USB Drop Attack
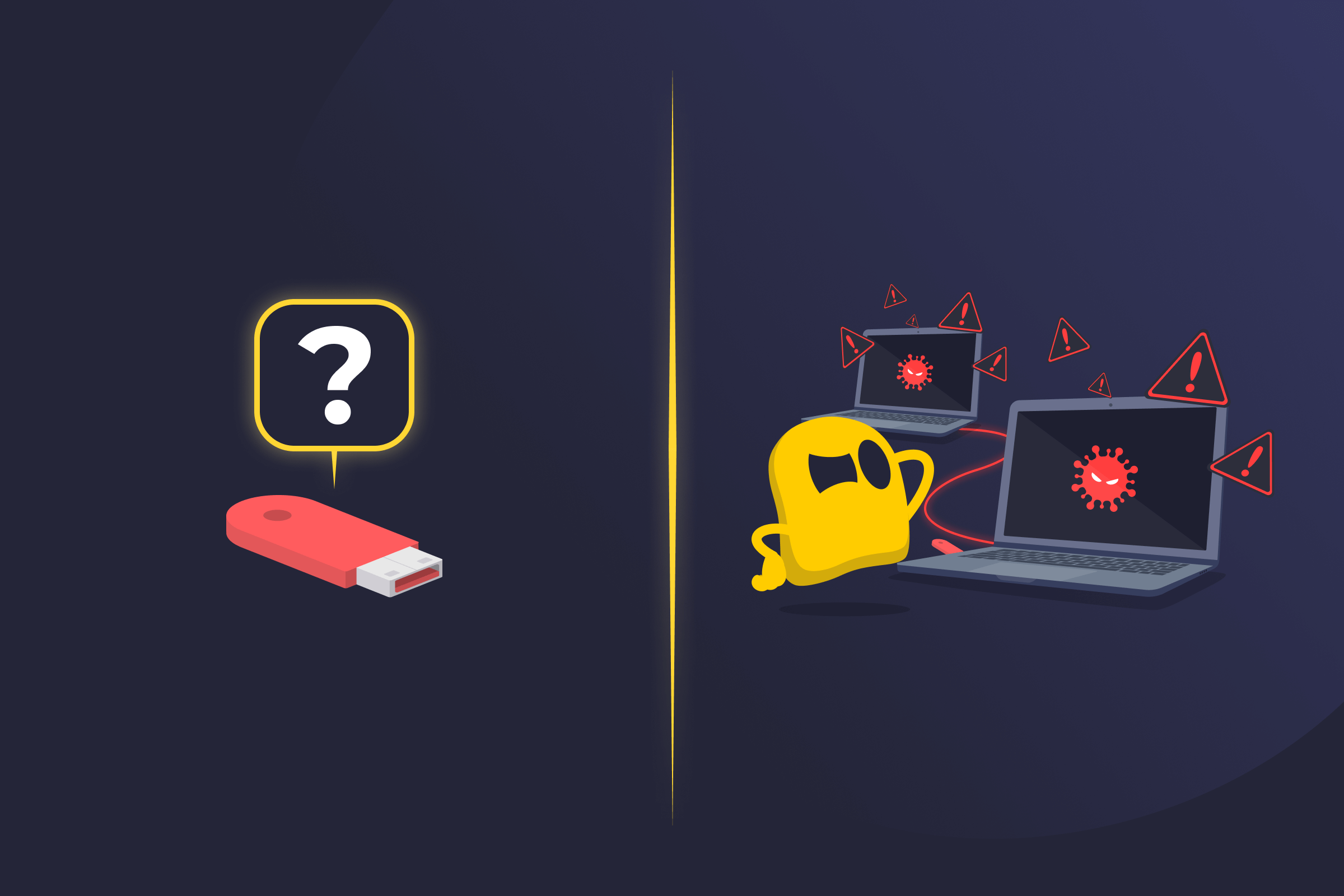
USB Drop Attack Definition
A USB drop attack is a social engineering technique in which attackers leave infected USB flash drives in places where people are likely to find them and plug them in. Instead of hacking into a system remotely, the attacker relies on human curiosity. When someone connects the USB drive to their computer, malicious software can run and compromise the device or network without obvious warning signs.
How a USB Drop Attack Works
A USB drop attack typically starts with a malicious USB drive being placed in a location where it’s likely to be found, like a parking lot, office lobby, or shared workspace. The device is often labeled in a way that suggests it contains important or sensitive information, with names such as "Payroll," “Photos,” or “Confidential.” This increases the likelihood that someone will plug it into a computer to see what’s on it.
Once connected, the USB drive can trigger malicious software, like spyware, ransomware, or keyloggers. In most cases, the code may attempt to run automatically. In others, it may rely on a user opening a file that appears legitimate. Once the malicious program launches, it can steal sensitive data, install additional files, or grant the attacker remote access. Connecting the affected computer to a larger network can expand the impact beyond a single device.
Risks of a USB Drop Attack
- Exposing sensitive information: An attacker may copy or transmit personal records, login credentials, or confidential business data without authorization.
- Allowing unauthorized access: The infected device may provide an attacker with ongoing remote access.
- Spreading malware to other systems: An initial infection can move across shared drives, connected devices, or the whole network.
- Interrupting business operations: Systems may slow down, lock users out, or become unreliable.
- Causing data loss or corruption: Important files can be modified, encrypted, or permanently deleted.
- Creating financial and reputational impact: Recovery costs, downtime, and loss of trust can follow a preventable security incident.
How to Protect Against USB Drop Attacks
- Never plug in unknown USB drives, even if they appear legitimate.
- Disable automatic USB execution to prevent software from running automatically.
- Restrict USB port access to limit which devices can connect to company systems.
- Deploy tools that scan external devices and monitor suspicious behavior.
- Educate employees and users about social engineering tactics.
Read More
FAQ
USB drop attacks are effective because they rely on normal human behavior. People may plug in a found device out of curiosity, concern, or because they want to return it to its owner. Unlike many cyberattacks, this method doesn’t require exploiting a software flaw. It succeeds when someone unknowingly gives the attacker physical access to a system.
Antivirus software can detect and block many known threats, but it won’t fully protect you. Some malware is designed to avoid detection or exploit features such as automatic file execution. Security tools reduce risk, but the safest approach is to avoid connecting unknown USB devices in the first place.
Yes. Workplaces are frequent targets because employees often use shared spaces and connected systems. An infection on one device can spread to shared drives, internal applications, or other computers on the network. Many organizations combine technical controls with employee awareness training to reduce the risk.

 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee