We’re kicking off 2026 the exact same way we ended last year: aggressively defending your right to digital privacy.
When you run a global VPN network, you get a lot of mail. Every quarter, we receive a steady stream of legal demands, copyright notices, and police inquiries, all looking for the same thing: data that ties an IP address to a specific user’s identity.
We publish this Transparency Report every three months to show you exactly who is knocking on our door, what they are asking for, and, most importantly, why we always send them away empty-handed.
Here’s a look at the data requests and bug bounty results from January, February, and March 2026, plus a roundup of the quarter’s biggest cybersecurity headlines.
Legal Requests — Our Q4 Numbers
We categorize the requests we receive into two main buckets:
- DMCA Complaints: Copyright holders demanding information because they believe one of our IPs was used to download or share protected content.
- Police Requests: Law enforcement agencies worldwide asking for logs or user identities connected to ongoing investigations.
Here is what hit our inbox this quarter:
| January | February | March | |
| DMCA Complaints | 19,296 | 15,973 | 18,264 |
| Police Requests | 2 | 2 | 0 |
No matter who makes the request, our response is identical. CyberGhost VPN operates on a strict No-Logs policy. Our infrastructure runs entirely on volatile RAM, meaning servers are wiped clean every time they reboot. We do not monitor your traffic, log your timestamps, or record your browsing history.
Because we don’t collect this data in the first place, we have nothing to share when authorities come asking.
DMCA Complaints
| January | February | March |
| 19,296 | 15,973 | 18,264 |
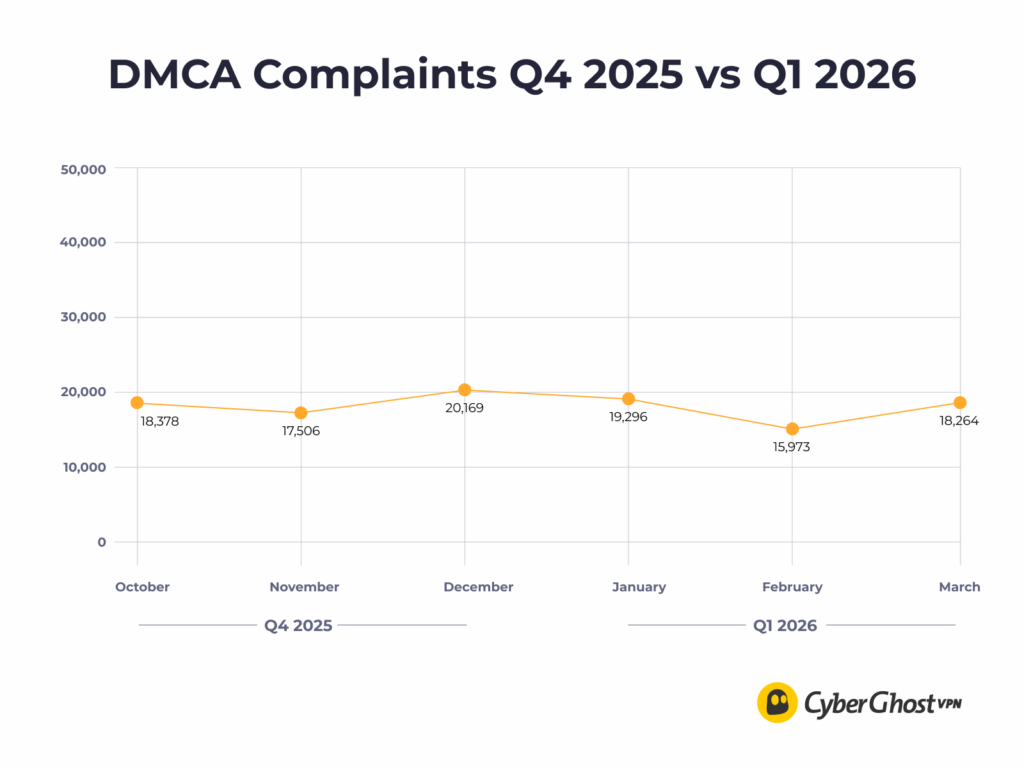
Compared to the 56,053 DMCA notices we received in Q4 2025, Q1 saw a slight decrease, leveling out at just over 53,000 complaints. Despite the sheer volume of these automated takedown requests, they all hit a dead end. Because we decouple your personal identity from your VPN IP address, it is mathematically impossible for us to trace network activity back to a specific user.
Police Requests
| January | February | March |
| 2 | 2 | 0 |
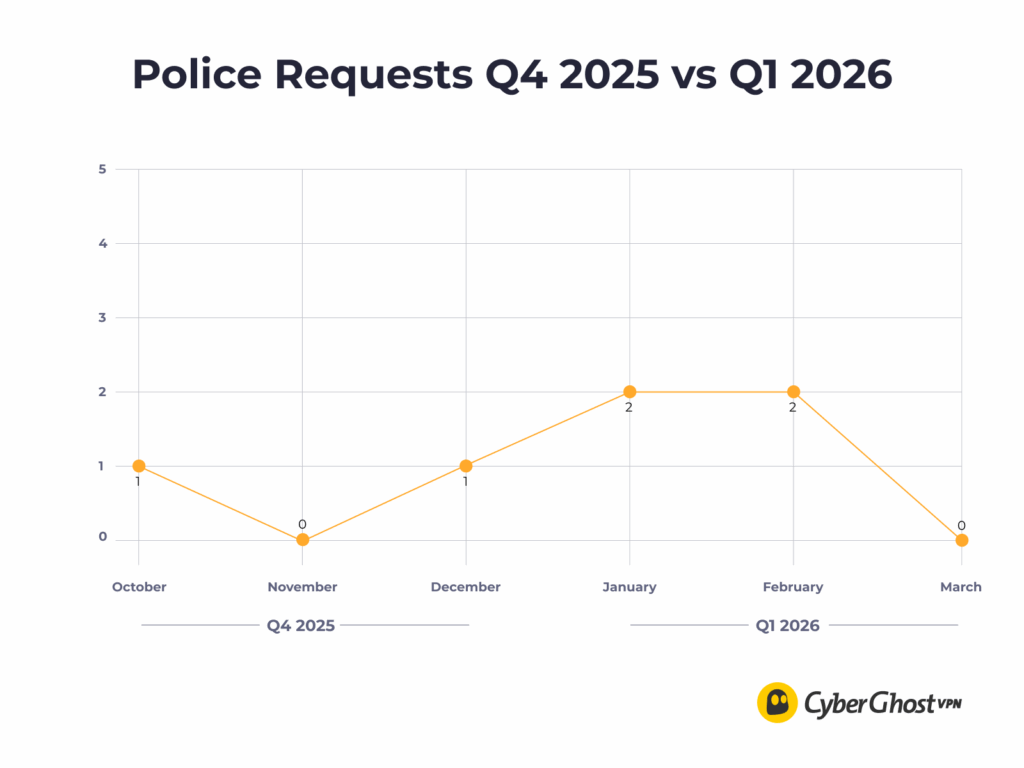
Law enforcement agencies reached out to us 4 times across Q1 (twice in January and twice in February). While we respect the work of authorities, our commitment to our users’ privacy is absolute. Zero logs mean zero data handed over, 100% of the time.
Q1 Bug Bounty: Stress-Testing Our Defenses
We don’t just rely on our own engineers to tell us our network is secure. Through our partnership with YesWeHack, we actively invite the global cybersecurity community to try to break our apps, infrastructure, and backend systems.
Here is how the Bug Bounty program performed in Q1 2026:
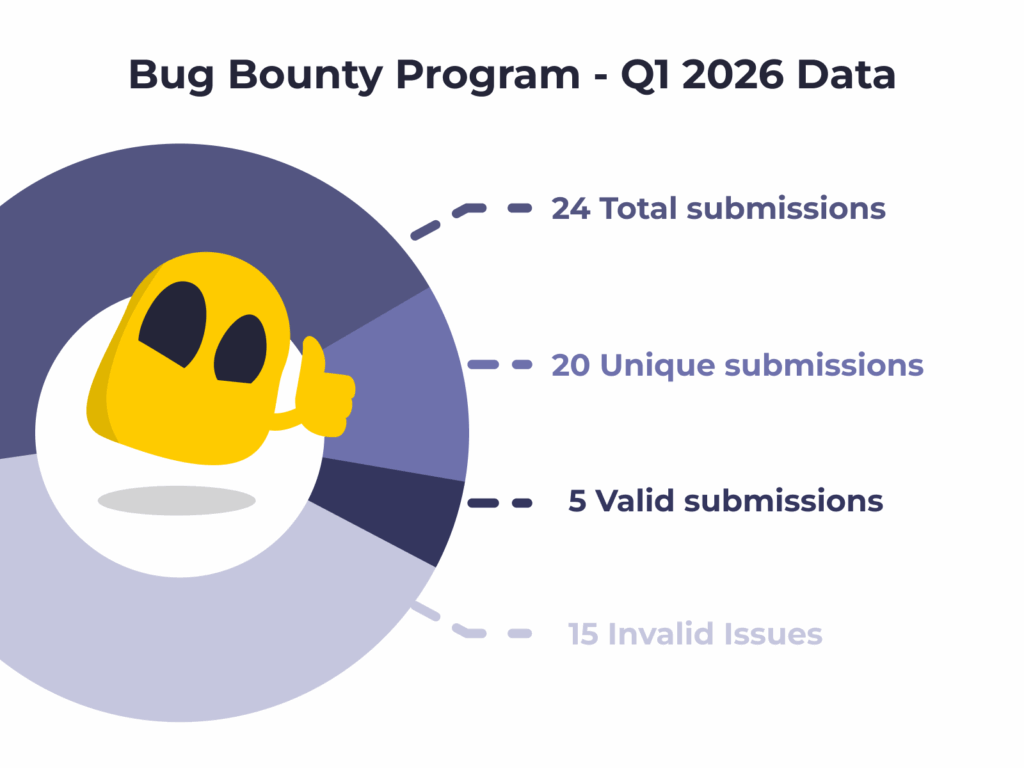
This quarter, ethical hackers successfully identified 5 valid issues, which our development team rapidly patched and resolved. The other 15 submissions were categorized as invalid or informational.
Even the “invalid” reports hold immense value. They help us double-check our blind spots, validate that our existing safeguards are functioning properly, and ensure our security posture remains rock-solid against evolving threats.
Q1 2026 Cyber Trends
A VPN is just one piece of your digital armor. To stay truly safe, it helps to know what threats are actively circulating on the web. Here are a few of the major cybersecurity stories that shaped the first three months of 2026.
Third-Party Vendors Remain the Weakest Link
In March, TELUS Digital confirmed a massive cyberattack orchestrated by the ShinyHunters ransomware group. The breach compromised roughly a petabyte of data belonging to its BPO (Business Process Outsourcing) customers, including FBI background checks and financial info. It’s a stark reminder that even if an organization’s internal security is strong, granting access to third-party vendors creates a massive vulnerability when things go wrong.
Cyberattacks Targeting Physical Infrastructure
Also in March, Intoxalock, a provider of ignition interlock devices, suffered a cyberattack that disrupted its servers nationwide. The attack caused a massive outage affecting installations, calibrations, and account access, impacting thousands of drivers across 45 US states. As everything becomes “smart” and connected, digital disruptions are increasingly resulting in real-world physical paralysis.
The Rise of Destructive “Wiper” Attacks
Ransomware is evolving from simple extortion to outright destruction. In mid-March, global medical tech giant Stryker detected a severe cyberattack from the hacktivist group Handala. Rather than just stealing data, the attackers managed to wipe over 200,000 servers, mobile devices, and corporate systems across 79 countries in real-time. It highlights a dangerous trend of state actors prioritizing maximum operational sabotage over financial payouts.
FCC Warns of Ransomware Surging Against Telecoms
Early in 2026, the US Federal Communications Commission (FCC) issued a severe warning to telecom businesses, citing a fourfold increase in ransomware attacks against the sector since 2021. The Commission highlighted that communications networks are highly vulnerable to cyber exploits, threatening national security and public safety. As attackers realize how much critical data flows through these pipes, the ISPs and telecoms that manage them have a massive target on their backs.

Leave a comment