Understanding how the Blowfish algorithm works today can be tricky. Blowfish is often described as fast, secure, and reliable, but you may have also seen it called outdated or even risky. That contradiction makes it hard to know what to believe, especially if you’re trying to understand how your data is actually being protected.
So is Blowfish still a safe choice, or does it fall short of modern security standards? And why is it still used in some cases but avoided in others? Let’s take a closer look at Blowfish and what you should know before relying on it.
What Is the Blowfish Algorithm and Why Was It Created?
The Blowfish algorithm is a symmetric encryption method, which means it uses the same secret key to encrypt and decrypt data. It takes readable information, called plaintext, and transforms it into an unreadable format known as ciphertext. Only someone with the correct key can convert it back. Blowfish is designed to be fast, efficient, and secure, which makes it especially useful for protecting data on computers and networks.
Blowfish stands out because it balances speed with strong security. It uses a variable key length ranging from 32 bits to 448 bits. This flexibility allows you to choose how strong you want your encryption to be. The algorithm works on 64-bit blocks of data and runs them through multiple rounds of complex operations1. These scramble the data thoroughly, making it extremely difficult to reverse without the key. Even with its complexity, Blowfish performs well on both older and modern systems.
The algorithm was created in 1993 by Bruce Schneier. At the time, many encryption algorithms were proprietary, restricted, or too slow for everyday use. Schneier claims he wanted to create a free and open alternative that anyone could use. He states it was designed to be unpatented and accessible, helping more people and organizations protect their data2.
Blowfish was also designed to address weaknesses in older encryption standards like the Data Encryption Standard (DES). It used shorter keys that became vulnerable as computing power increased2.
How Blowfish Encryption Actually Works (Step-by-Step)
The Blowfish algorithm encrypts data using a combination of key-dependent substitution and repeated transformation rounds. It’s designed so that even small changes in the input or key produce completely different outputs.
- You start with a secret key. Blowfish uses a single symmetric key. This key isn’t used directly to encrypt data. Instead, it’s used to generate a set of internal values that drive the entire encryption process.
- The key is expanded into subkeys (P-array and S-boxes). Blowfish begins with fixed initial values and then modifies them using the provided key. It creates an 18-entry P-array and four S-boxes, each containing 256 entries. This process is computationally expensive because Blowfish repeatedly encrypts data to transform these values. The result is a set of subkeys that are unique to the original key and highly resistant to analysis.
- The data is split into 64-bit blocks and divided in half. Blowfish processes data in 64-bit blocks. Each block is split into two 32-bit halves, usually called the left (L) and right (R) sides. These halves are then processed through multiple rounds of transformation.
- The algorithm runs 16 Feistel rounds. Blowfish uses a Feistel network, which means only one half of the data is transformed at a time while the other half is mixed in1. In each round:
-
- The left half is XORed with a value from the P-array.
- The result is passed through a function (called the F-function).
- The F-function uses the S-boxes to perform substitutions and combine values.
- The output is XORed with the right half.
- Finally, the left and right halves are swapped.
This repeated process ensures strong diffusion and confusion, meaning the output becomes increasingly scrambled and dependent on both the data and the key.
- The F-function introduces non-linearity. The F-function is a core part of Blowfish’s security. It splits input into smaller parts, looks up values in the S-boxes, and combines them using addition and XOR operations. This step makes the encryption unpredictable and resistant to simple attacks because it breaks any direct relationship between input and output.
- Final transformations complete the encryption. After 16 rounds, Blowfish performs a final swap of the two halves. It then applies the last two values from the P-array using XOR to produce the final encrypted block.
- The output is a ciphertext that appears random. The encrypted data has no visible pattern and can’t be reversed without the correct key and subkeys.
- Decryption uses the same structure in reverse order. Blowfish doesn’t need a separate decryption algorithm. It simply runs the same process with the P-array applied in reverse order. This is a key advantage of Feistel-based designs.
What Makes Blowfish Unique Compared to Other Algorithms?
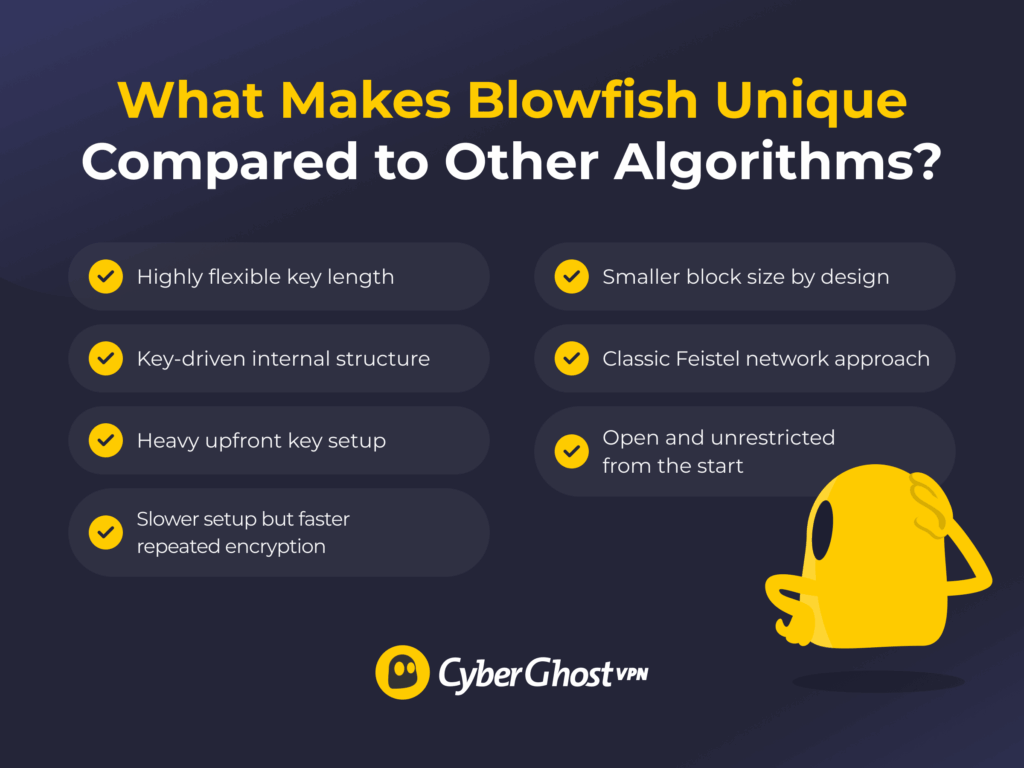
Blowfish stands out because it was designed to solve practical problems that older encryption algorithms struggled with. At the time, many ciphers were either slow, limited in flexibility, or restricted by patents. Blowfish introduced a different approach that focused on speed, adaptability, and open use.
- Highly flexible key length: Blowfish supports 32- to 448-bit keys, while Advanced Encryption Standard (AES) is limited to 128-, 192-, or 256-bit keys, and DES uses a fixed 56-bit key5.
- Key-driven internal structure: Blowfish generates S-boxes from the key, while AES uses fixed S-boxes and DES relies on predefined tables.
- Heavy upfront key setup: Blowfish requires more time to initialize due to its key expansion process but then runs efficiently on general CPUs2.
- It has a slower setup but faster repeated encryption: Blowfish takes longer to initialize due to key expansion, while AES has a much faster setup, making it better for systems that change keys often.
- Smaller block size by design: Blowfish uses 64-bit blocks, while AES uses 128-bit blocks.
- Classic Feistel network approach: Blowfish uses a Feistel design where halves are swapped each round; AES uses a different structure that is designed for efficiency and scalability in modern systems.
- Open and unrestricted from the start: Blowfish removed licensing barriers that existed with some older algorithms.
Pros and Cons of Blowfish Encryption
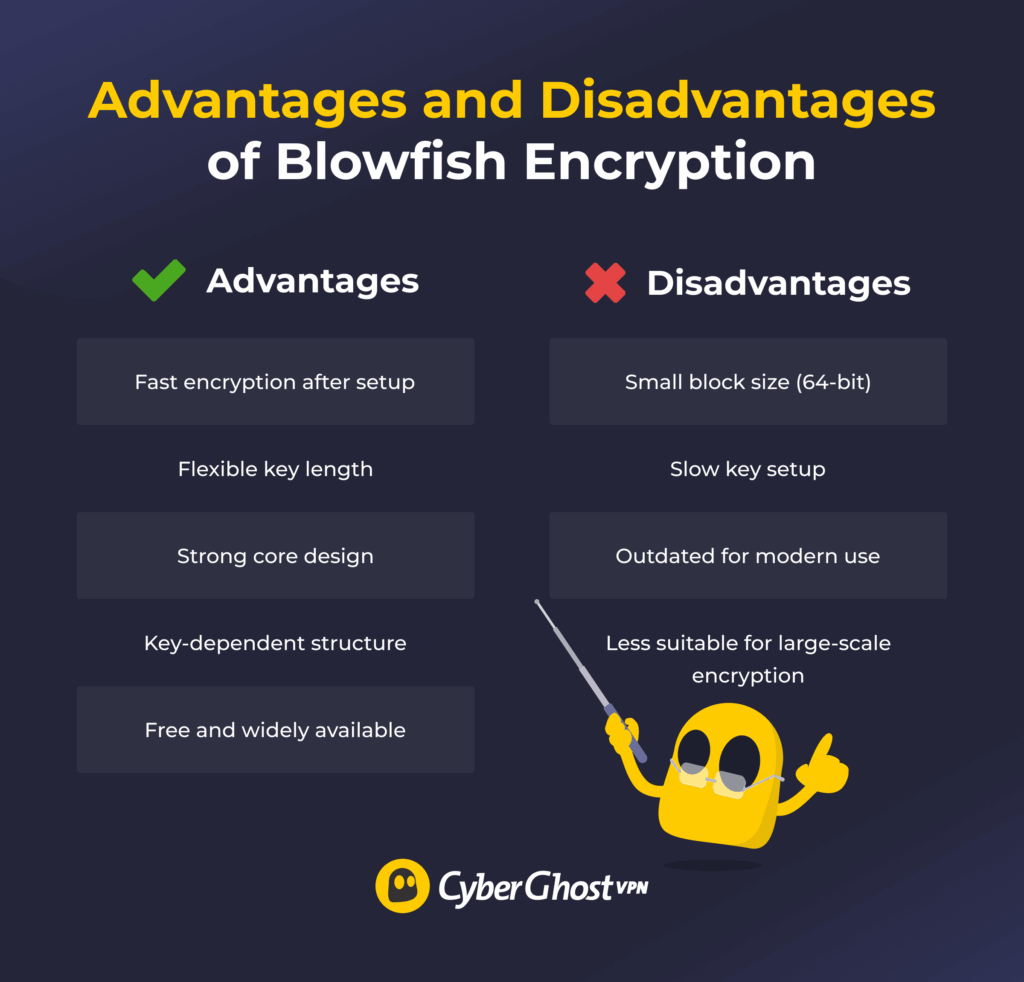
Advantages
- Fast encryption after setup: Performs efficiently in software once the key expansion phase is complete.
- Flexible key length: Supports a wide range of key sizes, allowing different levels of security.
- Strong core design: According to Bruce Schneier2, no practical attacks have broken the full algorithm when used correctly.
- Key-dependent structure: Generates internal S-boxes from the key, increasing resistance to analysis.
- Free and widely available: Not patented, which made it easy to adopt across different systems.
Disadvantages
- Small block size (64-bit): Less secure for large data volumes and vulnerable to attacks like Sweet32. Sweet32 is a type of attack that targets encryption algorithms with 64-bit block sizes. When large amounts of data are encrypted with the same key, repeating patterns can occur, which attackers may exploit to recover small portions of the original data3.
- Slow key setup: Not ideal for systems that frequently generate or change keys.
- Less common in modern systems: Often replaced by newer standards like AES for general-purpose encryption.
- Less suitable for large-scale encryption: Struggles with modern data sizes compared to algorithms with larger block sizes.
Is Blowfish Encryption Still Safe?
Blowfish isn’t considered broken, but it’s been widely deprecated in the last few years, and it’s used less often in modern encryption systems. For example, some VPN implementations have moved away from Blowfish in favor of newer, more secure ciphers6.
Blowfish’s main limitation could be its 64-bit block size, which may make it less secure when encrypting large amounts of data. This can introduce risks when large amounts of data are encrypted with the same key, as patterns may begin to repeat over time3.
Blowfish also has a slow key setup process. This isn’t a security flaw, but it makes the algorithm less practical in systems that require frequent key changes. Newer algorithms are designed to handle these scenarios more efficiently.
In some cases, Blowfish is still used, such as in bcrypt for password hashing, where its slow key setup helps resist brute-force attacks. However, for general encryption, most systems now use AES because it’s designed to handle larger data volumes and work efficiently on modern hardware. Bruce Schneier, the creator of Blowfish, has also pointed to newer designs like Twofish for modern use, reflecting how encryption approaches have evolved over time2.
Where Blowfish Is Used in Real Life
Blowfish isn’t widely used in new systems today, but it still appears in specific areas where its design offers practical advantages:
- Password hashing: Blowfish is the foundation of bcrypt, a widely used password hashing method. Its slow key setup helps protect against brute-force attacks by making each guess more expensive4.
- Legacy file encryption tools: Blowfish has been used to encrypt files before storage or transfer. Some older tools still rely on it for securing local data.
- Legacy VPN and network systems: Blowfish was used in earlier VPN configurations, though modern implementations have largely moved to newer ciphers as older options are phased out6.
- Embedded and resource-limited systems: In environments where lightweight software encryption was needed, Blowfish was a practical choice due to its efficiency after initialization.
Blowfish’s Place in Modern Encryption
Blowfish played an important role in making encryption more accessible and efficient, and it’s used in some situations today. However, its design wasn’t built for modern data environments, where large volumes of information are processed continuously.
As a result, most modern applications use AES, which is designed to handle larger data volumes and operate efficiently on current hardware. It’s widely used across industries, including VPN services like CyberGhost VPN. If you want to see how modern AES 256-bit encryption is applied in practice, you can try CyberGhost VPN with a 45-day money-back guarantee (14 days for monthly plans).
FAQ
What is the Blowfish encryption algorithm used for?
The Blowfish algorithm is used to encrypt data so it can’t be read without a secret key. It has been used for securing files, protecting data in transit, and supporting password hashing systems like bcrypt. Today, it’s mostly found in legacy systems and specific use cases rather than modern encryption applications.
Why is Blowfish considered secure despite its age?
The Blowfish algorithm is considered secure because its core design remains strong and hasn’t been practically broken. It uses 16 rounds of encryption, key-dependent S-boxes, and a large possible key size, which together make it resistant to many common attack methods.
Its structure creates high confusion and diffusion, meaning small changes in input or key produce very different outputs. However, its security is limited in modern use by its 64-bit block size, which has caused the algorithm to depreciate, not by flaws in the algorithm itself.
What are the limitations of Blowfish’s 64-bit block size?
The main limitation of the Blowfish algorithm’s 64-bit block size is that it can’t safely handle large amounts of data. When too much data is encrypted with the same key, patterns can start to repeat due to the limited number of possible block combinations.
This increases the risk of attacks like Sweet32, where attackers exploit these repetitions to recover information. Modern algorithms avoid this issue by using larger block sizes, which allow more data to be encrypted securely without pattern leakage.
How does Blowfish differ from AES and Twofish?
The Blowfish algorithm differs from the AES and Twofish algorithms in block size, design, and modern use. Blowfish uses a 64-bit block size, while AES and Twofish use 128-bit blocks, making them better suited for large data volumes.
Blowfish relies on a Feistel structure with key-dependent S-boxes, whereas AES uses a different design optimized for performance and security, and Twofish improves on Blowfish with a more advanced structure and fewer limitations.
Is Blowfish still recommended for modern encryption needs?
The Blowfish algorithm isn’t recommended for most modern encryption needs. While its core design remains secure, its 64-bit block size makes it unsuitable for encrypting large amounts of data, and newer algorithms are designed to handle modern security and performance requirements. Today, standards like AES are preferred for modern applications.
References
- Description of a New Variable-Length Key, 64-Bit Block Cipher (Blowfish) – Massachusetts Institute of Technology
- The Blowfish Encryption Algorithm — Schneier
- On the Practical (In-)Security of 64-bit Block Ciphers – Sweet32.info
- A Future-Adaptable Password Scheme – USENIX The Advanced Computing Systems Association
- Advanced Encryption Standard (AES) – National Institute of Standards and Technology
- Data-Channel Encryption Cipher Negotiation on Access Server – OpenVPN


Leave a comment