Secret Key
Secret Key Definition
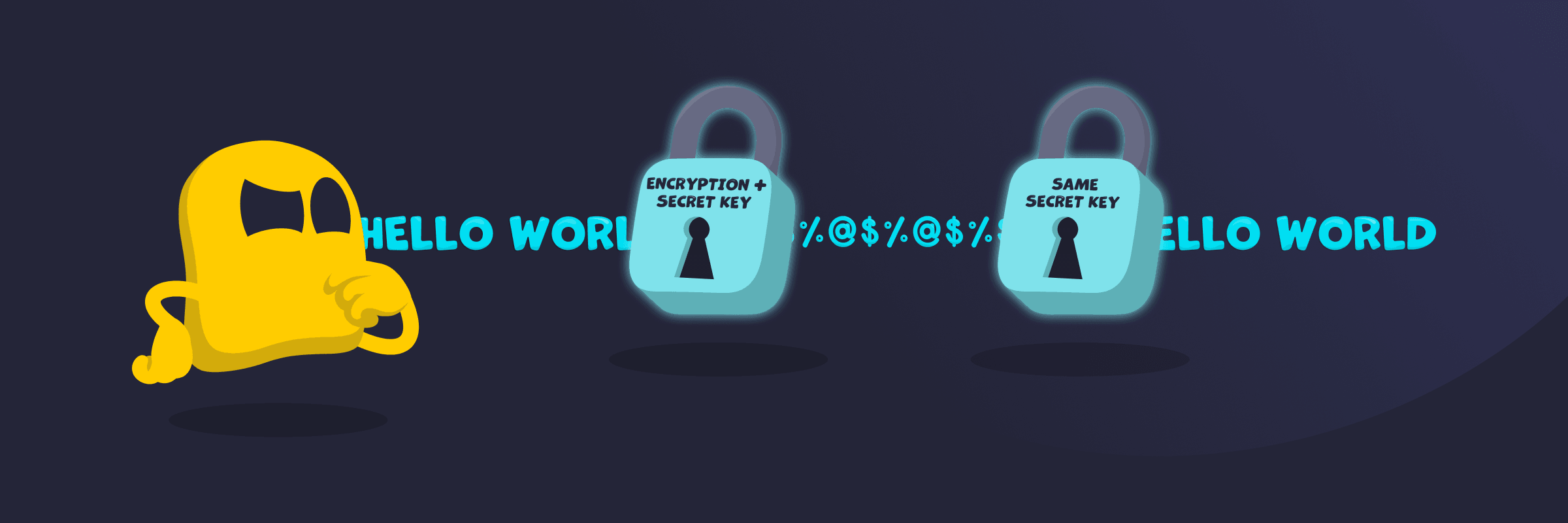
A secret key is a private piece of information used in cryptography to encrypt and decrypt data. It works like a shared code that keeps information secure, because only people who have the key can read the data. The same key is used to both lock and unlock the information, so both the sender and the receiver must keep it secret.
The key is usually a random string of characters or numbers, and the system uses it with an algorithm to turn readable data into unreadable data and back again. If someone else gets the secret key, they can access the data, so keeping it private is essential for security.
How a Secret Key Works
A secret key is used in symmetric encryption, where the same key is used to both encrypt and decrypt data. The process works as follows:
- It starts with readable data, called plaintext.
- The system applies a secret key along with an encryption algorithm.
- The data is transformed into unreadable ciphertext.
- The ciphertext is sent or stored securely.
- To read the data again, the same secret key is applied.
- The system decrypts the ciphertext back into readable plaintext.
Both the sender and the receiver must have the exact same key, and the data stays secure as long as the key remains private.
What Happens If a Secret Key Is Compromised
If a secret key is compromised, anyone who has it can access the protected data. They can use the key to decrypt sensitive information, read private communications, or even alter data without being detected. This breaks the core security of the system, because secret key encryption relies entirely on keeping the key private. In some cases, attackers can also impersonate legitimate users or systems. To fix the issue, the compromised key must be replaced immediately, and any affected data or systems should be secured with a new key.
Secret Key vs Public Key
A secret key is a single private key used in symmetric encryption. It encrypts and decrypts data, so both parties must have the same key and keep it secret. A public key is part of asymmetric encryption. It’s shared openly and is used to encrypt data, while a separate private key is used to decrypt it. The main difference is that a secret key is shared and kept private by both parties, while a public key is openly shared and works with a separate private key to secure the data.
Read More
FAQ
A secret key is generated using a random or pseudo-random number generator. The system creates an unpredictable sequence of bits or characters, making the key hard to guess. In some cases, a key can also be derived from a password using a process that adds randomness and strengthens it.
Yes, secret keys can be compromised if they are exposed, stolen, or poorly protected. This can happen through hacking, malware, insecure storage, or weak key generation. If someone gains access to the key, they can decrypt sensitive data or misuse the system. That’s why it’s important to store and manage secret keys securely.
Yes, it’s possible to change a secret key through a process called key rotation. This helps maintain security, especially if a key is exposed or has been used for a long time. However, data encrypted with the old key can’t be decrypted with the new one, so it must be decrypted and re-encrypted if continued access is required.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee