Masquerade Attack
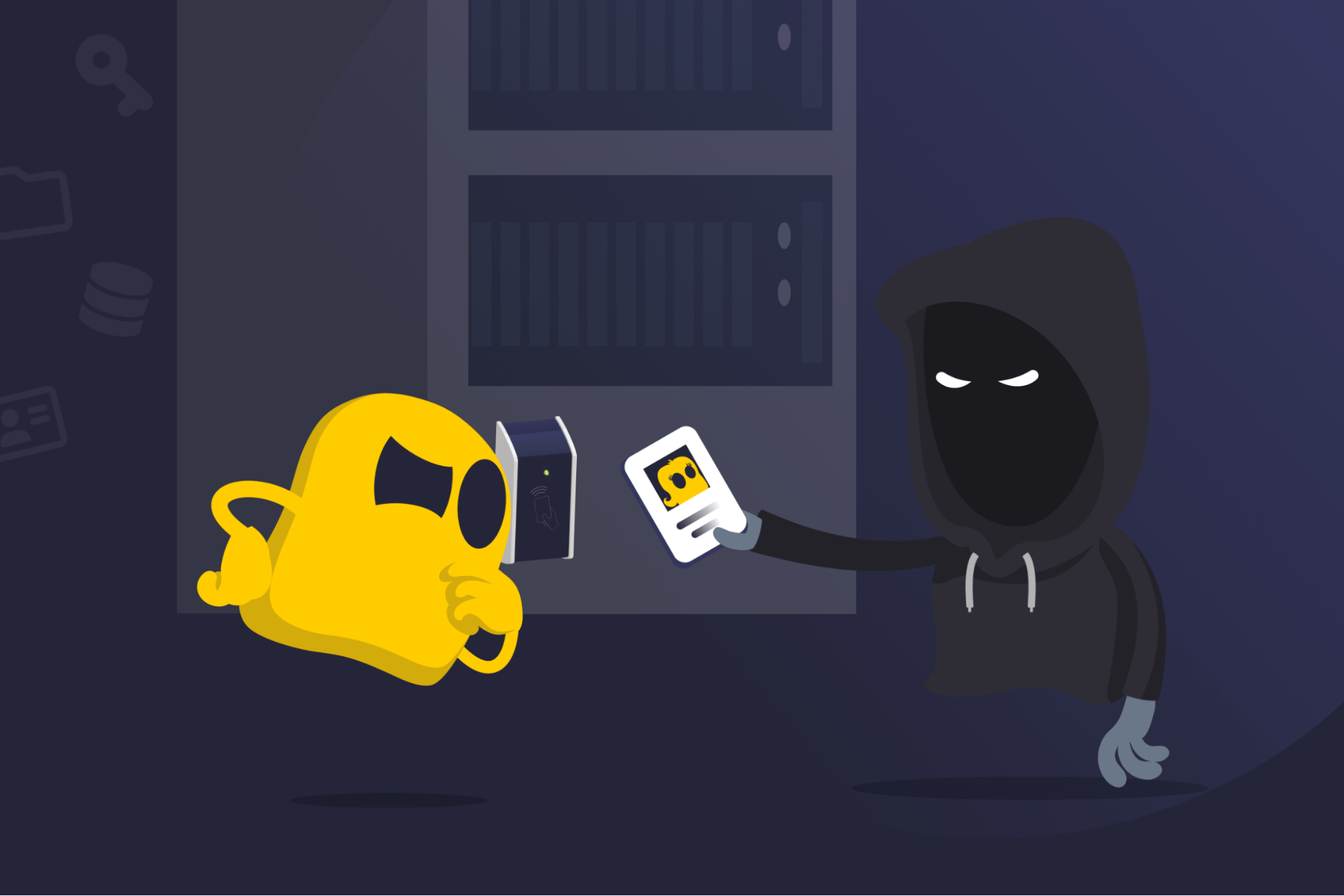
Masquerade Attack Definition
A masquerade attack is a cyberattack where an attacker poses as a trusted user or device to gain unauthorized access to a system or network. This is usually done by stealing login details, hijacking a session, or spoofing identifiers such as IP addresses. Since the attacker appears legitimate, masquerade attacks are difficult to detect and can lead to theft, fraud, or system disruption.
How Masquerade Attacks Work
A masquerade attack typically starts with the attacker gathering details, like login credentials, session tokens, or device identifiers. They can do it through methods such as phishing, malware, or exploiting system vulnerabilities.
Once the attacker has the necessary information, they can impersonate a legitimate user or device to sign in or establish a connection without triggering security alerts. With access granted, the attacker can steal sensitive data, move laterally within a network to reach other systems, or carry out fraudulent actions, like changing settings or authorizing transactions.
Examples of Masquerade Attacks
- Corporate espionage: Attackers use social engineering to trick employees into revealing credentials, then log in under their identities to access sensitive company data.
- Compromised administrator account: Cybercriminals steal an administrator’s credentials to change settings or extract large amounts of information.
- Unauthorized financial transfers: Attackers impersonate legitimate online banking users to move money or authorize fraudulent payments.
Masquerade Attack Prevention Tips
- Use multi-factor authentication (MFA) to make it harder to log in with stolen passwords alone.
- Monitor accounts and network activity using log analysis, intrusion detection tools, and alerts to flag unusual login attempts or access patterns.
- Keep software updated to help close known security gaps attackers could exploit.
- Train employees to recognize phishing and other methods commonly used to steal credentials.
Read More
- What Is a Spoofing Attack?
- What Is Spear Phishing?
- What Is QR Code Phishing?
- Identity Theft: Learn How to Stay Safe and Not Become a Victim
FAQ
A masquerade attack is considered an active attack. The attacker doesn’t just observe or collect data. They take direct action and actively log in, send messages, access systems, and more while pretending to be an authorized user.
A masquerade attack involves using stolen details to act as an authorized user within a network or system. Identity theft is broader and it describes the misuse of personal information for fraud, which may or may not include masquerade methods.
Encryption can help prevent attackers from stealing credentials by protecting your login details from being intercepted during transmission. However, if an attacker already has valid credentials, encryption can’t stop them from signing in, since the system recognizes them as legitimate users.
You should change your passwords as soon as possible, turn on multi-factor authentication, and notify the affected service or organization. Acting quickly can limit potential damage and help secure your account.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee