Encapsulating Security Payload
Encapsulating Security Payload Definition
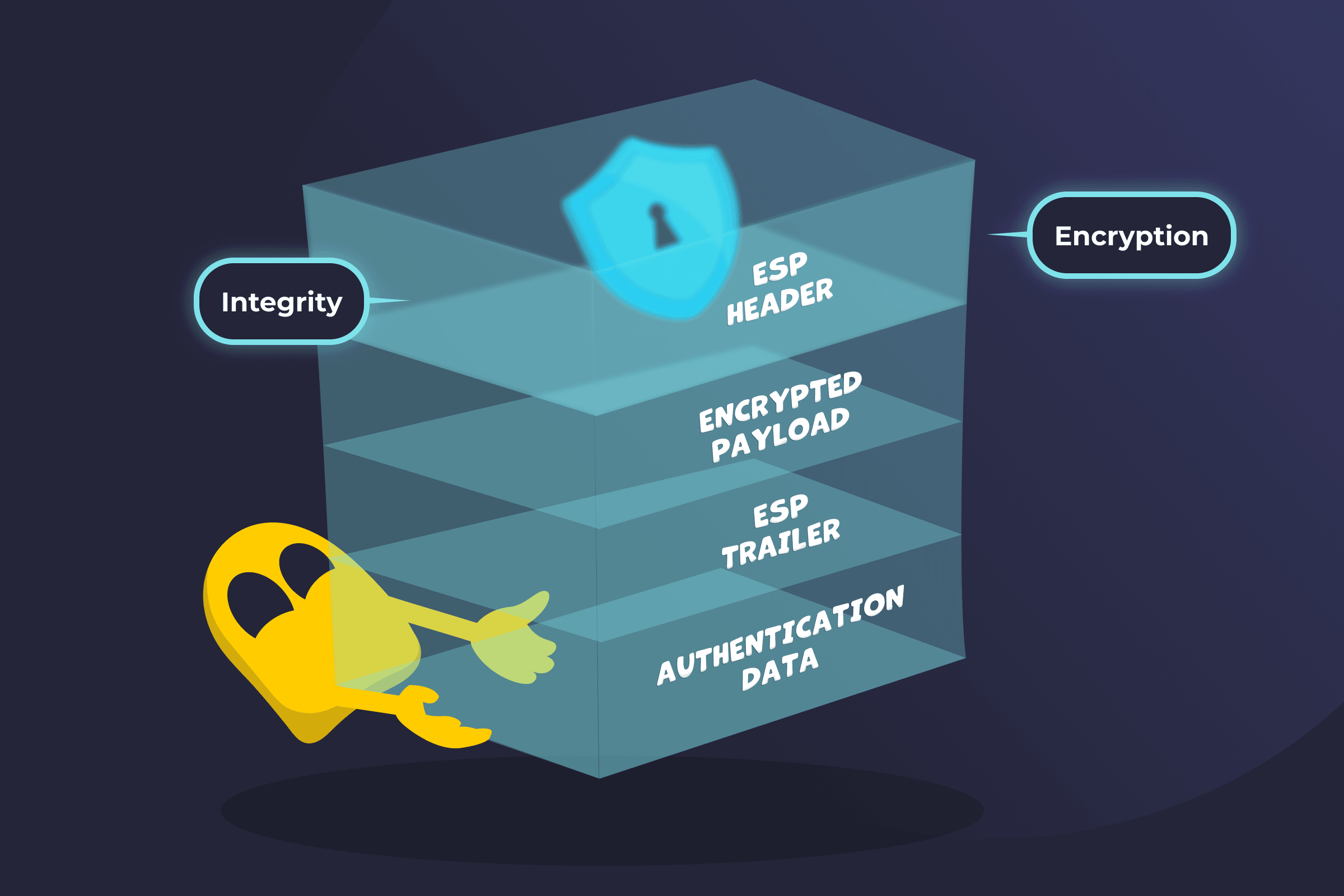
Encapsulating Security Payload (ESP) is a protocol in the IPsec suite that secures data as it travels across a network. It protects IP packets by encrypting their contents and optionally adding authentication, so only authorized recipients can read the data and verify it hasn’t been altered. ESP ensures confidentiality, integrity, and authenticity at the network layer.
How Encapsulating Security Payload (ESP) Works
- Payload preparation: ESP takes the original IP packet payload and prepares it for protection before sending.
- Encryption: ESP encrypts the payload using cryptographic algorithms such as AES, making it unreadable to anyone other than the intended receiver.
- Trailer and padding: ESP adds a trailer and padding to support encryption requirements and proper packet formatting.
- Data authentication: ESP includes integrity protection so the receiver can verify the packet has not been altered. In many modern implementations, encryption and authentication are combined into a single operation using an authentication tag.
- Sequence numbering: ESP assigns a unique sequence number to each packet to help detect and block replay attacks.
- Encapsulation: ESP adds a header to the encrypted data, creating a secure packet ready for transmission.
- Transmission: The secured packet is sent across the network to the recipient.
- Header and sequence check: The receiver checks the ESP header and sequence number to confirm the packet is valid and has not been replayed.
- Integrity verification: The receiver verifies the authentication data to confirm the packet has not been tampered with in transit.
- Decryption: The receiver decrypts the payload and processes the original data as intended.
Main Modes in ESP
- Transport mode: ESP encrypts only the data inside the IP packet (the payload). The original IP header stays visible, so the packet can be routed normally. This mode is usually used for direct device-to-device communication.
- Tunnel mode: ESP encrypts the entire original IP packet, including its header, and wraps it inside a new IP packet. This hides the original packet details, though a new outer IP header remains visible. This mode is commonly used in VPNs.
Use Cases and Applications
- VPN security: Encrypts and authenticates traffic within VPN tunnels to help protect data between connected networks.
- Site-to-site networks: Secures data flowing between separate office or branch networks over public infrastructure.
- Remote access: Protects connections for users accessing a private network from outside locations.
- Device communication: Secures direct communication between individual devices on a network.
- Public network protection: Helps protect sensitive data transmitted over unsecured or public networks.
- Cloud and enterprise networks: Supports secure data exchange across large-scale cloud and corporate environments.
Read More
FAQ
No. It only encrypts the payload of the IP packet, which is the actual data being sent. In transport mode, the original IP header remains unencrypted. In tunnel mode, ESP encrypts the entire original IP packet, but it’s still wrapped inside a new outer IP header that isn’t encrypted.
No, ESP isn’t the same as IPsec. ESP is one of the protocols within the IPsec suite. IPsec is a group of protocols used to secure network traffic, while ESP is specifically responsible for encrypting and protecting the data inside IP packets.
Yes, ESP protects against replay attacks. It uses sequence numbers to track each packet and detect duplicates. If a packet with a repeated or out-of-order sequence number is received, it can be rejected based on sequence numbers, preventing attackers from reusing captured data.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee