Your computer might be infected is the most terrifying thing your antivirus can tell you. What if told you it can get worse than that?
Some cybercriminals are really smart. They can stealthily hack into your PC without alerting your system. While they poke around your device and steal your data, you won’t know until it’s too late.
This is why it’s important to keep an eye out for signs of hacking. Here are 9 signs your computer is hacked.
How to Tell if You’ve Been Hacked
We’ll start from the most obvious signs and then move to the more subtle ones.
1. You See a Ransomware Message
Picture that a pop-up is suddenly taking over your screen. You’re unable to click or close anything. You’re just able to stare at a message that lets you know your data is encrypted and you need to pay a ransom to unlock it.
Cybercriminals just infected your PC with ransomware. It’s one of the most dangerous types of infections, and it’s notoriously hard to get rid of it without compromising your data. 
Ransomware can be an incredibly lucrative business, because attackers target individuals, small businesses, large businesses, hospitals, government bodies, police stations, and even entire cities. While the Federal Bureau of Investigation (FBI) doesn’t condone paying the ransom, experts estimate that around 50% of afflicted parties do. This might incentivize cybercriminals to continue these attacks.
Ransomware messages are, by far, the most in-your-face sign of a hacked PC. The others are a bit more subtle.
2. You Find Weird Apps on Your PC
Noticed weird names in your Task Manager or Activity Monitor? Saw new files on your desktop you don’t remember putting there? Found a new toolbar you don’t remember installing? This is a huge red flag that someone else accessed your device.
We call them potentially unwanted programs (PUP) or potentially unwanted applications (PUA). They serve a wide range of purposes, like:
-
-
-
-
- Monitoring your traffic
- Redirecting your searches
- Displaying ads
- Delivering malware
- Monitoring your keystrokes
-
-
-
The most common way PUPs get on your device is through software bundles, particularly the freemium ones. This is why it’s important to read the license agreement, where it states whether the installer will download one or more programs. Check whether you can select a custom installation process, so you can opt out of the software you don’t recognize.
3. Your Traffic Is Redirected
Redirection simply means that the attacker is sending you to another URL. For example, you might google “sushi restaurant california”, and you land on an unsecure HTTP site. You can also be redirected even if you type a site’s address directly into your browser.
Cybercriminals do this for two main reasons:
- They redirect you to sites filled with ads because they make money out of advertising. For maximum profit they might build the website in such a way that it’s impossible for you not to click something there. For example, the ads won’t have a close button, or an ad will fill your screen if you try to close the browser.
- To infect you with malware. HTTP isn’t secure, so it’s easier to exploit your system’s vulnerabilities. This way, they can infect your computer with adware, keyloggers, and trojans.
4. You Get Invasive Random Pop-Ups
Invasive pop-ups are annoying and can point to a bigger problem. You might notice an increase in pop-up ads, but you’ll also see more notifications from services that don’t generally pester you. Popular examples include Amazon AWG tracking numbers, PayPal transactions, Apple limited time offers, homeopathic remedies, and adult video content, among others.
Keep in mind that legitimate services will inform you of account activity, suspicious login attempts, or offers through email, not random pop-ups.
PUPs are generally the cause for these pop-ups. Toolbars are particularly problematic, so be sure to delete any suspicious ones.
5. You’re Spamming People
Social media made it easier to distribute malware and compromise your device. Even worse, cybercriminals can use your compromised device to infect your friends, family, and acquaintances. Email is a slower but still effective way to compromise devices.
In recent years, Facebook was the most popular way to distribute malware. In what the media dubbed the Facebook virus, attackers would use your account to send messages to anyone in your friends’ list. The message includes a link to a video with text like “is this you,” “it’s you” or simply “[your name] video.”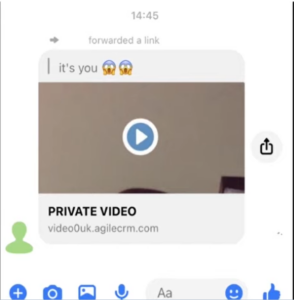
Clicking on the link leads to a bogus Facebook page that asks you to confirm your account with your password. This is how cybercriminals can access your account and lock you out.
Some people reported that clicking on the link led them to download the video, which was in fact a trojan in disguise. Later variants included a rogue JavaScript program. When someone clicked on the link, they inadvertently executed the script that compromised their accounts.
If someone has remote access to your device, you can find your accounts spamming people across different social media networks and direct messaging platforms, like Instagram and WhatsApp.
6. Your Accounts Are Compromised
Compromised accounts are a classic sign of hacking. If you find your password suddenly no longer works, you have your first red flag. If you can’t restore your password through email or phone, you can be sure a malicious hacker is to blame.
Cybercriminals are very interested in your accounts. Your social media accounts are perfect for identity theft and fraudulent scams, your eShops can make them some nice gifts, and your financial accounts are just the pot of gold. For the latter, you need to act quickly and notify your bank as quickly as possible to mitigate the damage. Block your credit or debit card to prevent charges. Depending on where you live, your local police might have a cyber incident department. If so, please consider filing a report with them as well.
You can also check if anyone leaked your data. Use CyberGhost ID Guard to check if your credentials were caught in a data breach.
7. Your Peripherals Have a Mind of Their Own
Weird peripheral behavior includes:
-
-
-
-
- Your cursor moving on its own and clicking random places.
- Your camera starts recording without a warning.
- Your microphone stealthily records you.
- USB-based flash drives transfer files without your knowledge.
-
-
-
Although it’s rare, your printer and monitors can also start displaying error messages for no good reason. This won’t be the first sign of intrusion you’ll notice because cybercrooks will wait until your PC is idle to take over it. Otherwise, you might just panic and shut down your Wi-Fi connection.
If you wake up at 2 AM and see your PC operating by itself, this is a very likely sign your device was hacked into. If you’re just surfing normally and you notice subtle changes, check for hardware issues before jumping to conclusions. Dirt trapped in the mouse can cause random clicking, and a faulty USB cable can cause your webcam to start and shut down by itself.
8. Your Antivirus and Antimalware Are Disabled
Having your security tools disabled is a huge red flag, and clear sign of intrusion. You might also notice they no longer work as intended. This includes not starting properly, shutting down automatically, or not being able to run a scan.
Unless you regularly run scans, you might not even notice your antivirus isn’t working until it’s too late. You also don’t want to ignore early signs, like your antivirus notifying you of suspicious files. Be diligent and check the files. Delete anything suspicious.
Be careful not to trust everything that seems like it comes from an antivirus solution. Attackers also famously use antivirus solutions to trick you into downloading malware. 
Fake webpages will try to mimic an antivirus solution that lets you know you have an infection. Here’s the thing. Unless you manually upload a file into the browser to check for malware, it can never know what your antivirus is doing. Your antivirus solution has its own way to send you notifications. It doesn’t need to interrupt your browsing through pop-ups.
9. Your Device Is Slow and Your Programs Crash
This is the most common symptom of a hacked PC but people often blame old devices or bad internet connections. Malware, malicious scripts, and remote control software take a lot of computational power. Because they take up so many resources, there’s not enough to go around for other software. This is why you’ll experience:
-
-
-
-
- Sluggish software
- Slow browser loading times
- Media freezing
- Software crashing unexpectedly
- Videos and online games buffering
-
-
-
If you’re on a plan with a data cap, you’ll notice you reach your allowance more quickly.
You can easily use Windows’ Task Manager and macOS’ Activity Monitor to see how much of your Central Processing Units (CPU) each app is using. For a computer sitting idle with no apps running in the background, you should be looking at maximum 10% CPU usage. Games can take anywhere from 30%-50% CPU. If an app you don’t recognize uses more than 30%, you have reason to be suspicious. An app using over 90% is a huge red flag.
How to Prevent Your Computer from Being Hacked
Prevention is better than cure, as the saying goes. This holds true for the digital world too. It is possible to prevent unwanted entry into your device, and stave off malware. Here’s how.
1. Use CyberGhost’s Anti-malware and Antivirus Solution
CyberGhost Security Suite is the perfect all-in-one app for your system security. It includes a world-class antivirus, Security Updater to check for vulnerabilities, and Privacy Guard to keep you safe from Microsoft’s trackers.
Our CyberGhost antivirus solution offers real-time protection against all manner of cyber threats like:- Malware
- Trojans
- Worms
- Spyware
- Adware
- Ransomware
- Cryptojackers
2. Use CyberGhost VPN to Encrypt Your Traffic
Get CyberGhost VPN to hide your IP address and encrypt your entire internet traffic. This adds another layer of security to your connection and helps keep intruders away from your devices.CyberGhost VPN uses 256-bit AES encryption which the US National Institute of Standards and Technology certified as an incredibly secure way to safeguard sensitive data. It’s impossible to crack with our current technology, which makes CyberGhost VPN a powerful tool to protect your online data.
CyberGhost VPN makes it impossible for cybercriminals to target you with packet sniffers, distributed denial-of-service (DDoS) attacks, or Man-in-the-Middle attacks. Better yet, you don’t need to be a tech guru to encrypt your traffic. A CyberGhost VPN subscription gives you access to easy-to-use apps for all Windows, macOS, Chromebooks, and Linux PCs.
We support other operating systems, so you can protect yourself from malicious hackers on your phone, gaming console, smart TV, and even router. You can cover up to 7 devices at the same time, so you can always protect your devices from snoopers.
3. Regularly Run Updates
Software and operating system updates can be annoying, but they contain important security fixes and patches. These make sure cybercriminals can’t exploit vulnerabilities to target your device.
Updating security tools like antivirus, firewall, or VPN solutions is also essential. You need to make sure that they recognize the latest digital threats.
Use CyberGhost Security Updater to have an easy and quick overview of your apps and which are vulnerable to security threats. From the dashboard you can choose to update or even remote outdated apps.
The Security Updater will also notify you when new updates are available, so you don’t have to constantly check every app.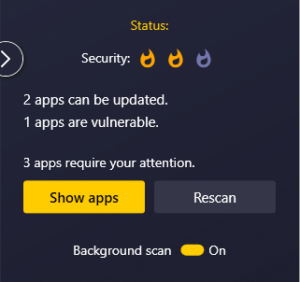
4. Enable Multi-Factor Authentication (MFA) and Login Alerts
Most services nowadays from Netflix to Google apps to banking apps notify you of login attempts through email. Don’t ignore them. Check the device, location, or even IP address where the login took place. If it’s not you, you should immediately change the password.
Always choose a strong and unique password for your accounts. You can use a password manager to store them securely.
Most importantly, enable multi-factor authentication. It’s an incredibly effective way to prevent unauthorized access. MFA falls into three categories:
- Based on your knowledge – this includes passwords, passcodes, PIN numbers, among others.
- Based on your possessions – this includes smartphones, yubikeys, USB drives, among others.
- Based on your biometric data – this includes your fingerprints, voice, or face.
The latter two are more secure.
5. Always Scan Your Email Attachments
Email phishing is still one of the common ways cybercriminals can hack into your PC. This is why you should never open suspicious emails from people you don’t know.
Unfortunately, cyber crooks are good at impersonating legitimate companies. They can also compromise your friends’ account and use their email address to further infect people. This makes you less likely to suspect anything bad is at play.
Cybercriminals send attachments that often contain malicious code that bypasses your system’s defense. It’s best to err on the side of caution and check all attachments. If your antivirus flags anything, don’t open it.
6. Back Up Your Data
Make a habit of regularly backing up your data. As we’ve seen with ransomware, there are a lot of threats out there that aim to compromise your private details. A backup can help you save your data while you plug the plug on the cyber attacker.
You can restore your device to factory settings, which wipes out everything on it including the malicious software. Afterwards restore your data from the backup. While this doesn’t guarantee that your personal information won’t be leaked, it helps minimize the damage, and helps you quickly regain access to your device and accounts.
7. Secure Your Router
Your router connects all your household devices, so you can think of it as a gateway to your digital life. Sadly, we don’t give our routers the love and care they deserve.
According to a Broadband Genie survey, 30% of people never change their router’s default password to a strong one. 51% of respondents never even checked their router’s admin panel, and a whopping 86% never updated the router’s firmware.
Routers get malware too, and they’re a prime target for network-based attacks. Stop overlooking your router security, and:
-
-
-
-
- Change its default name and password
- Regularly update the firmware
- Check what devices are connected to it
- Consider adding encryption by installing CyberGhost VPN
-
-
-
How to Clean a Hacked PC
You’ve noticed enough hacking signs on your PC? Then act quickly, before the perpetrator can do more damage.
1. Let CyberGhost’s Antivirus Solution Do Its Job
If you’re on Windows, get CyberGhost’s Security Suite. It comes with an antivirus solution that reliably keeps hacking attempts at bay. If you suspect an infection, you have 3 options:
-
-
-
-
- Quick Scan: This scans parts of your system that are normally vulnerable to threats.
- Full Scan: This scans your entire system (all apps, files, and processes).
- Custom Scan: This scans particular files you drag and drop.
-
-
-
Use the latter if you have a file you think is the culprit. Otherwise, go with the full scan option. After scanning CyberGhost antivirus will quarantine all suspicious files. You can then permanently delete all flagged threats.
CyberGhost antivirus will also notify you every time it identifies a security risk.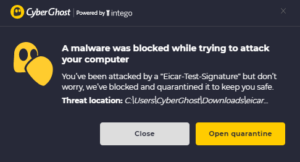
For macOS and Chromebook devices get an antivirus you trust and follow the same advice.
2. Manually Delete Infected Files
If your antivirus quarantined files, check them immediately. If you find anything suspicious, consider deleting the files.
You should run a quick Google search before deleting. Some legitimate installers are sometimes flagged, and you wouldn’t want to delete system files by mistake.
Problematic toolbars sometimes evade antivirus detection, so make sure to put your browser under the microscope. Anything you didn’t install yourself needs to go.
3. Delete Temporary Files
It’s a long shot, but some malware variants and malicious code can hide in temporary files. Here’s how.
On Windows
- Press the Windows key and R to open Run.
- Type in temp and press OK.
- Select all temporary files.
- Press the delete button.
On macOS
- Open Finder.
- Press a Shift/Command (⌘)/G combo.
- Type in ~/Library/Caches.
- Press and hold Command (⌘) and A to select all folders.
- Press Command (⌘) and Delete.
- Confirm your choice with your Mac’s password.
4. Restore Your Device to Factory Settings
If all else fails, you need to do a factory reset. Factory reset will remove all user data and return your device to its factory settings. Because this process wipes out all data, it helps remove pesky malware and intrusions too. Just keep in mind factory resets don’t remove infected files stored on backups.
Speaking of backups, if you previously backed up your data, you can restore your data afterwards. If you’re already dealing with a malware infection or unauthorized access, you shouldn’t upload a backup now. You’d just risk downloading the issues again.
It’s easy to perform a factory reset.
On Windows
- Press the Windows key and click on Settings (cog wheel).
- Select Updates and Security.
- Select Recovery.
- Under Reset this PC select Get Started.
- Choose Remove everything.
On macOS
- Select System Preferences from the Apple menu.
- Choose Erase All Content and Settings.
- Sign in with your admin account.
- A pop will ask you if you want back up your data with Time Machine. You don’t want to back up whatever lets cybercriminals in.
- Click Continue.
- Click Erase All Content & Settings.
Factory reset is different from a system restore. If you are already dealing with malware, do not perform a system restore, as it will allow the infected files to replicate.
The Bottom Line
It’s scary having someone intrude in your personal life. Digital devices have become a part of that. We went over how to detect hacking attempts, and what you can do to mitigate the risk. That said, prevention is essential and saves you a lot of headaches.
You need good security tools to protect your devices from digital threats. Don’t count on free software with basic settings to safeguard your data. Get CyberGhost VPN alongside CyberGhost Security Suite to improve your online security and keep threats at bay.
With just one subscription you get:
-
-
-
-
- Military-grade encryption on up to 7 devices simultaneously
- Real-time antivirus and anti-malware protection
- A complete overview of your apps’ security and vulnerabilities
- Control over how much data you share with Microsoft’s trackers
- Automatic notification if your email address is revealed in a data breach
-
-
-
Want to know more? Contact our 24/7 Customer Support Team for any questions you might have.
FAQ
How do hackers get into your computer?
There are several ways cybercriminals can hack their way into your device, but it all boils down to 5 execution styles.
-
-
-
-
- They exploit app and system vulnerabilities.
- They exploit unsecure connections, like on public Wi-Fi.
- They exploit device back doors.
- They use malware and malicious scripts.
- They use attacks to cripple your system’s defenses, like DDoS attacks.
-
-
-
Can your computer be hacked without you knowing?
It’s not common, but it’s possible. Most unauthorized access and remote surveillance software leave some damage behind. These are the hacking signs you can recognize. Some cybercriminals use stealthier malware variants like spyware, which can take a long time to show effect on your device. Bossware (spyware designed to monitor employees) is a type of malware that’s made to be as inconspicuous as possible. It’s virtually impossible to detect without a powerful antivirus.
Can a hacker access my computer camera, microphone, and screen?
Yes. Cybercriminals use malware like spyware to remotely access and control your camera, microphone, and screen. In fact, malicious actors often use camera and microphone recordings to blackmail people. Cyber crooks secretly record their victims during vulnerable situations like when they’re sleeping, changing clothes, or being intimate with a partner. They then ask for payment or threaten to leak the private recording to the public. It’s a problem companies take seriously. Even as recently as January 2022, Apple paid security researcher Ryan Pickren a $100,500 bounty who found a way to hack MacBook webcams.
Can a VPN stop hackers?
Not by itself, but a VPN is a great security tool to have in your arsenal. CyberGhost VPN uses 256-bit AES encryption to secure your connection. This encryption standard prevents cybercriminals from snooping on your traffic and prevents cyber attacks like DDoS and Man-in-the-Middle attacks. You can also pair your CyberGhost subscription with our antivirus solution for added protection on Windows. It comes with a risk-free 45-day money-back guarantee.
What is the best way to prevent your computer from getting hacked?
There is no single way to prevent hacking, just like there’s no single way to prevent theft. You need to take multiple steps to protect your digital identity and prevent unwanted access to your devices. Here’s a quick rundown:
-
-
-
-
- Use good security tools.
- Use CyberGhost VPN to encrypt your connection.
- Don’t skip updates.
- Enable MFA on your accounts.
- Always scan email attachments.
- Back up your data regularly.
- Secure your router.
-
-
-

Leave a comment
eman
Posted on 21/02/2023 at 17:13
thank you for the information
Ghostie
Posted on 28/02/2023 at 16:14
We’re glad to hear you enjoyed reading, Eman!