Your internet connection isn’t secure by default and considering all of the malware, scams, and hacks in the news, you’re constantly at risk. Many people turn to things like privacy browsers, proxy websites, the Tor Network, and VPNs to protect them while they browse online.
While privacy browsers and proxies provide some protection, most people choose to put their trust in either Tor or VPNs as both encrypt and reroute your connection. That means your connection is more private and adds another layer that hides your identity, but there are some key differences between the two.
What is Tor?
The Tor Browser is a private browser run by a non-profit company called The Onion Router, which shares the browser’s name. The Tor Browser can be used on your phone or computer. It encrypts your network and reroutes it through multiple points across the network, also known as Tor nodes (or relays).
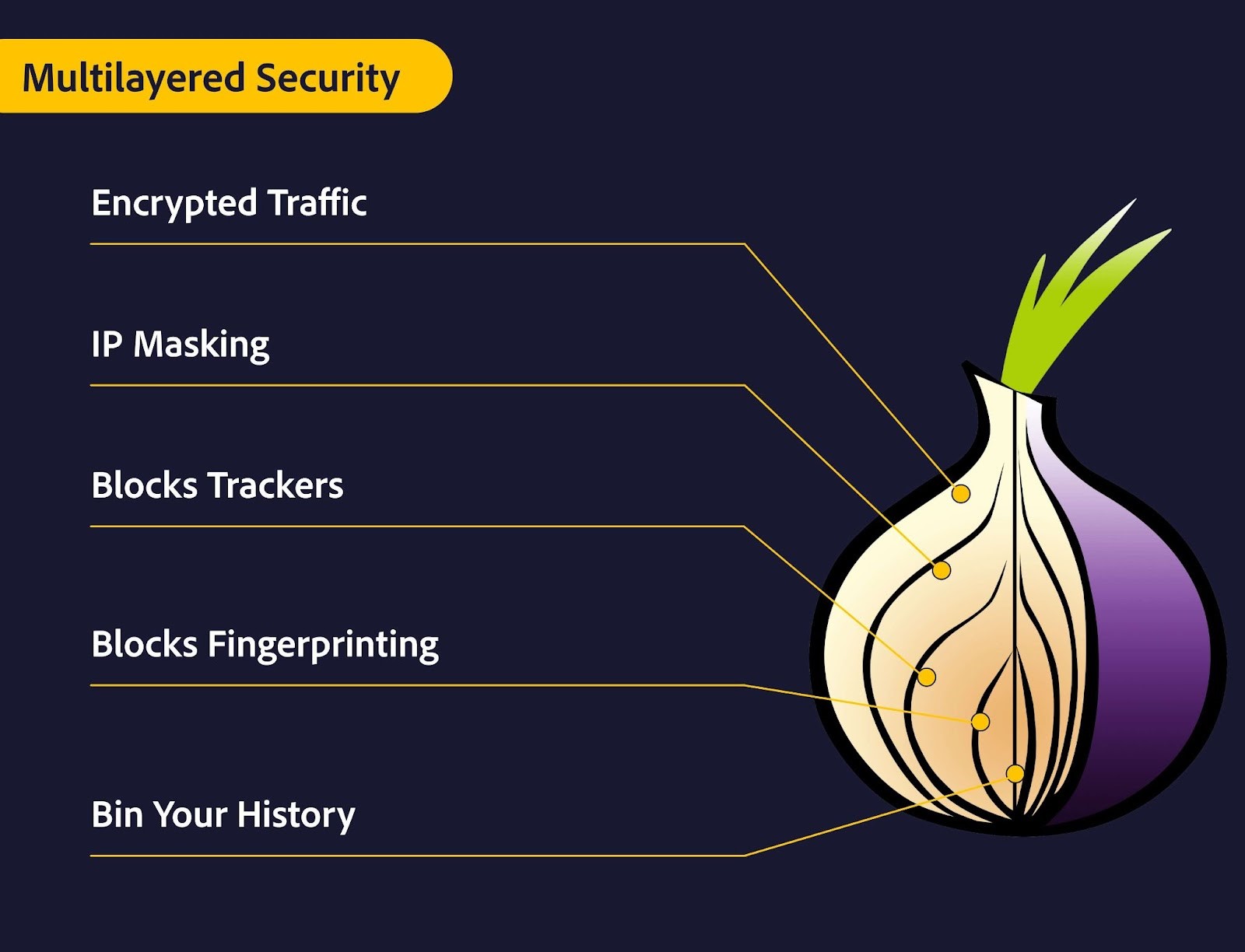
These nodes are run by volunteers around the world, who offer up their computers/servers to let people run their online traffic anonymously through them. After connecting to Tor, your connection is routed through these nodes, and your IP address changes at every pitstop. Each node only knows the IP address of the node before it, making it extremely hard to track down your real IP address.
When Do People Use Tor?
People use the Tor Browser for a variety of reasons, but mainly for extra online privacy. Some people use Tor to chat on anonymous forums or to encrypt their traffic on public Wi-Fi networks. One of the most well-known (and controversial) uses for the Tor browser is to access the dark web (.onion websites). Even though many people use the dark web for illicit activities, it is also used for legitimate reasons. For example, journalists and activists use it to protect their identities against retaliation from resentful parties.
While useful, the Tor browser isn’t for everyone. Below, I detail some of the reasons why you might want or use it or avoid it.
The Benefits and Drawbacks of Using Tor
| Benefits of Tor | Drawbacks of Tor |
| 🔐 You can browse the web anonymously with little fear that your true identity will be discovered. | 🚧 Tor is technically complicated to use. Unless you know what you’re doing, your connection can still be unsecured. |
| 🔐 Your browsing is encrypted, which lets you browse safely on open networks at cafés or the airport. | 🚧 The Tor browser only covers your online browsing. You need to apply additional complicated network configurations if you want your apps and games to run via Tor too. |
| 🔐 It’s the only way to access the dark web, which is used for legitimate reasons by many people, including scientists and journalists. | 🚧 Some ISPs don’t like it when their clients connect to Tor. Your ISP could send you a warning if they detect your activities. |
| 🔐 Ads and online companies won’t be able to track your every move online and create a digital profile with your identity. | 🚧 Tor greatly hampers your network speeds since the connection runs through multiple nodes that may be geographically spaced far from each other. |
| 🔐 Tor is free to download and use since it’s an open-source program run by a non-profit organization. | 🚧 Tor isn’t foolproof, and if the authorities or a cybercriminal is motivated enough, they may be able to discover your real identity. |
| 🚧 Some websites restrict your access if they detect you’re using Tor or make you go through multiple CAPTCHA walls every time. |
What is a VPN?

A virtual private network functions as a middleman between your network and the rest of the internet, including your ISP. VPNs are run by companies that have secure, private servers across the world. You can connect to any of these servers via the VPN client app on your device, which then instantly encrypts your connection and reroutes it through the VPN server. Your connection runs through the server first, changing your IP address, before it goes on to your ISP and the websites you visit.
Premium VPN subscriptions come with a host of additional security features, like a Kill Switch, DNS leak protection, and dedicated IP addresses. Some also provide their own device security software and privacy browser for extra added value.
Free VPNs exist, but they’re unsafe and unreliable. They can’t maintain a large and fast server base, will limit your bandwidth, and often sell your personal information and browsing data to interested parties
When choosing a VPN, look for one with a good reputation, strong No Logs policy, and additional features that suit your needs. For example, if you like to stream shows and movies, a VPN with special streaming-optimized servers is a worthwhile option. Get CyberGhost VPN and stream as much as you like in 4K quality with no bandwidth limits.
The Benefits and Drawbacks of Using a VPN
| Benefits of a VPN | Drawbacks of a VPN |
| 🎯 You can choose which VPN servers to connect to, giving you control over the IP address you get. That means you can safely access things like TV shows from home even if you’re on holiday in another country. | 💰 A good VPN isn’t free. Premium VPNs require a subscription that can be paid monthly or annually. On the other hand, you get what you pay for. |
| 🎯 Your online activity is fully encrypted, which lets you browse safely on open networks at cafés or hotels. | ⚠ Some VPNs log your personal information and browsing history. Unless you’re careful to choose a No Logs VPN, your data may be at risk. |
| 🎯 Your connection is private no matter what you do – whether you choose to browse the web, stream TV shows, or play online games. | ⚠ If the VPN is situated in any of the five/nine/fourteen-eyes countries, it may be forced to collect and hand over your data. |
| 🎯 You can quickly install VPN apps on any of your devices, and get instant coverage. They’re also extremely easy to use. | ⛔ Sometimes, streaming services detect and block known IP addresses from prominent VPNs. A good VPN will have ways around this, though. |
| 🎯 A VPN can improve your connection speed and ping in online games if the connection is rerouted on a better pathway than before. | ⛔ VPNs aren’t legal everywhere. Your country, school, or workplace may have rules/laws against VPN use that can get you in trouble. |
| 🎯 You can access better deals and avoid location-based price gouging when shopping online. |
Tor vs. VPNs
Despite the fact that both encrypt and reroute your network connection, there are many key differences between a VPN and Tor. The main thing to keep in mind is that Tor focuses on making you more anonymous online, while a VPN enhances your device’s security and privacy, and enhanced privacy is a side-effect of that process.
That means, both have their strengths but they aren’t meant to be used for the same reasons. Your own personal needs should guide you in choosing between Tor and a VPN. Let’s quickly explore which option might be better for you:
When to Use Tor
-
-
-
-
- Get robust anonymity. Tracing the connection back from the last public Tor relay to your network is extremely hard. It would take a dedicated and knowledgeable person or group to find your real identity.
- Bypass censorship and geography-based blocks. Tor provides full access to websites and other tools that are blocked in your country.
- Access the dark web. You can only access the dark web through the Tor browser.
- Gain a free browser-only privacy tool. If you just want to redirect and encrypt your browsing activity for free, then Tor is a great option.
- Safely browse on public Wi-Fi networks. Your connection is encrypted so you can safely browse on your phone or laptop while connected to a public network like in a hotel.
- Change to a random IP address. You don’t have control over which exit relay your connection goes through with Tor. It’s a great tool if you don’t care about which IP address you get.
-
-
-
When to Use a VPN
-
- 👍 Choose your own IP address location. If it’s important that your IP address is from a specific location, then a VPN is a more suitable choice.
- 👍 Increase your privacy and security on every device. Tor only works on your browser, but a VPN covers all of your apps and works with most devices, including your Smart TV and gaming consoles.
- 👍 Gain improved privacy online. Your true identity is automatically hidden with a VPN because it encrypts your connection and changes your IP address.
- 👍 Watch shows from the streaming platform of your choice. As you get to choose your IP address, you can keep using streaming services and other media, even if you’re at work or traveling abroad.
- 👍 Improve your online gaming experience. Your connection is rerouted on a different path, potentially with fewer stops. That can shorten the path it has to travel, which lowers your ping and eliminates latency and lag.
- 👍 Safely use public Wi-Fi networks. Your connection is encrypted so your devices are protected from outsiders when you use public networks like at hotels and restaurants.
- 👍 Get access to better deals. Many online retailers, hotels, and airlines make use of dynamic pricing. They change the price you see based on your location, browsing history, and device. A VPN levels the playing field because retailers can’t see your browsing history and you get to change your location. Sign up for CyberGhost VPN and keep online retailers from taking advantage.
As you can see, both are great at what they do, but they serve different purposes. If absolute anonymity is essential or you want to access the dark web (also known as .onion websites), then using both Tor and a VPN together might be the best option for you. Keep in mind this method will slow down your connection even more.
Tor-Over-VPN vs. VPN-Over-Tor
The Tor Network only protects your connection while it’s being sent from one node to another. Once your connection exits the last node, it’s not encrypted anymore. Those who know how can set additional safeguards to protect their identities when their connection reaches the exit node. The simplest way to do that is with a VPN, but there are two different approaches.
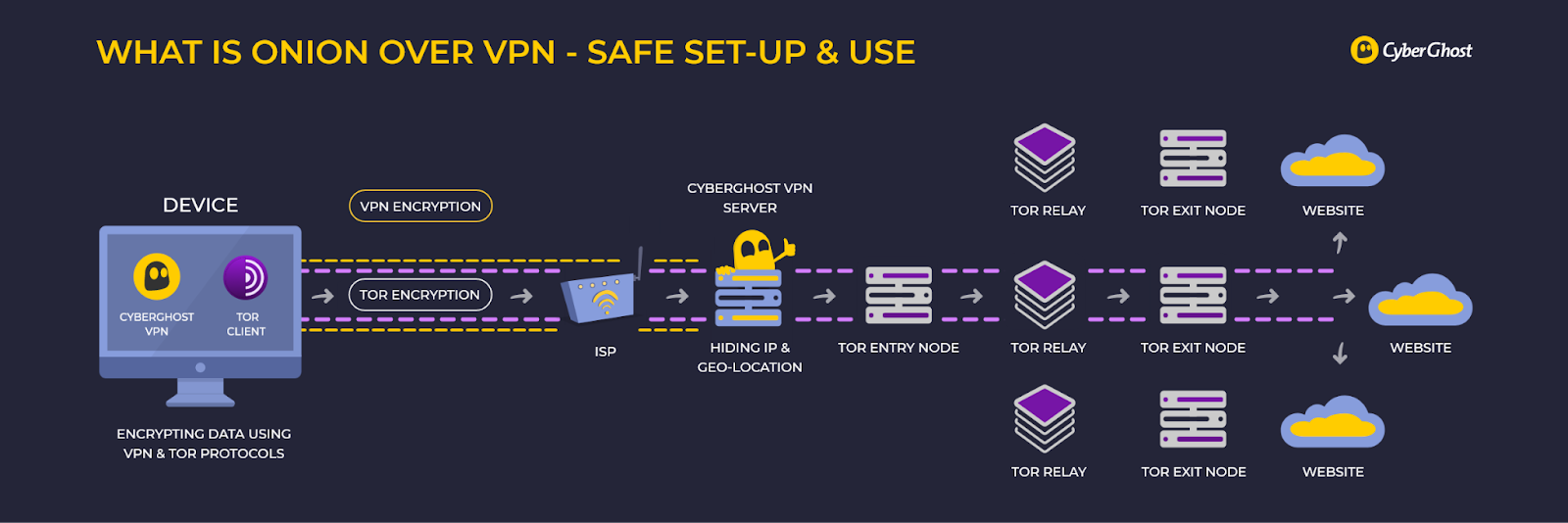
What is Tor-Over-VPN?
This is the method most people use because it offers additional privacy and identity protection while you’re connected to the Tor Network. You connect to the VPN first and it encrypts your connection before you enter the Tor network. That means when your connection exits the network, it’s still encrypted by the VPN.
This method bypasses your ISP entirely so your real IP address never touches the internet. That means your ISP also won’t be able to see that you’re connecting to the Tor network. You also get the benefit of websites not seeing that you’re using Tor so they won’t block you.
What is VPN-Over-Tor?
This method requires that you connect to Tor first and then your VPN provider. It’s a more complex process but makes it impossible for the exit node to read your traffic whereas with the other method it can.
We don’t recommend using the VPN-over-Tor approach because it doesn’t increase your anonymity and reintroduces trust in an otherwise trustless system. That means you’ll have to trust that your VPN isn’t logging your information, whereas, with the other method, it doesn’t matter as much. You also won’t be able to connect to .onion websites using this method.
That said, you don’t need a VPN for Tor. Regardless of the method you choose, this is a security measure that’s unnecessary for most people. You’re generally better off just using either Tor or a VPN separately.
Your Ultimate Tool for Privacy and Security: CyberGhost VPN
Your VPN should work for you, whether you want to watch TV shows on multiple streaming services, escape censorship, or increase your online privacy and security. CyberGhost VPN is a premium VPN, which means it isn’t free like Tor, but you get a lot of additional features.
Here are some of the privacy and security features you get with CyberGhost VPN:
-
- 💪 Enhanced privacy with 256-bit AES encryption
- 💪 Unrestricted access to thousands of servers across 91 countries
- 💪 Ultra-secure NoSpy servers
- 💪 Robust VPN protocol options
- 💪 Absolute no-logs guarantee
- 💪 Automatic kill switch
You also get access to these additional benefits:
-
- ⮕ Generous 45-day money-back guarantee (against 30-day industry standard)
- ⮕ Fast speeds with no bandwidth limits
- ⮕ Instant access to specialized streaming-optimized servers
- ⮕ Full support for all operating systems (Android, iOS, Windows, macOS, and Linux)
- ⮕ Complete support for up to 7 simultaneous devices
- ⮕ Optional secure dedicated IP address
- ⮕ Helpful 24/7 customer support
FAQ
Do I need both Tor and VPN?
Unless you’re very concerned with staying completely anonymous online, you likely don’t need to use both Tor and a VPN. CyberGhost VPN offers you everything you need to keep your connection private and secure. You also get the added benefit of having your device’s entire network connection encrypted and rerouted instead of just your browsing session. CyberGhost VPN supports all major operating systems including Android, iOS, Windows, macOS, and Linux.
Which is better – Tor-Over-VPN or VPN-Over-Tor?
Tor-over-VPN is the recommended way to use Tor with a VPN. You connect to the VPN first and then use the Tor browser. That approach provides additional privacy since your connection is encrypted before and after your exit the Tor nodes. The VPN-over-Tor approach is considered less secure. CyberGhost VPN works well with the Tor Browser and offers additional security benefits like a Kill Switch and ultra-secure NoSpy servers.
Which is safer – Tor or VPN?
A VPN is much safer to use for most people than the Tor network because Tor requires extra technical knowledge to safeguard. VPNs just require that you install an app and connect to a VPN server. A VPN also protects your whole device, while the Tor browser only protects your browsing session. CyberGhost VPN offers thousands of secure servers spread across 91 countries, so you can keep your true IP address anonymous at all times.
Is Tor illegal?
Tor isn’t illegal to use, but many ISPs frown on its use and may send you a warning. Authorities may also start taking a closer look at your online activity because Tor is often used for illicit activities. Some websites also block access from connections that go through Tor.
If you’re concerned, try CyberGhost VPN instead. You still get online privacy and security (for your whole device and not just your browser) and you’ll be much less conspicuous. CyberGhost VPN has a robust No Logs policy so your personal information stays yours alone.
Can you be tracked while using Tor?
Authorities and skilled groups/individuals may be able to track your connection through Tor under the right circumstances. The person running the exit node will also be able to see all of your online activity. Your connection after exiting the last Tor node isn’t encrypted either. If you aren’t careful, you can reveal personally identifiable information that others can use.
You can get better privacy if you use CyberGhost VPN to encrypt your connection before and after it exits the last Tor node. CyberGhost VPN uses ultra-secure 256-bit AES encryption.
Does Tor hide an IP address?
Tor hides your IP address by encrypting your connection and sending it through multiple Tor nodes (or relays). Your IP address will change to the same IP address as the last (exit) node before going on to your destination website. Although Tor only does this for your browsing session.
Any apps and other network services on your device will still use your IP address. Use a VPN like CyberGhost VPN to hide your IP address instead if you want your entire device covered. Easily test CyberGhost VPN’s privacy features for yourself with our 45-day money-back guarantee.
Why do criminals use Tor?
Criminals use Tor to hide their true identities as well as to access the dark web (.onion websites). Not all activity on the dark web is illegal, but it is easier for cybercriminals to get away with illicit activities there. Because of that, authorities may monitor anyone that uses Tor more closely.
If you want to change your IP address and gain extra privacy but don’t want the headache of using Tor, try CyberGhost VPN instead. Reach out to our 24/7 customer support team if you have any questions.

Leave a comment