. Each layer removes its corresponding header or trailer in sequence until only the original data remains. This final payload is then delivered to the appropriate application or service.
Benefits of Decapsulation
- Efficient packet routing: Decapsulation allows networking devices to interpret packet headers and forward data accurately across complex networks.
- Protocol compatibility: Each networking layer can process only the information it needs, allowing different protocols and technologies to work together.
- Traffic inspection and filtering: Layered processing lets firewalls, routers, and security tools examine packet contents and enforce rules or detect threats.
Limitations of Decapsulation
- Processing overhead: Every encapsulation and decapsulation step requires computing resources, which can introduce small delays in data transmission.
- Tunneling vulnerabilities: Some tunneling protocols (such as GRE or IP-in-IP) can be abused if a system decapsulates untrusted or spoofed traffic without proper validation. This may allow attackers to bypass filtering rules, spoof source addresses, or amplify attacks.
- Reduced protection after decapsulation: Once data is decapsulated, it’s no longer protected by the outer tunnel. For example, traffic inside a VPN may still be exposed if it isn’t encrypted at the application level.
Examples of Decapsulation
- Web browsing: When you load a website, your device removes network and transport headers from incoming packets so the browser can display the page content.
- Email delivery: As an email reaches your device, each network layer removes its headers until the message is passed to your email application.
- VPN connections: Encrypted VPN packets are decapsulated when they reach the VPN endpoint, removing the outer tunnel headers before delivering the original data.
- Routing through networks: Routers read and process outer headers to forward packets, performing partial decapsulation to interpret routing information.
Read More
FAQ
Decapsulation is the process of removing protocol headers and trailers from a data packet so the receiving device can access the original data. It occurs as packets move through networking layers in models like the OSI or TCP/IP.
Decapsulation is the opposite of encapsulation. Encapsulation adds protocol headers to data before it is sent across a network. Decapsulation removes those headers when the packet reaches intermediate devices or its final destination.
Decapsulation can occur at multiple points in a network, including routers, switches, firewalls, and the final receiving computer. Each device processes the packet according to the networking layer it operates on until the packet reaches its final destination, where it’s fully unwrapped.


 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee