Human technological innovation is awe-inspiring. We’ve explored space, developed AI technology, and created vaccines to help combat a global pandemic in record time. You’ll understand my disappointment when I discovered that the most popular password in 2026 is…wait for it…’123456’ and it’s been the most popular password for a few years now, along with ‘123456789’, ‘Qwerty’, and ‘Password’. Groundbreaking, I know. We can do better. No, we have to do better! Our cybersecurity and, quite frankly, our collective dignity is at stake. Dramatic? Yes! Incorrect? No!
We all use several passwords every day, but what do they actually do?
What Do Passwords Do?
A password is your first (and often only) line of defense against cybercriminals. It’s also how platforms ensure only you can access your data. Passwords are like club bouncers only, with less actual muscle and neck tattoos.
Our IRL lives are becoming increasingly digitized. We find ourselves needing to log-in to access more and more aspects of our day-to-day life. You’ll need a password to get food deliveries to your door, find your way on a map, and communicate on any social media platform. You’ll even need a password to find the love of your life or at least your love for the night.
The rapid rise of remote work has upped the need for strong password authentication. Employees, more and more, require access to work resources from locations other than the office. Use the best VPN for PC to prevent your passwords from being leaked on unsecured WiFi connections.
Now’s the time to take our online security seriously. It’s important to understand and recognize the butterfly effect of damage that even a single data breach can cause.
The Perils of A Passable Password
Poor passwords can pack a painful punch if they fall into the wrong hands. According to a Verizon report1 , 89% of total data breaches were due to stolen or weak passwords. The UK’s NCSC worldwide breach analysis2 found that 23.2 million breached accounts used ‘123456’ as a password. Practice some self-love, and don’t put your entire online data security at the mercy of a flimsy password like ‘password1’ or ‘batman’. You deserve better than that.
While threat actors use different methods to target their victims, cracking weak passwords is one of their most popular approaches. This is because it’s often the easiest way to steal credentials or access a restricted account or system. According to IBM’s 2024 Cost of a Cyberbreach Report, weak passwords were one of the common causes of data breaches, which cost companies an average of $4.88 million that year.
I get it, though, password fatigue is real. Having to constantly create and change your passwords, and remember them is frustrating. You might have given up and surrendered, letting cyber-fate decide whether your password will protect you. Unfortunately, if you don’t change your password to a stronger and better one, cybercriminals can and will come for your data.
A Cybercrook’s Toolbox to Hack Your Password
The shorter and simpler your password, the easier it is for cybercriminals to hack.
Top 4 tools cybercriminals use to hack your password.

In response to cybercrime, online security has evolved at a lightning pace. The question is whether passwords are keeping up.
Are Passwords Still In?
The password has begun to lose some popularity. Microsoft, in a big influencer move, took a massive step towards eliminating passwords a couple of years ago. Windows now gives you the option to go passwordless, replacing it with either an authenticator app (Windows Hello), a security key, or verification codes sent to your phone or email.
Others are also joining the #passwordsareover trend. Apple’s new operating systems incorporate passkeys in iCloud Keychain. Google has also focused on a passwordless future.
You could test-drive life without a password using biometric authentication (face, voice, fingerprint recognition), hardware and software tokens, pins, SSO (single sign-on authentication), and cryptographic keys.
Yes, a world without passwords is intriguing, but it won’t happen overnight. We’ve got a lot to figure out, and passwordless tools won’t be widely accessible for everyone on every device and platform for a long time. For now, you still need passwords for most accounts. That said, you’re going to need a good one.
How to Build a Stronger Password
Construction is key. Knowing how to build your password will help you create one that’ll stay strong no matter what cybercriminals hit it with.
Check out 11 of the biggest password DOs and DON’Ts:
![]() blend a mix of numbers, letters (upper and lowercase), and symbols. The more complicated the password, the harder it’ll be to crack in a cyberattack.
blend a mix of numbers, letters (upper and lowercase), and symbols. The more complicated the password, the harder it’ll be to crack in a cyberattack.
Instead of ‘password1’, try ‘p@sS_w0RD#one1’, or instead of ‘123456’, try ‘0ne_TWO_3_FOUR_5_SIX’.
![]() use numbers or letters in a predictable sequence or a predictable key pattern. ‘Qwerty’ is a predictable password for a reason. It’s the sequence of the top left letters on your keyboard. Eureka moment! Once you get over it, this password isn’t original and won’t protect you from cyberattacks. Shake it up, people! 123456 is a NO, but 634152 is a GO!
use numbers or letters in a predictable sequence or a predictable key pattern. ‘Qwerty’ is a predictable password for a reason. It’s the sequence of the top left letters on your keyboard. Eureka moment! Once you get over it, this password isn’t original and won’t protect you from cyberattacks. Shake it up, people! 123456 is a NO, but 634152 is a GO!
![]() choose length over complexity. Size does matter here! You’re more likely to remember a longer yet simpler password than a shorter, more complicated one. A password with at least 12 characters will give you robust protection without risking forgetting or mixing it up.
choose length over complexity. Size does matter here! You’re more likely to remember a longer yet simpler password than a shorter, more complicated one. A password with at least 12 characters will give you robust protection without risking forgetting or mixing it up.
![]() use your personal details. Your birthday, name, family name, street address, hobbies, and pet’s name are all off the table. Cybercriminals can and will find that information online and use it to crack your password. While Charlie makes for a good canine companion, it doesn’t make for a strong password.
use your personal details. Your birthday, name, family name, street address, hobbies, and pet’s name are all off the table. Cybercriminals can and will find that information online and use it to crack your password. While Charlie makes for a good canine companion, it doesn’t make for a strong password.
![]() use two-factor or multi-factor authentication. Team your password up with other forms of authentication, like biometric, hardware tokens, security questions, and OTPs (One Time Passwords). It’s like building your own little Avengers squad, just for your online security.
use two-factor or multi-factor authentication. Team your password up with other forms of authentication, like biometric, hardware tokens, security questions, and OTPs (One Time Passwords). It’s like building your own little Avengers squad, just for your online security.
![]() re-use your password. Recycling plastic? Yes! Recycling your password? No! If cyber attackers crack your password for one platform, the rest of your accounts become sitting ducks if you’ve used the same password for everything. Use a different password for each account! Ok, now you’d say, how will I remember all these passwords when I can’t even remember what I had for lunch! Get a password manager to do the heavy lifting for you.
re-use your password. Recycling plastic? Yes! Recycling your password? No! If cyber attackers crack your password for one platform, the rest of your accounts become sitting ducks if you’ve used the same password for everything. Use a different password for each account! Ok, now you’d say, how will I remember all these passwords when I can’t even remember what I had for lunch! Get a password manager to do the heavy lifting for you.
![]() vet your passwords regularly. It’s always good to clear bad energy from your life, and that includes weak passwords. Put your passwords to a strength test; try PasswordMonster.com or Howsecureismypassword.net. They determine how strong your password is, and you’ll also get a -very scary- estimate on how long it’d take a cybercriminal to crack it. Prepare to freak out. I tried it; a password with characters including caps, numbers, and characters takes 26 billion years to crack, while a more clear-cut ‘987123’ takes 25 microseconds to crack.
vet your passwords regularly. It’s always good to clear bad energy from your life, and that includes weak passwords. Put your passwords to a strength test; try PasswordMonster.com or Howsecureismypassword.net. They determine how strong your password is, and you’ll also get a -very scary- estimate on how long it’d take a cybercriminal to crack it. Prepare to freak out. I tried it; a password with characters including caps, numbers, and characters takes 26 billion years to crack, while a more clear-cut ‘987123’ takes 25 microseconds to crack.


![]() email or text your passwords to yourself or your friends. Avoid having your password floating around out there in your easily hackable email or phone records. Instead, try the old-fashioned way of writing your password down with a pen and paper and storing it in a safe location. Who doesn’t love a good throwback to a time before everything was recorded online?
email or text your passwords to yourself or your friends. Avoid having your password floating around out there in your easily hackable email or phone records. Instead, try the old-fashioned way of writing your password down with a pen and paper and storing it in a safe location. Who doesn’t love a good throwback to a time before everything was recorded online?
![]() make use of password-creating methods. Feeling uninspired? Have a password writer’s block? Here’s what you can do:
make use of password-creating methods. Feeling uninspired? Have a password writer’s block? Here’s what you can do:
-
-
- The Sentence Method. Create a random sentence and apply a rule to create a password using it. Try taking the last 2 letters of every word in the sentence to create your password. Turn ‘You caught the very last train lucky fish’ into ‘ouhtherysrinkysh’.
- ‘Three Random Word Method’3. Join 3 completely random words together. It could be ‘MattressRotationBurger’ or ‘CupcakeRoadZebra’. Have fun with it!
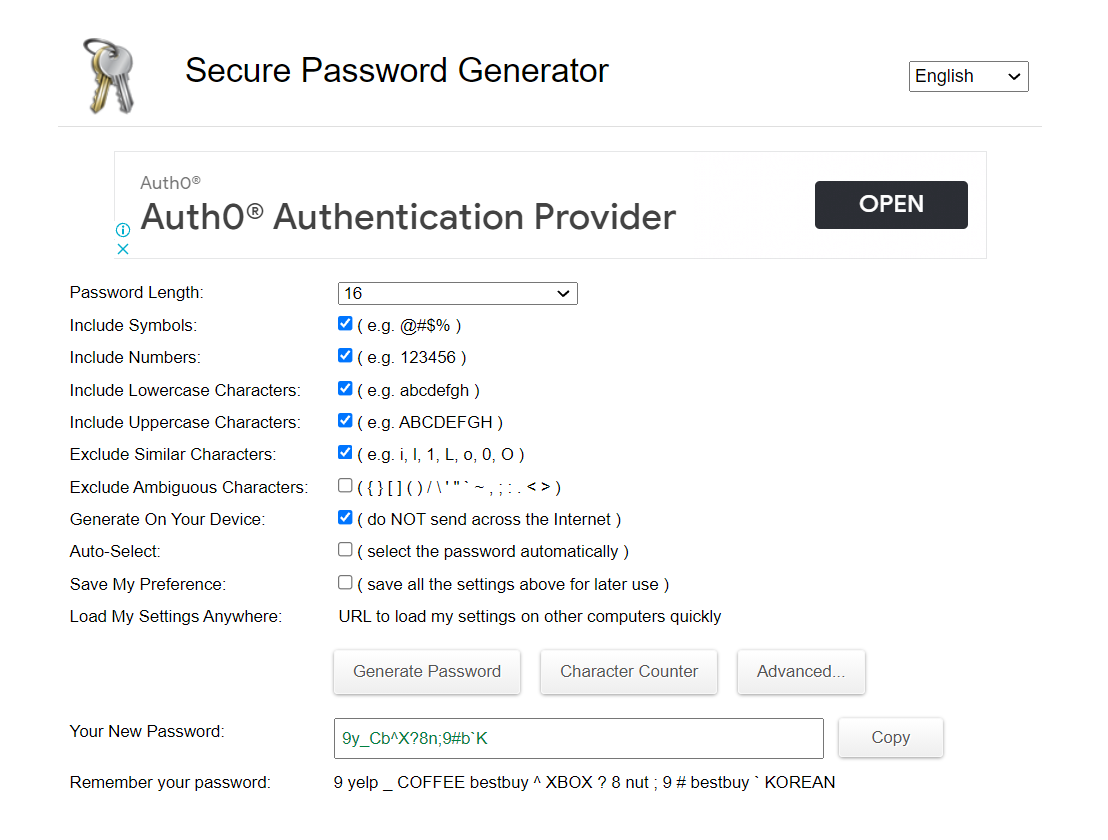
- The password generator at passwordsgenerators.net.
Create a completely randomized password for you.
-
![]() create or use your passwords while connected to public Wi-Fi without a VPN.You should never use public Wi-Fi without a VPN, especially when you’re dealing with your passwords. It’s nothing for cybercriminals to intercept and steal your personal information, including your passwords.
create or use your passwords while connected to public Wi-Fi without a VPN.You should never use public Wi-Fi without a VPN, especially when you’re dealing with your passwords. It’s nothing for cybercriminals to intercept and steal your personal information, including your passwords.
![]() try a password manager. I know changing your passwords and remembering different ones is a part-time job! Get a trusted buddy to secure and remember your passwords for you.
try a password manager. I know changing your passwords and remembering different ones is a part-time job! Get a trusted buddy to secure and remember your passwords for you.
Cybercrime is real and we all have to deal with it as technology continues to intertwine with our lives. A strong password strength is a small and easy step towards protecting yourself and your data online.
FAQ
Should I change my passwords regularly?
No! While this may seem counterintuitive, according to recommendations4 by NSIT (National Institute of Standards and Technology), frequent password changes don’t help protect your online security. The more you change your passwords, the more likely you’ll constantly forget and jumble up your passwords.
It’s best to focus on building strong passwords for each account. Better yet, use a password manager to create and manage passwords that’ll stand the test of time.
What are examples of bad passwords?
According to CyberNews5, drumroll please, the top ten most common and worst passwords to use in 2026 are:
-
- 123456
- 123456789
- Qwerty
- Password
- 12345
- Qwerty123
- 1q2w3e
- 12345678
- 111111
- 1234567890
What’s Multi-Factor Authentication (MFA)?
It’s an ultra-secure authorization where you use a password plus at least one other authorization tool to access a specific platform or site. Authorization tools include biometric authorization, security questions, and OTPs (One Time Pins).
Are password managers safe to use?
Yes, you’ll find password managers developed by reputable security companies are not just safe but very easy to use. A lot of them will help you generate, manage, and store passwords in an ultra-secure vault.
Use a password manager in conjunction with CyberGhost VPN for maximum security! CyberGhost VPN encrypts your traffic to keep snoopers away from your data.
References
- https://www.verizon.com/business/resources/reports/dbir/
- https://www.ncsc.gov.uk/news/most-hacked-passwords-revealed-as-uk-cyber-survey-exposes-gaps-in-online-security
- https://www.ncsc.gov.uk/news/ncsc-lifts-lid-on-three-random-words-password-logic
- https://auth0.com/blog/dont-pass-on-the-new-nist-password-guidelines/
- https://cybernews.com/best-password-managers/most-common-passwords/

Leave a comment
Sally Steiner
Posted on 31/10/2021 at 15:23
jThis is such an enlightening article. I have iIt has really opened my eyes with regards to cyber safety. It is so user friendly.
Thank you