Egress Traffic
Egress Traffic Definition
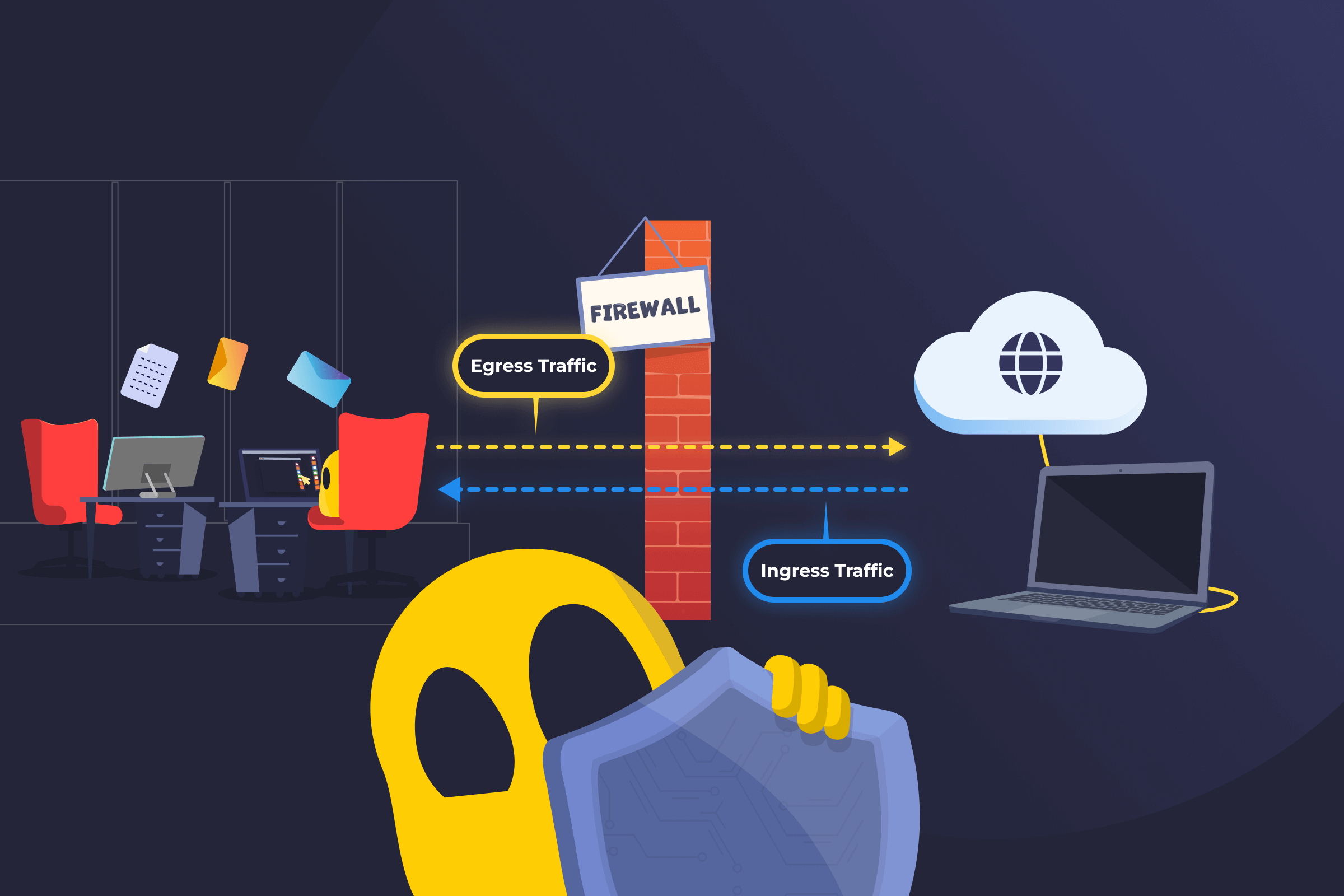
Egress traffic is the data that leaves a device, server, or internal network and travels to an external destination. This can include sending an email to people outside your organization, transferring files to cloud storage or SaaS platforms, or connecting to external websites.
Outbound data may contain sensitive information such as customer records, intellectual property, or internal communications. This means organizations should monitor and manage egress traffic to reduce security risks, maintain performance, and control costs.
How Egress Traffic Works
When a user or a system inside a network initiates communication with something outside that network, the outgoing data becomes egress traffic. Before leaving the environment, it typically passes through security controls, like firewalls, proxy servers, or secure web gateways. These controls can check whether the destination is approved, inspect traffic for privacy violations, log activity for auditing and investigation, or block suspicious and unauthorized transfers.
For example, if an employee attempts to upload a large dataset to an unknown file-sharing site, an egress control system may flag or block the action based on company policy.
Benefits of Egress Traffic Monitoring
- Detects data leaks: Helps identify unusual outbound transfers that may indicate data theft or accidental leaks.
- Improves visibility: Highlights suspicious connections to unknown or malicious destinations.
- Controls bandwidth usage: Identifies high traffic or unnecessary data transfers that can slow networks or increase costs.
- Enforces security policies: Allows users and administrators to block potentially unsafe destinations, ports, or applications.
- Limits attack impact: Prevents attackers from easily exporting stolen data from a compromised system.
- Strengthens network segmentation: Restricts which systems or internal zones can send traffic outside the network, helping contain potential breaches.
Challenges of Egress Traffic Monitoring
- Limited visibility: Encrypted traffic can reduce inspection capabilities without extra tools.
- Risk of overblocking: Strict rules may disrupt legitimate activities or critical services.
- High traffic volume: Large organizations generate significant outbound data, making monitoring and analysis more difficult.
- Complex configurations: Poorly designed policies can create gaps in protection or make operations more difficult.
Read More
FAQ
Ingress traffic refers to data coming into your network from an external source, such as website visitors, incoming emails, or downloaded files. Egress traffic is data leaving your network, such as outbound emails, file uploads, or connections to cloud services. Monitoring both directions gives a complete view of how data moves in and out of your environment.
Many cyberattacks rely on outbound communication. Attackers often try to send stolen data outside the network or connect compromised systems to remote servers for control. Monitoring egress traffic helps detect unusual destinations, unexpected data transfers, and suspicious communication patterns that may signal a breach.
Yes. Organizations can use firewalls, filtering tools, and security policies to control where outbound traffic is allowed to go and how it is transmitted. For example, they can block unapproved websites, restrict certain ports or protocols, or prevent unauthorized cloud uploads. The goal is not to block all outbound communication, but to allow only what is necessary and trusted.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee