Drdos Attack
DrDos Attack Definition
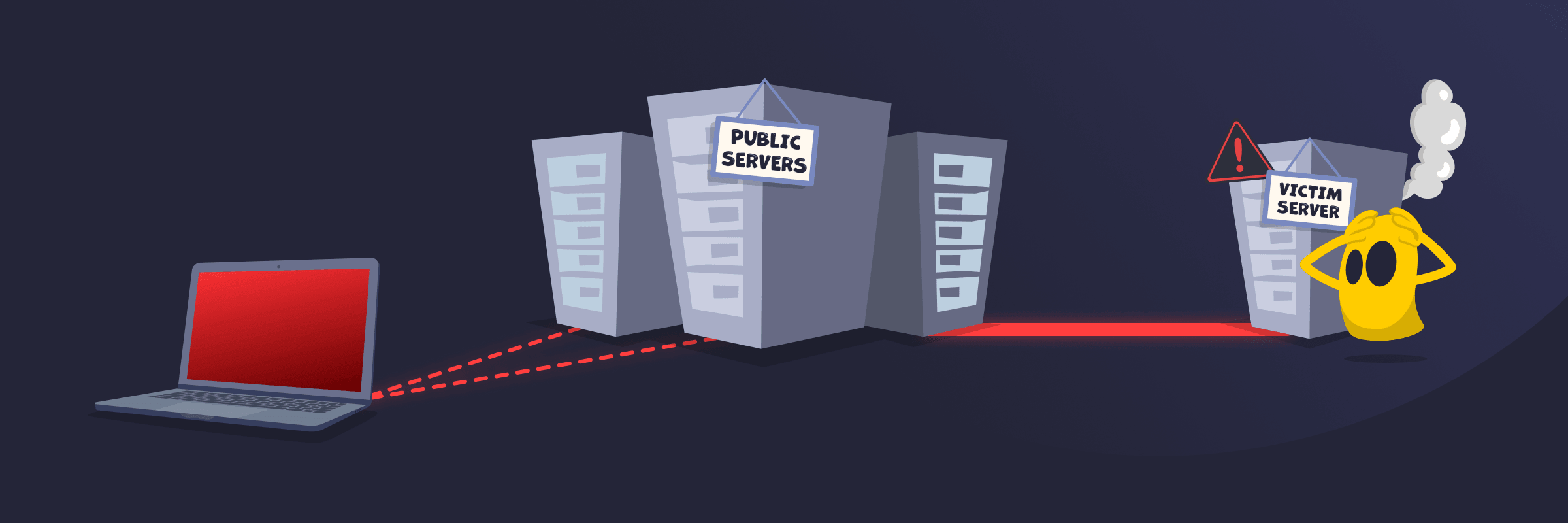
A DrDoS (Distributed Reflection Denial of Service) attack is a type of DDoS cyberattack that uses publicly reachable servers to flood a target with unwanted traffic. The attacker sends requests that appear to come from the victim’s IP address, so the servers reply to the victim instead. In many cases, the replies are larger than the requests, which amplifies the traffic and can slow down or disrupt the target’s service.
How a DrDoS Attack Works
An attacker begins by sending spoofed requests to publicly accessible services, using the victim’s IP address as the source address. The services then reply to the victim, not the attacker. Attackers often choose services that can turn small requests into much larger responses, which increases the amount of traffic sent toward the target.
When many reflectors (third-party servers that respond to the attacker’s spoofed requests) respond at once, the victim’s network or server can become overloaded. This can lead to slowdowns, dropped connections, or downtime.
Common Types of DrDoS Attacks
- DNS amplification attack: An attacker sends small DNS queries that trigger much larger responses, which then flood the target.
- NTP amplification attack: This attack abuses time servers that reply with large amounts of data, overwhelming the victim.
- Memcached amplification attack: Misconfigured memcached servers return huge data responses that quickly overload the target.
- SSDP amplification attack: Exposed UPnP-enabled devices respond to spoofed discovery requests, sending traffic back to the victim.
- SNMP amplification attack: Network management servers are used to generate amplified traffic that overwhelms the target.
DrDoS vs DDoS
A DDoS (Distributed Denial of Service) attack overwhelms a target with traffic from multiple sources, often compromised devices in a botnet. A DrDoS (Distributed Reflection Denial of Service) attack is a reflection-based version that uses spoofed requests to make legitimate servers send traffic to the victim.
The key difference is the traffic path. Many DDoS attacks send traffic directly from attacker-controlled systems, while DrDoS attacks route traffic through third-party reflectors used without their knowledge.
How to Prevent a DrDoS Attack
- Use DDoS protection services to detect and block malicious traffic before it reaches the network.
- Filter and rate-limit incoming requests to help prevent traffic spikes from overwhelming systems.
- Use anti-spoofing controls like source address validation, ingress filtering, and similar rules to help stop spoofed traffic from leaving a network.
- Disable unnecessary services and unused protocols to reduce the number of systems attackers can exploit.
- Secure and update servers to help prevent misuse of infrastructure.
- Use firewalls and monitoring tools as these systems detect unusual activity early and help stop attacks faster.
Read More
FAQ
Typical targets of DrDoS attacks include websites, online services, and organizations that rely on constant internet availability. Attackers often go after large companies, financial institutions, e-commerce platforms, gaming services, and government websites because downtime can cause major disruption and financial loss. However, smaller businesses and individual servers can also be targeted, especially if they have weaker defenses or limited bandwidth.
A VPN may reduce the risk of some IP-based attacks against an individual device by replacing the device’s visible IP address with the VPN server’s IP address. It can’t fully prevent DrDoS attacks, especially when attackers target a website, server, or network directly. In those cases, dedicated DDoS protection, traffic filtering, and network-level defenses are needed to absorb or block the attack traffic.
Companies defend against DrDoS attacks by using DDoS protection services that detect and block malicious traffic before it reaches their systems. They also use firewalls, rate limiting, and monitoring tools to control incoming traffic. Many also rely on CDNs or upstream providers to absorb excess traffic and reduce the impact, while securing servers and disabling unused services to limit exposure.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee