Requests for user data arrive regularly. Copyright holders send DMCA notices, law enforcement agencies submit inquiries, and other authorities reach out asking whether online activity can be tied back to an individual.
This transparency report covers the requests CyberGhost received between October and December 2025, how we classify them, and what happens when they reach us. We’ve also included an update from our bug bounty program, along with a brief look at security stories from the wider internet that shaped the quarter.
Legal Requests — Our Q4 Numbers
We publish this data every quarter so you can see exactly what kind of legal requests we get and why they go nowhere.
These fall into two categories:
- DMCA complaints: Sent by copyright holders who claim that one of our IP addresses was used to share protected content without permission.
- Police requests: Submitted by law enforcement agencies asking for user data linked to an IP address associated with unlawful activity.
| October | November | December | |
| DMCA Complaints | 18,378 | 17,506 | 20,169 |
| Police Requests | 1 | 0 | 1 |
We review every request, but the outcome is always the same. Our no-logs policy means we do not collect or store any information about what users do online. Our servers are built without persistent storage. They run on RAM and reset regularly, leaving no data behind. We are also under no legal obligation to retain user information. Even if compelled, we would have nothing to provide.
With that said, let’s have a look at the numbers.
DMCA Complaints
| October | November | December |
| 18,378 | 17,506 | 20,169 |
Compared to Q3, the number of DMCA complaints dropped slightly, from 86,975 in Q3 to 56,053 this quarter. That’s still tens of thousands of takedown attempts, all hitting the same wall.
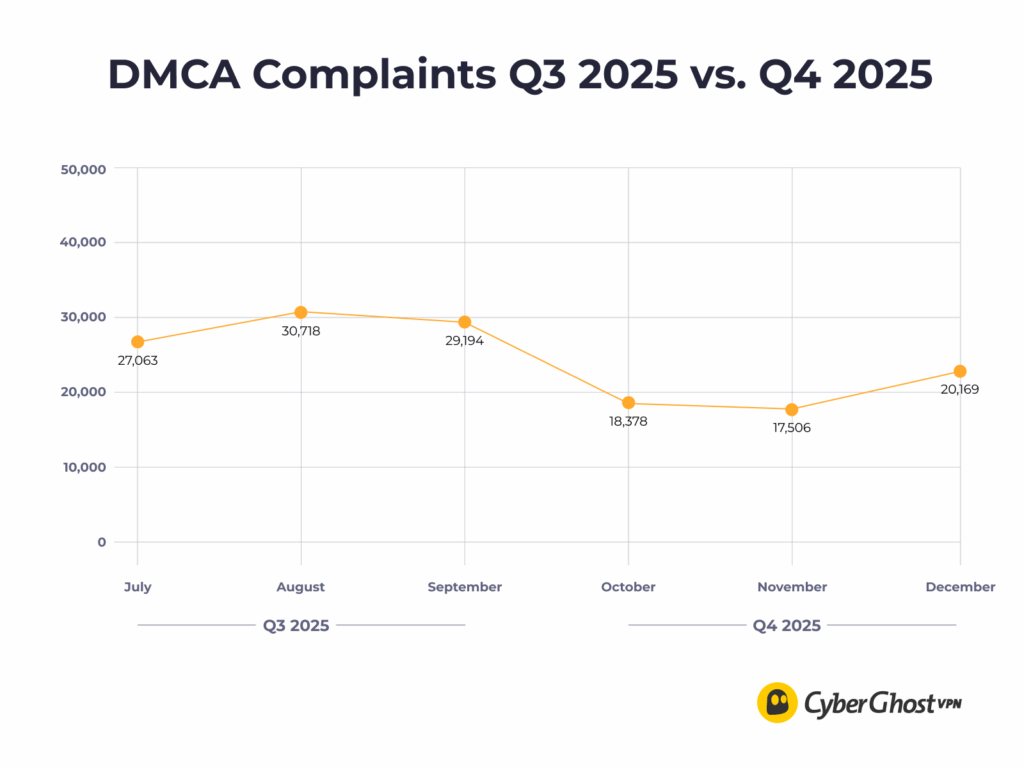
These notices aim to trace an IP address back to an individual. But on our network, that link doesn’t exist. There are no logs to match. No browsing history to pull. Every single complaint ends the same way: rejected for lack of evidence.
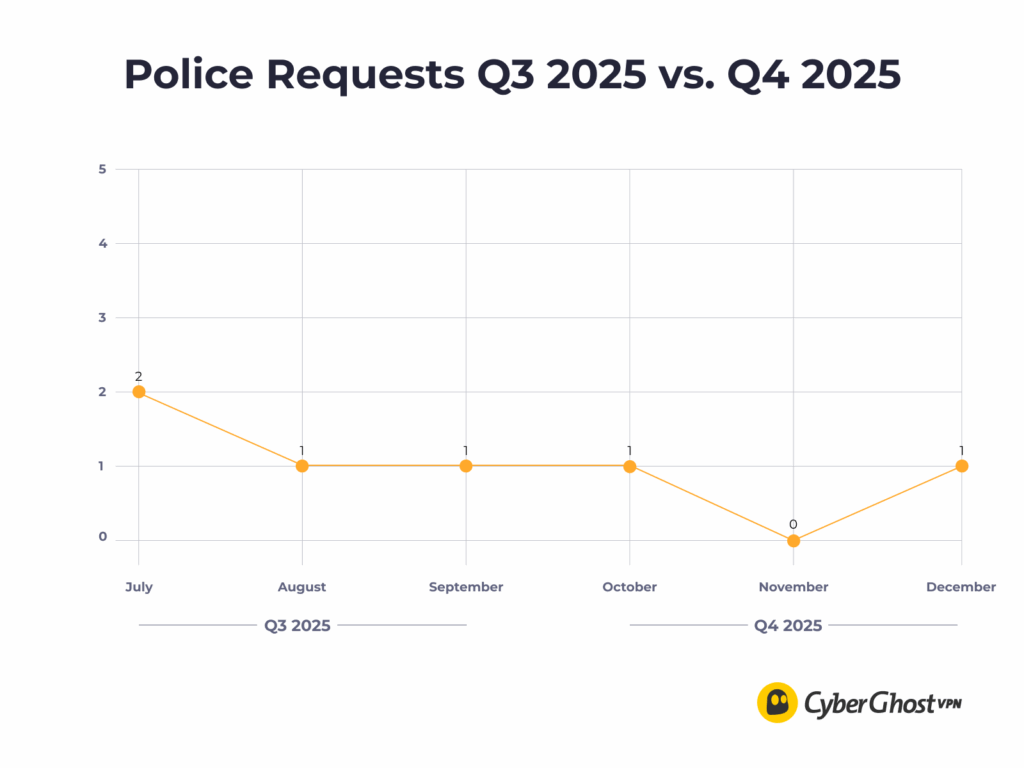
Police Requests
| October | November | December |
| 1 | 0 | 2 |
Law enforcement agencies contacted us once in October and then again in December 2025, each time seeking data tied to IP activity. As always, there was no user data to hand over.
Spotlight: CyberGhost VPN Completes Third Deloitte Audit
At CyberGhost, we’re always ready to prove we practice what we preach. That’s why this quarter, we completed our third independent audit conducted by Deloitte Audit Romania.
Carried out under the rigorous International Standard on Assurance Engagements (ISAE) 3000 (Revised), this audit put our VPN configuration, management systems, and token-based Dedicated IP technology under the microscope.
The results? The audit verified that our server configurations perfectly align with our strict No Logs policy. It serves as independent validation that our refusal to log your data is hardwired into our infrastructure.
Read the full Audit Announcement
What Our Bug Bounty Program Found This Quarter
CyberGhost runs a public bug bounty program to invite independent security researchers to examine our apps, infrastructure, and backend systems. The goal is to see how the product behaves when tested by people who approach it with a critical eye.
In Q4 2025, we received 19 submissions, five of them unique. Two reports identified valid security issues, both of which were resolved. The remaining submissions didn’t reveal exploitable weaknesses, but they were still part of the process. They helped confirm assumptions, validate existing protections, and ensure that expected safeguards behaved as intended.
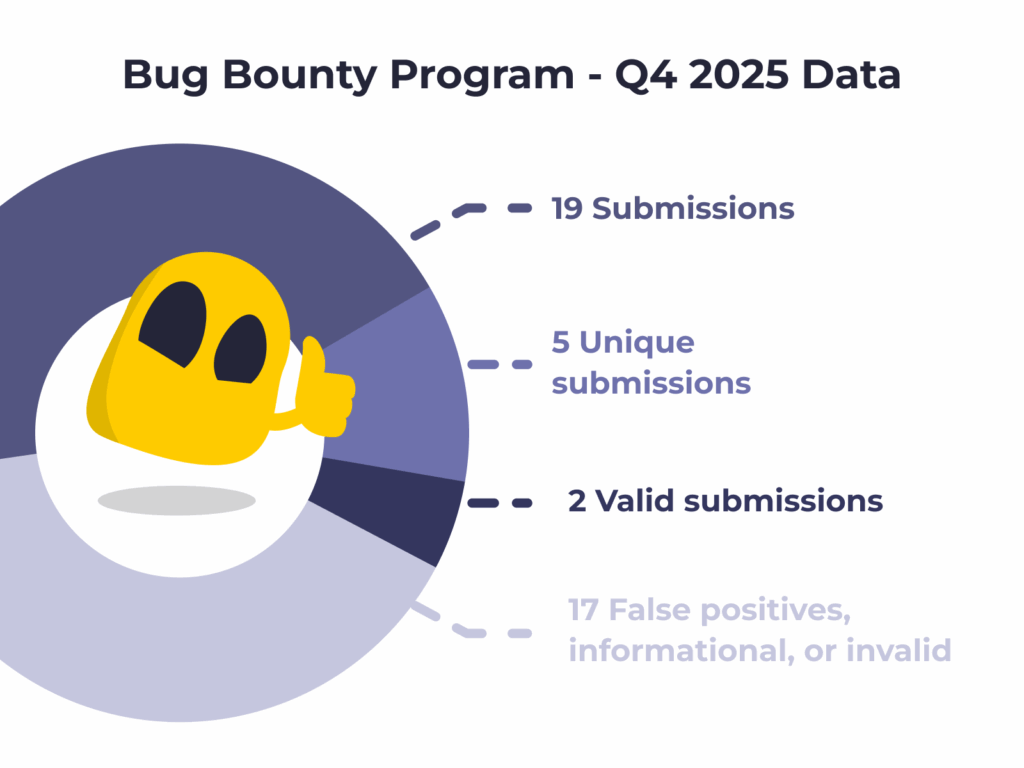
This balance is what we look for. Most reports should confirm that things are working as designed. And when something needs attention, it should surface quickly and be addressed without delay.
Q4 Cybersecurity in Review
Each quarter, we also look beyond our own reports to see how privacy and security are being tested elsewhere. These stories offer context for the risks people face online and how those risks continue to evolve.
Businesses finally acting on AI security risks
A late-2025 global report found that companies are increasingly assessing AI-related security risks before deployment. The share of organizations evaluating AI tools for security concerns nearly doubled from the year before, reflecting growing awareness of vulnerabilities tied to generative AI, data leaks, and fraud. At the same time, businesses are adopting AI for cybersecurity functions like phishing and intrusion detection, even as gaps in skills and risk understanding persist.
Multiple exploited issues show systemic weaknesses
Security reporting in December highlighted a pattern of actively exploited vulnerabilities across widely used software components. Rather than isolated bugs, the incidents showed how attackers continue to target common building blocks in modern systems, where a single weakness can affect many organizations at once.
Browser exploits forced emergency patches before year’s end
Also in Q4, Google issued an emergency update for Chrome to address a zero-day vulnerability actively exploited in the wild. These kinds of browser flaws matter because the browser is often the first point of contact between users and potential threats online. When attackers have a way to compromise browsers, they can use that foothold to deliver malware, steal credentials, or escalate privileges on end-user machines.
Malware targeting developer ecosystems resurfaced after earlier containment
Security intelligence from late 2025 showed that the Glassworm family of malware resurfaced in new waves across open-source package repositories like OpenVSX and the Visual Studio marketplaces. The malware uses clever evasion techniques — such as invisible characters in package names — to trick developers into downloading compromised code that can steal credentials or install remote access tools. These attacks highlight how supply chain risks have shifted from targeting users directly to compromising the tools developers rely on.

Leave a comment