Vampire Tap
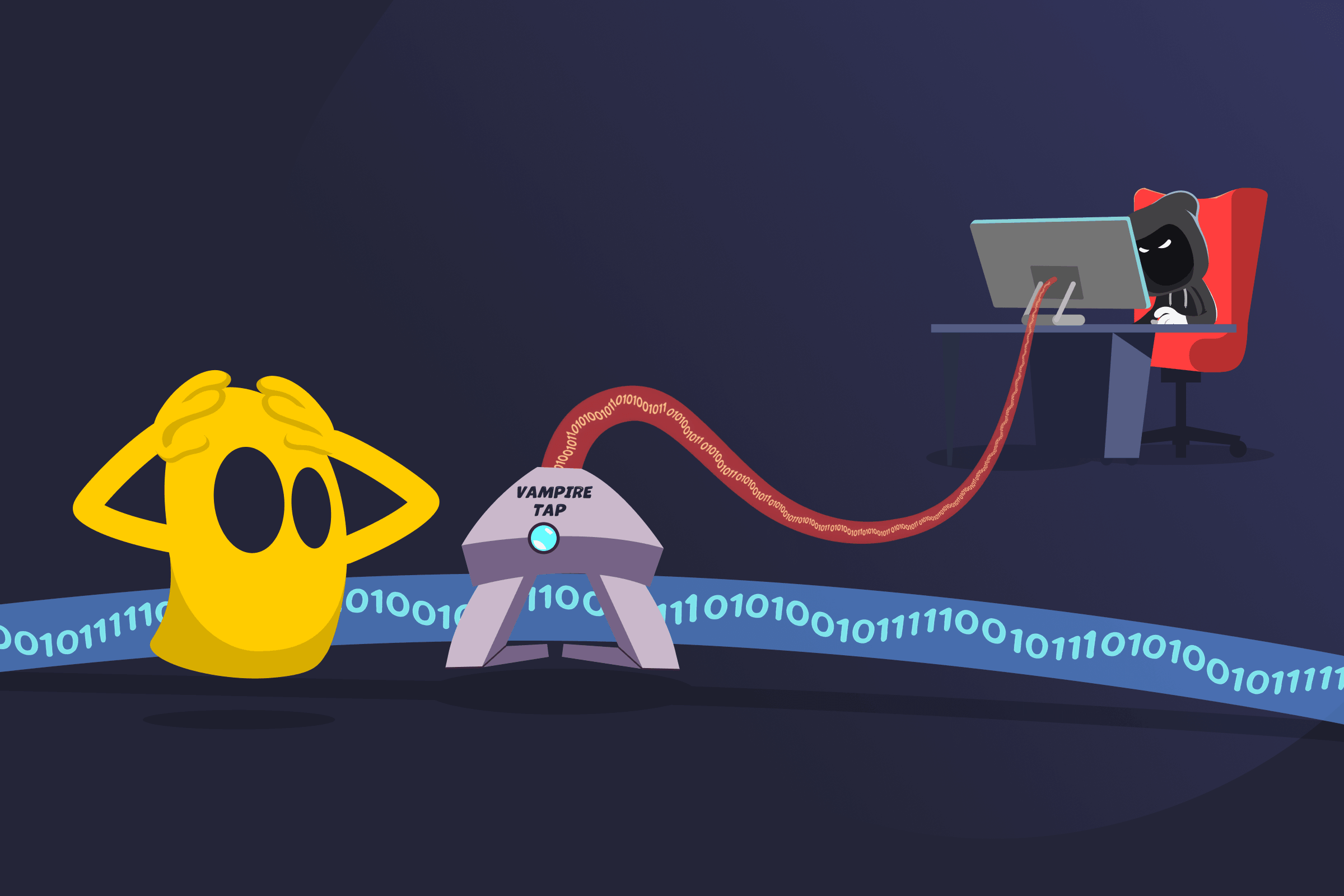
Vampire Tap Definition
A vampire tap is a device that connects to a network cable by piercing its insulation and making direct contact with the internal conductor, without cutting or interrupting the cable. It allows a device to join a network while data continues to flow normally through the cable. The connection happens without disrupting existing communication. Vampire taps were commonly used in 10BASE5 Ethernet networks to connect devices to thick coaxial cables without cutting them.
How a Vampire Tap Works
- A vampire tap clamps onto the outside of a network cable and stays firmly in place.
- A sharp metal pin pierces the cable’s insulation without cutting the cable.
- The pin makes direct contact with the inner conductor that carries data.
- The tap connects the cable to a device, such as a transceiver.
- The device can then send, receive, or monitor data while the network continues to run normally.
Advantages
- Non-disruptive connection: Connects to a cable without interrupting data flow.
- Live network integration: Adds a connection while the network remains active.
- Direct cable access: Provides immediate access to data on the cable.
Security Risks of Vampire Taps
- Cable Integrity Impact: Weakens the cable by piercing its insulation and can degrade signal quality over time.
- Unauthorized Access: Allows attackers to connect to a network cable without detection, bypassing digital security controls.
- Data Interception: Enables direct capture of data traveling through the cable.
- Network Monitoring: Allows continuous observation of network activity without the knowledge of other users.
- Detection Difficulty: Makes unauthorized connections harder to notice without physical inspection.
Best Practices for Managing Vampire Taps
Though it's impossible to cover every conceivable scenario, here are some typical precautions:
- Restrict physical access: Limit who can reach network cables and infrastructure.
- Inspect cables regularly: Check for signs of tampering or unauthorized attachments.
- Secure network areas: Use locked enclosures and controlled environments for cabling.
- Use encryption: Protect data so intercepted traffic can’t be easily read.
- Replace legacy systems: Upgrade to modern network setups that don’t support vampire taps.
Vampire Tap vs. Modern Network Connections
A vampire tap connects to a network by piercing a cable to access data without cutting it. Modern network connections use standard ports and switches to add devices safely. They don’t require physical tapping. They also support higher speeds and include built-in security features.
Read More
FAQ
No, vampire taps aren’t considered safe to use. They pierce the cable, which can weaken it and affect signal quality. They also create security risks by allowing unauthorized access to network data. Modern networks avoid them because safer and more secure connection methods are available.
You can detect a vampire tap by inspecting network cables for physical damage or unusual attachments. Look for small puncture marks, clamps, or devices attached to the cable. You can also monitor network performance for unexpected signal loss or interference. In some cases, unusual network activity or unauthorized data access may indicate that a cable has been tapped.
Yes, a vampire tap can slow down a network. It pierces the cable, which can weaken the signal traveling through it. A weaker signal can lead to errors, data retransmissions, and reduced efficiency. The added connection can also introduce interference or noise on the line. Over time, this can affect stability and cause slower or inconsistent network performance.


 45-Day Money-Back Guarantee
45-Day Money-Back Guarantee