Remember the iconic scene in Avengers: Age of Ultron when Ultron gains consciousness and hacks into Jarvis? Oh, how the movie does its best to portray Ultron as a virus. But in reality, because Ultron uses Jarvis’ vulnerabilities to attack, Ultron is actually a worm infection.
Computer worms and viruses have a long history of getting mixed up in movies and literature. If Disney got it wrong, it’s no wonder that the average internet user thinks the two are synonymous with one another. But the truth is that, while they might have some similarities, they’re two very different threats. And each one should be taken very seriously.
Are You Protected? Improve your online privacy and protect yourself from worms, viruses, and malware with one intuitive app. Install the CyberGhost Suite and take care of all your security needs in one go.
Virus versus Worm: The Basics
First thing’s first. What’s the difference between a computer worm and a virus?
Let’s look at some definitions.
Computer Virus
A computer virus is a malicious piece of code that is designed to spread from device to device by self-replicating. It’s written by cybercriminals to attach, overwrite, or otherwise replace another program on your computer in order to reproduce itself without your knowledge.
A virus can cause a number of problems on an infected device. It can damage data, destroy files, siphon your private information, format hard drives, or make disks unreadable. A virus can enter your computer as an email attachment, in a downloaded file, or hidden on a zip drive or CD. It’s usually not obvious that a virus is present on a website, in an email or elsewhere.
Computer Worm
A computer worm is a type of malware that reproduces itself and spreads over network connections. It doesn’t usually infect computer files but instead infects another computer on the network.
They’re a form of malware which runs invisibly in the background and overtakes parts of an operating system. It’s pretty hard to tell you’re dealing with a worm until your systems are slowed down and your device’s resources are consumed.
Worm infections are especially egregious, as they can spread without user interaction. Once a computer worm is active on an infected system, it’s able to spread throughout a network. In the past, computer worms used to attack through infected storage media, like CDs and later USB drives.
Now, emails are a common gateway for these worms to spread, as they can create and send outbound messages to all addresses in a user’s contact list.
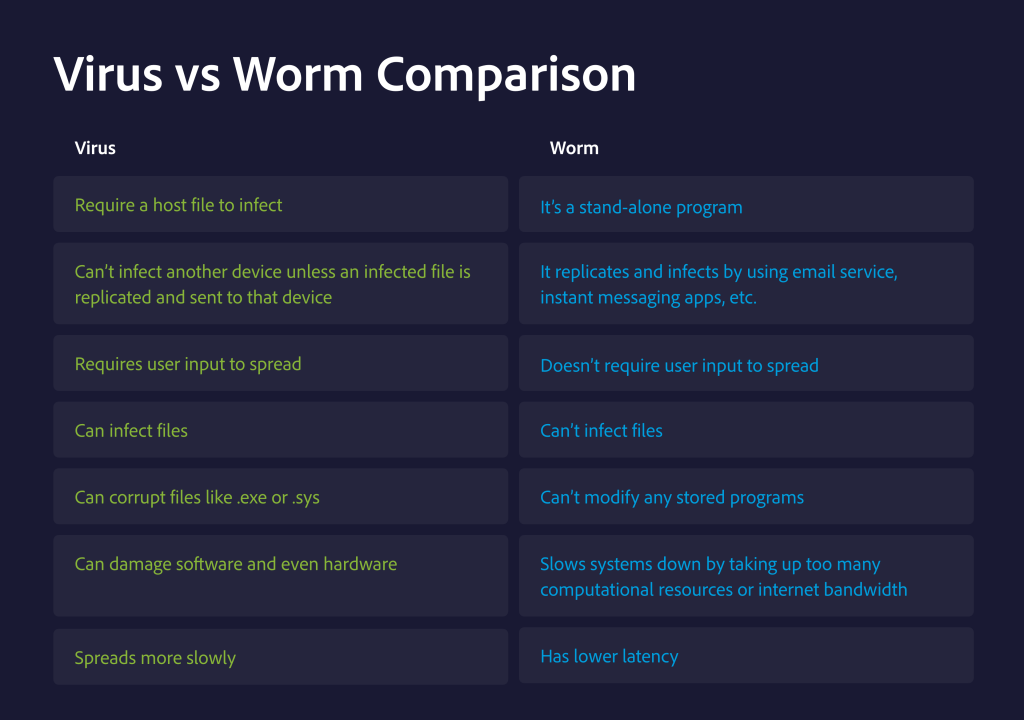
While they might seem similar by the definitions alone, viruses and worms have different end goals.
The main difference between computer worms and viruses is that a worm is a self-replicating program that spreads without user interaction. Viruses, on the other hand, generally require some action on the part of a user to spread, despite the fact that they are also self-replicating.
Let’s see an overview of the main difference between worms and viruses.
How do Computer Viruses and Worms spread?
Cybercriminals have gotten way more creative in the past few years. Gone are the days of relying on malicious floppy disks to deliver a virus.
Nowadays, with the prevalence of Wi-Fi connections and increasingly more gadgets connected to the internet, cybercriminals developed a wider variety of ways to infect someone’s device.
They rely on a combination of social engineering and system vulnerabilities to deliver malicious code.
Take for example the Nimda worm.
Nimda is actually “admin” spelled backwards. It was a hybrid worm that spread via infected email attachments and across websites running vulnerable versions of Microsoft’s IIS web server software. Back in 2001, Nimda actors were responsible for infecting thousands of Asian and European businesses in a matter of days. The worm also exploited weak passwords to speed across different machines on local networks.
Hi-tech firms including Microsoft, Dell, and NTL were among the victims of Nimda.
Klez is a virus that caused similar damage back in 2001. It spread by sending fake emails with spoofed recognized senders to trick people into installing the virus.
Then it infected files, copied itself, and spread throughout each victim’s network. It hung around for years, as cybercriminals released more versions of the virus, with each version more destructive than the last.
So, it’s clear that both types of malware are disastrous. But how exactly did they spread so fast?
Emails are a popular way to spread different types of malware, like trojans or ransomware. Email attachments can carry some pretty shady code, which is why most email providers offer an attachment scanner service. However, this isn’t 100% fool-proof, so keep in mind to be mindful of attachments, especially from senders you don’t know.
Dyre is a well-known banking malware that spread almost exclusively through spam emails back in 2014. It made headlines after stealing more than $1 million in a single campaign. Dyre worked by persuading victims to login into a bank website after which the perpetrators could steal financial information. After infecting a computer, the malware used it to out spam with the malicious attachment to other people.
Unfortunately, it’s not obvious if an email is malicious. Always scan the attachment and check the sender’s email address. If the email address contains any typos or weird misspellings, it’s a red flag.
Suspicious Websites
Unfortunately, not all websites have your security in mind. Some websites have malicious code hidden within their HTML. This means that every time the page loads, there’s a chance the infected code will latch onto your device. This is why it’s crucial to stay away from HTTP sites.
According to a research by Symantec, the top 10 most popular shady domains is:
- .country
- .stream
- .download
- .xin
- .gdn
- .racing
- .jetzt
- .win
- .bid
- .vip
Around 98% of all websites with these domains contain some form of malware. So avoid them like the plague.
Downloads and File Transfers
This is a typical scenario – cybercriminals attach malicious code to different types of files and pass them off as legitimate programs or apps. You might know this as a trojan. Trojans try to pass as anything you can imagine: an alarm clock app, a QR scanner app, a compass app, a photo editor app, an Internet speed test app, or a file explorer app. It can really be anything.
Trojans will have you thinking you’re downloading a freemium app or a public domain piece, but really, you’re in for an unpleasant surprise.
Instant Messages
Social media platforms are a gold mine for malicious parties. Both mobile and desktop messaging apps can be a breeding ground for both viruses and worms. Generally, they’re sent through an external link in a private message. It can be from a sender you don’t know, or from one of your friends whose device is infected with malware.
But it’s never a good idea to click on links, unless you specifically asked for a website. If it’s from an unknown sender, you’re better off just ignoring the message.
If they send a file, be careful about .txt or .svg files as they’re popular choices.
Trojan can sometimes also hijack instant messaging apps and send out malicious files. Like the Stresspaint that was found hidden inside a fake stress-relief app and spread through Facebook spam campaigns to infect 35,000 users.
P2P and Filesharing
Filesharing networks are convenient and easy to use. But some uploaders can also hide some malicious files among the data they put out. This can be on torrent sites, cloud storage, or even USB sticks.
A study conducted by researchers at Digital Citizens Alliance and RiskIQ actually looked at malware hidden among torrent files.
The researchers found that almost one-third of the 800 torrent sites in the study served malware on the users’ devices between June and August 2015. This means that about 12 million Internet users per month were infected by downloading material from torrent files.
The most popular trojans hidden in torrent files are:
- Xtreme Rat
- Bifrost
- Back Orifice
- NJRat
- ADWind
- DarkComet
- BlackShades
- SBU7
- Poison Ivy
- Cerberus
Networks
Unsecured networks, like the public Wi-Fi you find in restaurants, airports, and bars, are notoriously famous for attracting malicious parties. But a lesser-known fact is that cybercriminals can hide viruses and worms in network packets.
Afterward, the code can spread to any device across the network.
The Emotet malware is a good example of this. Emotet first infects a system with a self-extracting RAR file, containing two binaries, worm.exe, and service.exe. After the RAR file unpacks itself, Worm.exe executes automatically.
The worm.exe binary immediately begins profiling wireless networks in order to attempt to spread to other Wi-Fi networks and infect other devices.
Which is More Dangerous: a Computer Virus or Worm
Both computer viruses and worms are dangerous. But the damage they can do depends on what they were programmed to do. Some variants are coded to be mainly nuisances and just plaster you with pop-ups.
Others are designed to steal your private and financial information. This spells disaster for your privacy.
In general, the damage caused by a virus or a worm are similar and depends on the malicious code it is hiding. Some are meant to be nothing more than minor nuisances and just pester you with annoying, vulgar popups. However, others are designed to steal private information, including financial details.
But, the general consensus amongst experts is that a worm is more dangerous than a virus because it can spread much faster. For example, a worm can be created to infect all your email contacts. It will infect your contacts and infect their contacts and so on. Viruses, on the other hand, require you to do something for it to infect your computer.
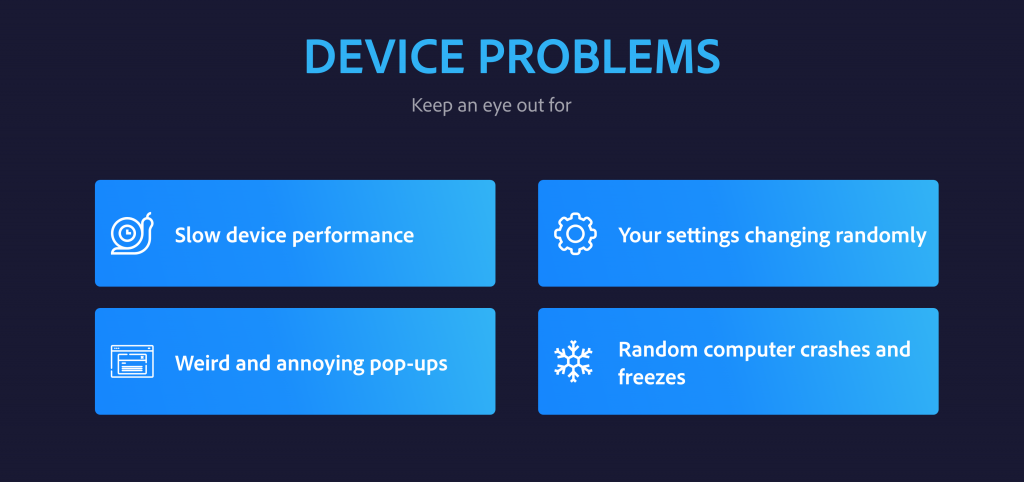
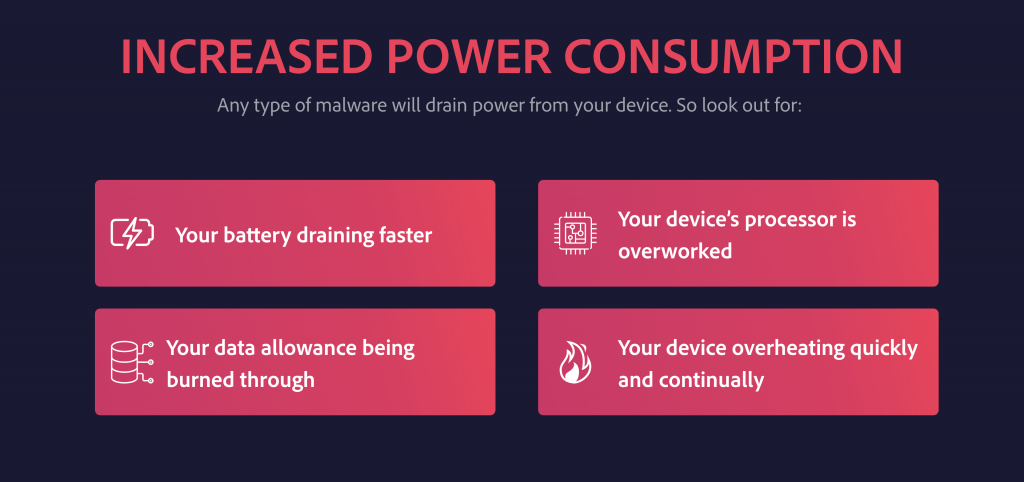
How to Detect a Virus or a Worm
It might not always be easy to know when you are dealing with a computer worm or a virus. They’re not like ransomware, where you get an in-your-face notification.
With worms and viruses, it’s harder to tell that malware is actively poking around your system.
So it’s important to exercise caution and be mindful of any recent changes.
But if you have reason to suspect you’re dealing with a virus or a worm infection, here’s what you need to look out for.

What to Do if You Have a Virus or Worm
Whether you’re noticing your device is acting strangely or your security software notified you about the threat of a virus or a worm, you might find yourself wondering about the best course of action.
If you find that your device is infected with a worm or virus, the steps for minimizing damage and removal are quite simple.
First, you need to minimize the damage. While it might seem easier said than done, it is really quite simple. The easiest way to do this is to shut off your internet and cut all internet access to your devices. It will prevent the worm or virus from transmitting your data and “blind” the cybercriminal.
Next, you need to run a virus scan and delete any suspicious files. We recommend saving all important documents to an external hard drive, USB stick, or secured cloud.
Lastly, you need to remove the malicious code. Run your antivirus program (and make sure it is updated). Most times, the antivirus program will be able to locate and isolate the threat. If for, whatever reason, the worm or virus will not leave quietly, you can restore your computer to its factory settings. But remember, this will cause you to lose all your data.
How to Protect Yourself from Computer Viruses and Computer Worms
A good defense is the best offense.
Here are 8 things you can do to protect your devices from viruses and worms.
- Use a good antivirus. The CyberGhost Security Suite has a cutting edge antivirus powered by Intego. It will protect you from most known viruses and the definitions are regularly updated to keep up with cyberciminals writing new malware.
- Use strong and unique passwords. Do not use the same password for every website. Get a password manager to help you manage, and store all your passwords in a secure vault.
- Enable two-factor authentication (2FA) to prevent unauthorized access to your accounts.
- Use CyberGhost VPN. This will add another layer of encryption to protect your connections.
- Don’t ignore device updates. Whether they’re for your operating system or an app, they can provide essential security patches.
- Enable your firewall. Firewalls prevent certain types of infection by blocking malicious traffic before it can enter your computer.
- Avoid clicking on suspicious links or attachments. Even if you know the sender, it’s always a good idea to run a scan and check all shortened links.
- Use only HTTPS web connections to enter your personal details.
FAQ
What is more dangerous, a worm or virus?
Both worms and viruses are malicious, self-replicating programs that can spread throughout a network, and both cause the same amount of damage, largely depending on the way they were coded.
General consensus, however, is that worms are more dangerous because they can spread faster by exploiting vulnerabilities or back doors, often without your knowledge or consent.
Can a virus execute itself?
No, a virus can’t execute itself. The malicious code needs a host file to infect in order to replicate itself.
Can a virus affect my Wi-Fi connection?
Most viruses need an online connection to spread because otherwise, cybercriminals would require physical access to your devices. But some virus types can use your Wi-Fi connection to spread across your network.
What was the most expensive virus?
The worst computer virus outbreak in history was called Mydoom. It caused an estimated damage of $38 billion in 2004. Adjusted for inflation, it is around $52.2 billion today. It was spread via mass emails. It also roped infected machines into a web of computers, called a botnet, that performed distributed denial of service (DDoS) attacks.
How can I tell if a download is safe?
The best way to check if a file you downloaded is safe is to run an antivirus scan. If the scan comes back clean, it’s great news.
But there are also some things you can look out for when you download files.
Always download from official websites and official app stores. Don’t ever download through unsecured HTTP sites.
Assess the size of the file you’re downloading. If you’re downloading a .jpeg image, but the size claims to be 2 GB, there’s something fishy there.
Lastly, check if the file is signed. When you run an executable file, you’ll get a security warning. Check the publisher’s name and make sure the company is a legitimate one.
Have you ever dealt with a computer virus or a worm? Let me know about your experience in the comments below.
Until next time, stay safe and secure!

Leave a comment