Key Escrow
Key Escrow Definition
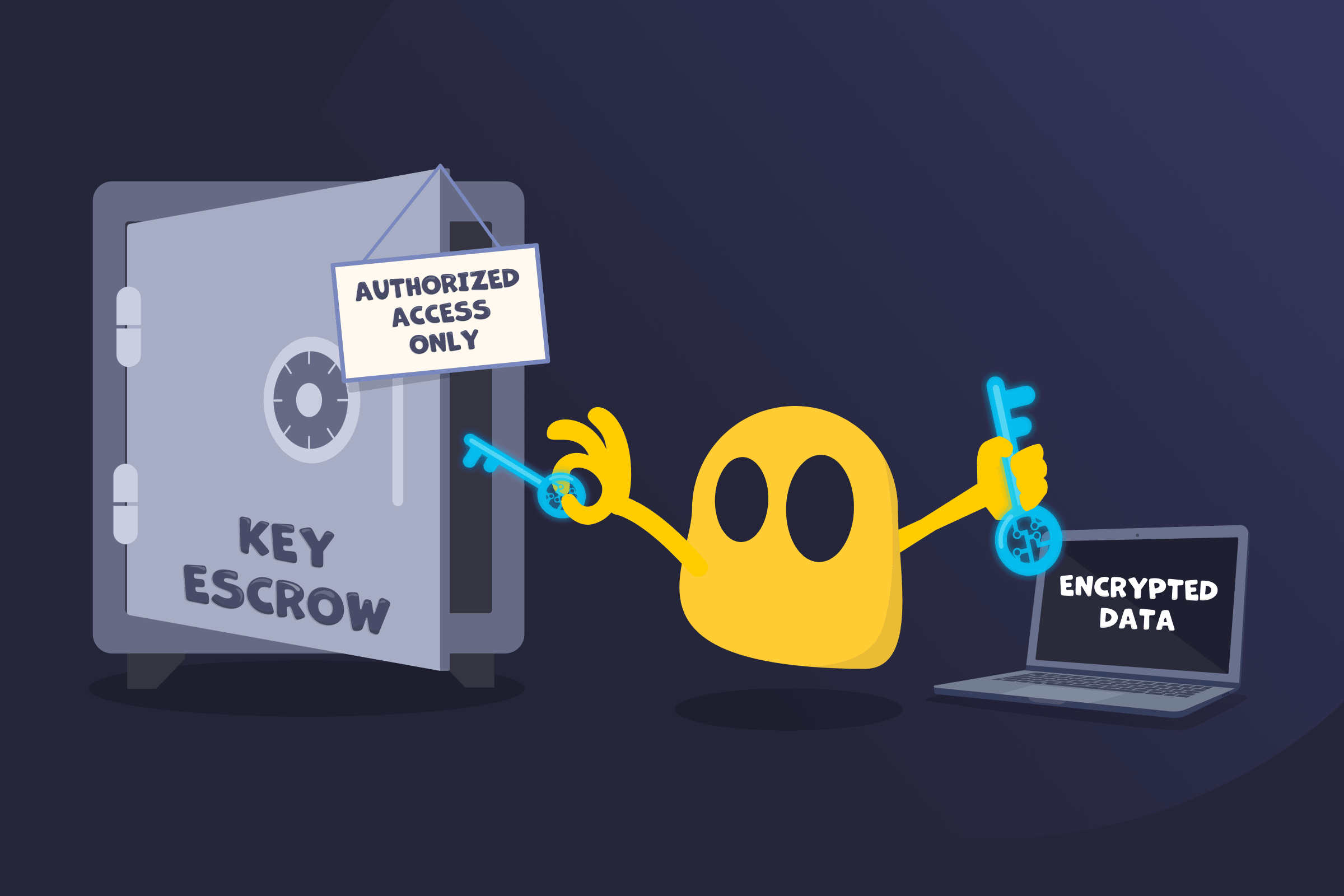
Key escrow is a cryptographic security arrangement in which a copy of an encryption key is stored with a trusted third party, known as an escrow agent. This key can be accessed only under specific, authorized conditions. Access to the escrowed key is typically protected by an escrow password, which ensures that only authorized parties can retrieve it.
Encryption keys are used to protect data by controlling how information is encrypted and decrypted. By placing a backup copy of a key in escrow, organizations can recover access to encrypted data if the original key is lost, unavailable, or otherwise inaccessible.
How Key Escrow Works
Key escrow systems follow a controlled process to store and retrieve encryption keys when needed:
- A cryptographic key is generated to encrypt and decrypt data.
- A copy of the key is securely stored with an escrow agent or key management system.
- The escrowed key is protected using encryption, access controls, and auditing mechanisms.
- An authorized party requests access to the key if the original key becomes unavailable.
- The escrow agent verifies the request and releases the key so the encrypted data can be accessed.
Why Key Escrow Is Used
- Data recovery: If a user loses an encryption key, the escrowed copy can restore access to encrypted data.
- Business continuity: Companies can access encrypted files or communications if an employee leaves, loses credentials, or becomes unavailable.
- Device and system management: IT teams can recover keys for encrypted devices, systems, or corporate accounts.
- Legal or regulatory access: In some cases, authorities may obtain escrowed keys through a lawful request to access encrypted information.
Security Risks Associated with Key Escrow
- Single point of failure: If the escrow system is compromised, attackers may gain access to multiple encryption keys at once.
- Privacy concerns: Escrow systems allow third parties to access encryption keys under certain conditions, which may expose private user data.
- Security vulnerabilities: Storing additional copies of encryption keys increases the number of places where they must be protected.
- Government access: Government agencies can request access to escrowed keys through legal processes, raising concerns about potential surveillance.
Read More
FAQ
Escrowed encryption keys are held by a trusted third party called an escrow agent. This may be a key escrow service, an organization’s internal IT or security team, or a secure key management system. The escrow agent stores the keys and releases them only when authorized conditions are met.
Key escrow can be secure if escrowed keys are protected with strong controls such as encryption and strict access permissions. However, it also introduces risk because additional copies of encryption keys are stored outside the original system. If the escrow system is compromised or misused, unauthorized parties could gain access to encrypted data.
Key escrow stores a copy of an encryption key with a trusted third party so it can be accessed under authorized conditions. Key recovery is a broader process that allows lost or unavailable encryption keys to be restored using various methods. This includes escrow systems, backup keys, or recovery mechanisms built into the encryption system.
No. Many encryption systems don’t use key escrow. Some systems, especially those that use end-to-end encryption, are designed so that only the user holds the encryption keys. In these cases, no third party stores a copy of the key, which prevents others from accessing encrypted data but can also make recovery impossible if the key is lost.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee