Remember when you persuaded your school buddy to ask a dumb question on your behalf? Your friend took the teacher’s wrath while you giggled under your breath. A proxy server is that school buddy on the internet, except it’ll betray you before catching heat.
Let me explain…
If you’re using the internet without any privacy tools in 2025, you seriously need to step up your privacy game. Cyberstalking isn’t just for creeps anymore. Everyone from your ISP to the websites you visit wants to track your online activity to gather information about you and display relevant ads.
When you use a proxy server to access the internet, it communicates with a website on your behalf. This prevents websites from knowing your original IP address and location.
That said, governments, ISPs (internet service providers), and cybercriminals can intercept your traffic before it reaches the proxy. Authorities can also force proxy owners to reveal your identity and browsing history from their servers.
You need full VPN protection to protect your identity online. Unlike proxies, CyberGhost VPN encrypts your traffic before it leaves your device. No one can access your data at any point.
Keeping that in mind, let’s talk about the ins and outs of proxy servers – how they work and where they don’t.
What’s a Proxy Server?
You may be familiar with the phrases “proxy attendance” or “vote by proxy”. The term “proxy” literally means something or someone representing or acting on the behalf of another.
Digitally, a proxy server is a computer that acts as an intermediary between your device and a website. It receives your web requests and forwards them to websites and services on your behalf.
Companies use proxy servers to control user activity on their networks. That said, as an individual user, you’d want to use them if you don’t want the websites you visit to identify or locate you.
How Do Proxies Work?
Your IP address is your unique, digital address, much like your home address. When you open your internet browser and type in a website URL, you’re sending a data request to that website. Your data request also includes your IP address. That’s how a website knows where to send its response to your request, i.e. the web page you requested.
IP addresses map to a geographic location. Every time you access a website, you give away your IP address, and with that your rough physical location.
When you use a proxy, your request goes to the proxy server instead of the website’s servers. The proxy replaces your IP address with its own before sending your request to the website you’re visiting. Websites interact with the proxy server instead of your computer. This means they can’t get your IP address or identify your location.
Why Use a Proxy?
Your IP address is the digital equivalent of your home address—it gives away your location. If a website or service isn’t available where you are, websites will deny you access based on your IP address.
When you connect to the internet via a proxy server, websites can’t locate you. They’ll see the proxy server’s IP address and your request will seem to be coming from the proxy’s location. Just ensure you choose a proxy server based in a region where the website or service is available, and, theoretically, the website won’t block you anymore.
Sometimes, ISPs and network admins block certain websites’ IP addresses to restrict access to them. You can bypass such restrictions using a proxy server, too.
Your ISP or network admins will see you connecting to the proxy server’s IP address rather than the IP address of the blocked website. This is why they won’t restrict your access to certain websites either. Bypassing restrictions and censorship is the one reason why people go through the hassle of using the internet through a proxy server.
In theory, a proxy is a decent solution to access restricted sites. In practice, it’s a little more complex.
Benefits of a Proxy Server and Why It Doesn’t Always Work
Proxies offer some basic privacy, access, and control benefits. That said, they’re not always effective. Here’s why:
1. Open Internet Access
Proxies let you access restricted websites and services – even if they’re restricted for geographical reasons or because your government, ISP, or local network administrators have blocked them.
🚧 Why Proxies Don’t Always Unblock Content
In reality, proxies often fail to access restricted content and services. That’s because most commercial proxies offer limited IP addresses that websites can learn and block over time.
Many users also share similar IP addresses when using a proxy server, and websites flag such IP addresses. Governments, ISPs, and network admins can analyze your request to see what you’re accessing and block it before it reaches the proxy server too.
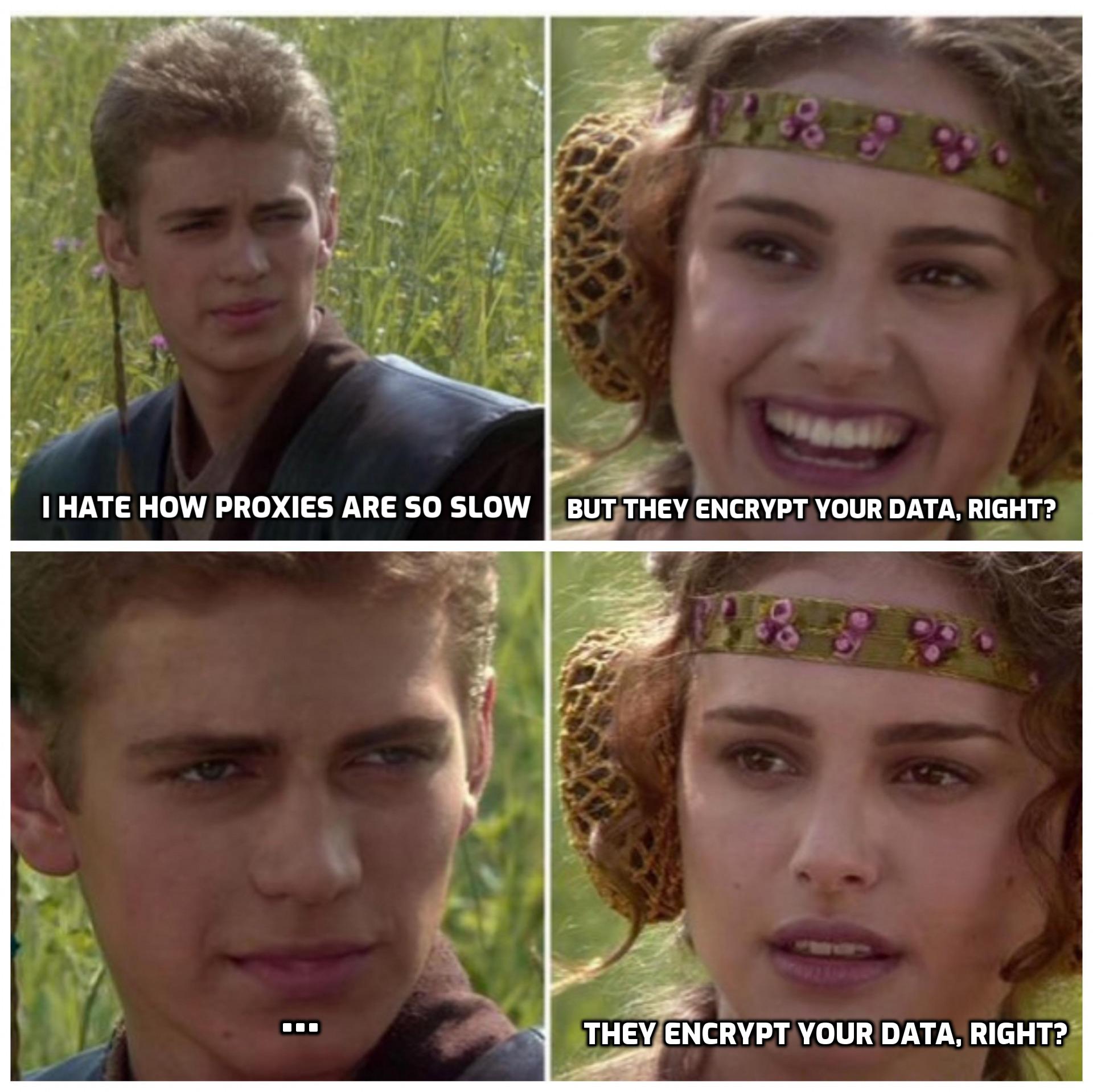
2. Privacy
People use proxies to protect their privacy when browsing. A proxy prevents a website from identifying your location based on your IP address. This is great, but when you use a proxy for privacy reasons, you’re overlooking one big issue.
🚧 Why Proxies Don’t Protect Your Privacy
The proxy owner knows your IP address, so they can see everything you do online. You have no reason to trust a proxy owner more than the government, your network admins, or ISP. Anyone who intercepts your connection between your device and the proxy server will also see your IP address along with your unencrypted data.
If I had to give you one reason for choosing a VPN over a proxy, it’d be encryption. CyberGhost VPN encrypts all your traffic with the strongest state-of-the-art encryption. No one can sneak a peek at your internet traffic – not your ISP, government, or any eavesdropping cybercriminals.
3. Access Control
Using a proxy to access the internet isn’t the only benefit. You can also use it to control and monitor how others use the internet on your home network. Sounds ironic, but it comes in handy for parental control, for instance.
Proxies are gateways letting internet traffic through. You can set one up yourself and specify rules to allow or block certain kinds of traffic and websites.
🚧 Why Proxies Aren’t Great for Parental Controls
Like everything else, proxies don’t give perfect access control. Say, if someone’s using CyberGhost VPN to access restricted internet, we’ll encrypt their traffic end-to-end. No proxy can decipher CyberGhost traffic, so anyone using our VPN can bypass the proxy rules.
4. Bandwidth and Speed
If your school or office network uses a proxy, you may notice how websites load much faster after your first visit. The proxy server saves a copy of web pages you visit frequently and displays recent local versions instead of reaching out to the website servers every time. This saves bandwidth and improves load times.
🚧 When it Doesn’t Work
You won’t get the same speeds when you set up a proxy at home. That’s because your office or school uses expensive private proxies with top-notch hardware and software specs.
You also won’t get the same level of service with a public proxy. Public proxies often have excessive traffic loads and high re-routing latency, which can significantly slow your internet speed.
Types of Proxy Server
Confused by all the contradicting information about proxies on the internet? That’s because proxy servers aren’t all the same. They can differ in their placement, working, and usage.
Different proxy servers’ types have different privacy levels, number of users, and functionality. I’ll list and explain the common ones:
1. Transparent Proxies
Just as the name indicates, these proxies are transparent. No, not to the websites you visit; they’re invisible to you, the end-user. Websites know you’re connecting through a proxy.
A transparent proxy isn’t of much use to you. That said, offices, schools, and public places use them to monitor what you’re doing on their network or to block certain websites. You won’t know if a company is using one unless they tell you.
Transparent proxies can’t track your internet traffic when you use CyberGhost VPN. That’s because we encrypt your data before it leaves your device.

2. Anonymous Proxies
Anonymous proxy servers replace your IP address, so you can access websites with increased privacy. Keep in mind that websites will know you’re using a proxy and may refuse you access on those grounds.
You won’t see targeted ads or localized content on websites with an anonymous proxy. That’s quite something… if you disregard the personalized ads these proxies push on you. What’s more, if some cyberpunks intercept your connection before your traffic reaches the proxy, they’ll see your IP address and may steal your identity.
3. Elite Proxies
Elite proxies, also known as high anonymity proxies, claim to go a step further than anonymous proxies. They change your IP address periodically and conceal you’re using a proxy. If all you want is to hide your IP from a website, they’re a good solution.
The downside? Changing IP addresses adds latency. Elite proxy servers from well-known providers quickly become overcrowded and will further slow you down.
Your data remains unencrypted even with elite proxies, so snoopers can still find out your IP address before your request reaches the proxy server. Malicious users can then steal personal information as it leaves the proxy and see who you are.
4. Dedicated Proxies
Dedicated proxies are exclusive to one user only. Naturally, they’re terrible at maintaining your privacy. Anyone can trace the proxy back to you with a little persistence.
That said, you don’t have to share your server’s resources with anyone which gives you better speeds. You also won’t find websites and online forums blocking your IP address due to other users on the same proxy violating website policies.
5. General Proxies
Most proxy users share a general proxy server. General proxies give you the most privacy, but at the cost of security and speed. You may experience the ‘bad neighbor’ effect – someone using the same proxy does something illegal and you get in trouble with websites or authorities. General proxies are usually overcrowded and websites frequently block them.
6. Public Proxies
Anyone can own a public proxy and make it available to the public for free. They’re considered a quick pass to access geo-restricted content or to improve your privacy online.
I strongly suggest you never use free public proxies. Here’s why:
-
-
-
-
- Cybercriminals may own free proxies. They can monitor and steal your sensitive data, and even impersonate you.
- Owners can sell your data to third parties.
- Free public proxies can alter your web traffic and spam you.
-
-
-
You get what you pay for – poor speeds and shady service.
If you need a risk-free unblocking tool that preserves your digital identity, give CyberGhost VPN’s 45-day money-back guarantee a try. We encrypt your personal information and maintain one of the fastest server networks available.
7. SOCKS Proxies
Unlike HTTP or HTTPs proxies that only work with websites, SOCKS proxies privatize all kinds of internet traffic including email and torrenting. Although they don’t encrypt your data, they’re still more secure and private than other proxies. That’s because SOCKS proxies don’t interpret or analyze your internet traffic.
8. Residential Proxies
Typically, proxy servers are present inside a data center, and proxy owners assign them IP addresses. A residential proxy is an actual device, like a laptop or a mobile phone with an ISP-assigned IP. Residential proxies appear legitimate and trustworthy to websites.
That said, residential proxies are way too expensive for casual browsing and still won’t give you end-to-end encryption and enhanced privacy.
9. Reverse Proxies
Unlike typical proxy servers that act on a user’s behalf, a reverse proxy sits in front of websites or servers and receives your requests on the website or server’s behalf.
Offices and websites usually use these proxies to keep malicious users from accessing their internal network or servers. They also use reverse proxies for load balancing (distributing traffic equally among servers), caching popular web pages for better speed, and to save resources. As an end-user though, you’re probably only interested in the different kinds of forward proxies.
Risks of Using Proxy Servers
Now that you have a good idea of how proxies work, you should also be aware of the risks involved in using one. Just in case you’ve had a long day, here’s a quick rundown of what’s at stake.
1. Your data
Proxies don’t encrypt your data. If you can’t trust your ISP with your data, why would you trust unknown proxy owners?
2. Your Identity and Money
When your data isn’t encrypted, cybercriminals can steal your passwords, credit card information, and other credentials to impersonate you or steal your money.
3. Your Time
Most proxies take time to inspect your traffic on top of the rerouting lag. They also have static configurations, so you can’t play around with settings and protocols to improve speeds. While free proxies can’t afford the hardware and software to give you optimal speeds and minimal ping, reputable, paid proxies are often overcrowded and overloaded.
Proxy owners can configure proxies to allow certain kinds of traffic and block the rest. As such, many of them block bandwidth-intensive activity like streaming and torrenting.
4. Your Privacy
Proxies keep logs of your internet activity. Proxy owners may use this information to gauge your interests and preferences, so they can show you relevant ads. Worse still, they may sell this data to third-party advertisers. Once this happens, your personal information may be sold and traded to thousands of other companies around the world.
5. Your Device
When you connect to a proxy server, you’re essentially trusting the owner to not misuse the connection to infect your device with malware. Got yourself a trusted provider? Uh… you may still fall victim to malvertising – malicious actors infecting legitimate advertising networks with malware – so beware!
Is there a better alternative to a proxy to protect your online freedom and privacy? Yes, a VPN! Let’s get to know more about it.
What Is a VPN?
A VPN is a network of servers that lets you access the internet with superior privacy and security. Like proxy servers, VPN servers act as intermediaries between you and the internet. And that’s where their similarities end.
The VPN servers route your online traffic, receive your internet requests, and send them off to the destination servers – websites and services. What that means is, you can use a VPN to get an IP address in a different region. VPNs also encrypt your internet traffic end-to-end (from your computer to the website you’re visiting). That way others can’t snoop on your data or monitor your activity.
Is a VPN Better than a Proxy?
Absolutely! CyberGhost is a premium VPN service, which means it gives you much more than a new IP address. Here’s what a VPN offers that a proxy doesn’t:
VPN vs. Proxy Server Comparison Table
| Features | Proxy Server | CyberGhost VPN |
| New IP address | ✅ | ✅ |
| End-to-end encryption | ❌ | ✅ |
| No-Logs policy | ❌ | ✅ |
| Automatic Kill Switch | ❌ | ✅ |
| Configuration options | ❌ | ✅ |
| Speed-optimized servers | ❌ | ✅ |
| Dedicated IP address | ❌ | ✅(Optional) |
| Advertisements | ✅ | ❌ |
| 45-day money-back guarantee | ❌ | ✅ |
Let’s dive in deeper to understand each benefit better.
1. Advanced End-to-End Encryption
Remember I said your IP address is like your home address? Now imagine if your postman or the postal service could look into every parcel you send or receive. Sounds absurd and terrifying, doesn’t it? Your ISPs and network admins can do exactly that with the data packets you send to the internet. They see what you’re doing online, even when you use a proxy, and so do cybercriminals and snoopers.
CyberGhost VPN uses strong encryption to scramble your internet traffic before it leaves your computer. Your ISP, network admin, or any other third party won’t know what you do online. If someone ever managed to hijack your connection and steal your data, they wouldn’t be able to interpret, utilize, or alter it in any way. This is probably CyberGhost’s main advantage over proxies.
2. No-Logs Policy

You won’t find any security and privacy policies with most general proxies. That’s because proxy owners notoriously monitor and store your private data and session details. This is worse than websites or your network admins keeping tabs on you since you can’t tell when cybercriminals own or compromise a proxy server.
CyberGhost VPN has a strict no-logs policy. We use RAM-only servers, which means we don’t store any connection data. No one can compel us to share anything from our backend, because we never keep it in the first place. We also back this up with our Romanian headquarters!
3. Faster Speeds for Streaming, Gaming, and Torrenting
Proxy owners can configure proxies to allow certain kinds of traffic and block the rest. The proxy takes time to inspect your traffic on top of the rerouting lag. Proxies also have static configurations, so you can’t play around with settings and protocols to improve speeds.
Free public proxies are always overcrowded, and their outdated server hardware can barely keep up with the load. They’re useless for any activity requiring fast connection speeds.
By comparison, CyberGhost VPN has a massive server fleet with thousands of top-notch servers across 90+ countries. We’ve got 10-gbps servers in the busiest locations, and we’re always adding more, so they’re never overcrowded. You can choose from different protocols depending on your needs. The super-fast WireGuard® protocol is perfect for smooth UHD streaming.
CyberGhost VPN also has dedicated servers for streaming, torrenting, and gaming to guarantee access to websites and give you the performance you need. You won’t even get this kind of flexibility with most VPNs, let alone proxies.
4. Extra Security Features
Proxies have very limited functionality and features. In contrast, CyberGhost VPN has tons of additional privacy features, including:
-
- 💪 Automatic Kill Switch: Our Kill Switch feature disconnects your device from the internet the moment you lose connection to our servers. We secure your data even if your VPN connection ever drops.
- 💪 NoSpy servers: We host our premium NoSpy servers inside our Romanian headquarters, outside the 5,9, and 14-eyes surveillance alliances. Our team manages the servers end-to-end, so we can ensure the highest security standards.
- 💪 Dedicated IP address: Typically, you get a new, shared IP address whenever you connect to a VPN. Get your very own dedicated IP address with CyberGhost VPN to access your office network or web services that restrict changing or sharing IP addresses. Thanks to our unique token system, no one can identify who owns a specific dedicated IP address, not even us.
Use CyberGhost VPN for Superior Security
You now know all about the pros and cons of proxy servers and why you should never use a free proxy. Sure, free web proxies can give you quick access with zero commitment, but the risks are far too great to ignore. As for paid, reputable commercial proxies, I’d still opt for CyberGhost VPN for its advanced encryption, unmatched server performance, and extra privacy features.
If you could get creme brûlée’s rich texture and delectable vanilla-caramel flavor with Jello’s ease, then why not? Simply subscribe to CyberGhost VPN and download the app to get enhanced online privacy. You’ve got nothing to lose in trying us out, as we offer an industry-leading 45-day money-back guarantee!
FAQ
What is a proxy server and what’s it used for?
A proxy server acts as an intermediary between you and the internet. Proxies intercept your web requests and forward them to the website or service you want to access. This means the location associated with your request is from the proxy server, not your device. They’re not always reliable as some websites can tell if you’re using a proxy server and may deny you access.
Download CyberGhost VPN today to get unrestricted internet access. You can hide your location and enjoy improved privacy.
What‘s an example of a proxy?
An HTTP proxy is one of the most common types of proxy. It replaces your IP address before forwarding your HTTP requests to the destination web servers. You’ll easily find many web proxies on the internet.
That said, I strongly suggest you avoid free, public proxies. They don’t encrypt your traffic, so cybercriminals or other third parties may be able to steal your data. CyberGhost VPN gives you many more benefits than an HTTP proxy without any downsides. Get in touch with our friendly 24/7 customer service team today to learn how we keep your connection safe and private.
Should you always use a proxy server?
No, use proxies only when you need to hide your original IP address or geolocation. For instance, when you’re accessing websites or web services unavailable in your region. Most free and commercial proxies will significantly slow down your connection speeds, though.
CyberGhost VPN is a safe and much faster alternative to a proxy. You’re always just one tap away from a safer internet with CyberGhost VPN.
Is a VPN a proxy?
No, a VPN is much more than a proxy. A VPN hides your IP address like a proxy server. Unlike a proxy, the VPN also creates a secure and encrypted tunnel between you and the websites you visit. This prevents third parties like your ISP or cybercriminals from seeing what you get up to online.
A reliable VPN like CyberGhost gives you improved privacy and security on the internet. Try us out risk-free with our 45-day money-back guarantee today!
Are there downsides to using a proxy?
Yes. You may experience difficulties when using a proxy, including a painstakingly slow internet connection, websites blocking your access, and targeted ads. Proxies also don’t encrypt your traffic. That means your data gets exposed to your ISP, network admins, malicious intruders, and other third parties.
Proxy owners may monitor your activity and store your data too. CyberGhost VPN offers advanced encryption and a no-logs policy. Your data will always be out of any snoopers’ reach!

Leave a comment