Shadowsocks
Shadowsocks Definition
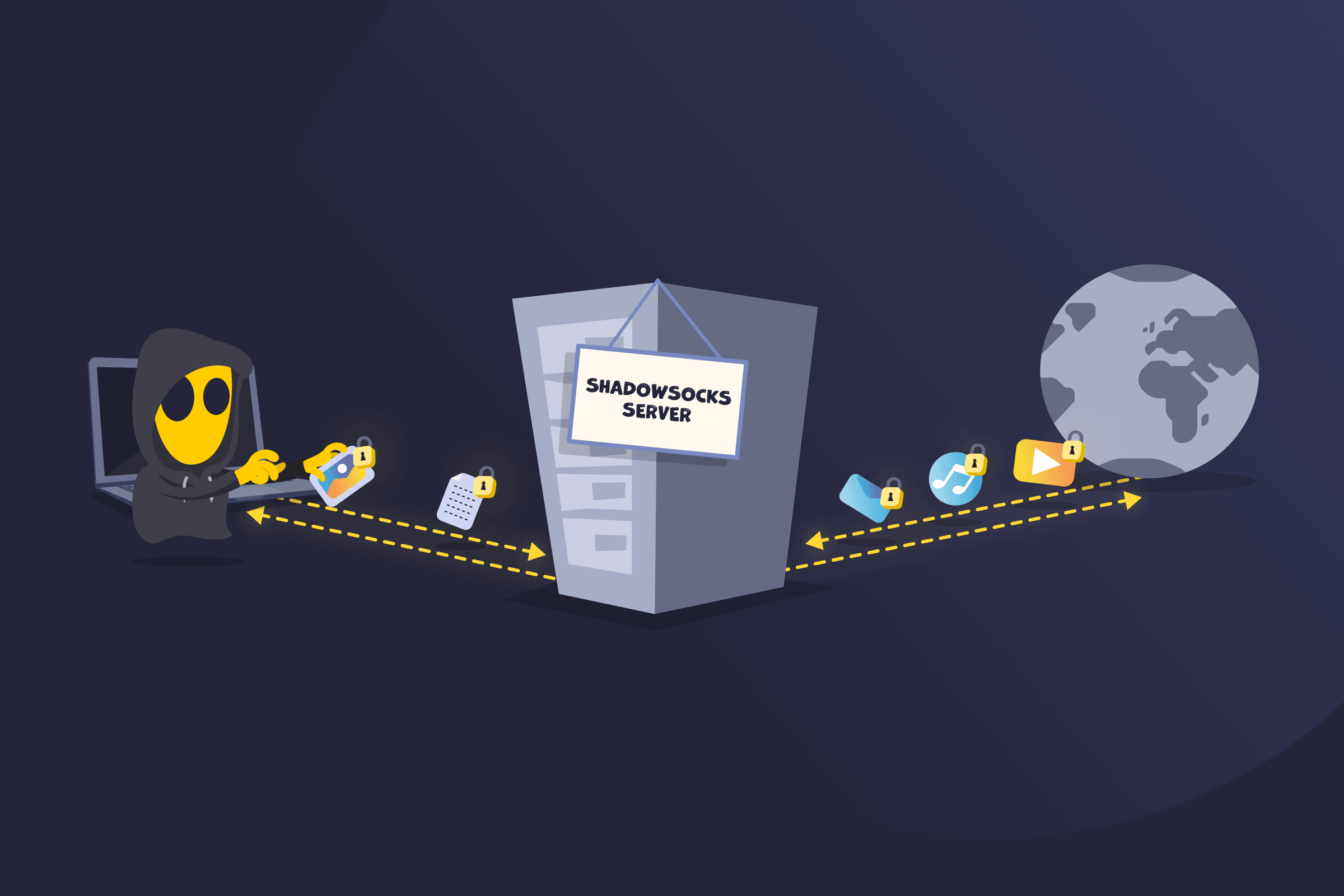
Shadowsocks is a lightweight, open-source encrypted proxy that sends internet traffic through a remote server to enable freer access to the web. It works by encrypting data packets between a device and a Shadowsocks server. The server then forwards requests to websites or services and returns responses through the same encrypted path.
It operates at the application layer, using transport layer protocols, which helps disguise traffic as normal activity. This makes it harder for networks, ISPs, or governments to detect, monitor, or block the connection, including systems that use deep packet inspection (DPI).
How Shadowsocks Works
- A device connects to a Shadowsocks client, which acts as a local proxy.
- When a website is accessed, the request goes to the client, which encrypts the data and sends it to a remote Shadowsocks server.
- The server decrypts the request and forwards it to the target website or service.
- The website sends a response back, which the server encrypts and returns to the device, where the client decrypts it for viewing.
- Shadowsocks hides traffic inside encrypted data, making it look like normal internet activity and harder to detect or block.
Common Use Cases for Shadowsocks
- More Private Browsing: Encrypts traffic between your device and the server to help maintain a more discreet browsing experience.
- Public Wi-Fi Protection: Helps protect data from exposure when connecting through shared or unsecured networks.
- Controlled Network Environments: Helps reduce network interference in environments where traffic is monitored or filtered.
- Restricted Network Access: Improves connectivity on networks where certain services or websites are filtered or blocked.
- Online Privacy: Enhances general privacy and discretion by making traffic harder to monitor or identify.
How to Use Shadowsocks Safely
- Use strong encryption and passwords: Protect the connection by preventing unauthorized access.
- Choose trusted clients and servers: Reduce risk by relying on reliable software and servers.
- Keep software up to date: Improve security by fixing known vulnerabilities.
- Use secure websites: Protect data by using HTTPS connections.
- Limit sensitive activity: Reduce exposure by avoiding sensitive actions on unsecured networks.
- Add extra protection if needed: Strengthen privacy by combining additional security tools.
Shadowsocks vs. VPN
Shadowsocks is an encrypted proxy that routes only selected traffic through a remote server and focuses on bypassing censorship by making traffic look like normal internet activity. A VPN, on the other hand, creates a secure tunnel that encrypts and routes all internet traffic through a server, boosting privacy and security for the entire connection.
Read More
FAQ
Shadowsocks is secure for protecting data in transit and making your traffic harder to detect, as it encrypts the connection between your device and the server. However, it doesn’t provide the same protection like a VPN, since it may not cover all traffic or include advanced privacy features, and its security depends on proper setup and the trustworthiness of the server you use.
Shadowsocks routes your traffic through a remote server, so websites and services see the server’s IP address instead of yours. This changes the IP address they associate with your connection. However, it doesn’t provide complete anonymity, as your IP may still be visible to the server operator and potentially to your network depending on how it’s configured.
Shadowsocks is designed to make your traffic look like normal internet activity, which makes it harder to detect than traditional proxies. However, it isn’t completely undetectable, as advanced network monitoring techniques, such as deep packet inspection, may still identify or block it in some environments.


 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee