You’re working away at your computer, but your programs are responding slowly, your browser is redirecting you to random websites, and suddenly, you see the blue screen of death. What the heck is happening?
You could need a simple software update, but you’re probably experiencing something much more sinister. These symptoms could indicate your computer caught a trojan virus. If that’s the case, your sensitive data is at serious risk.
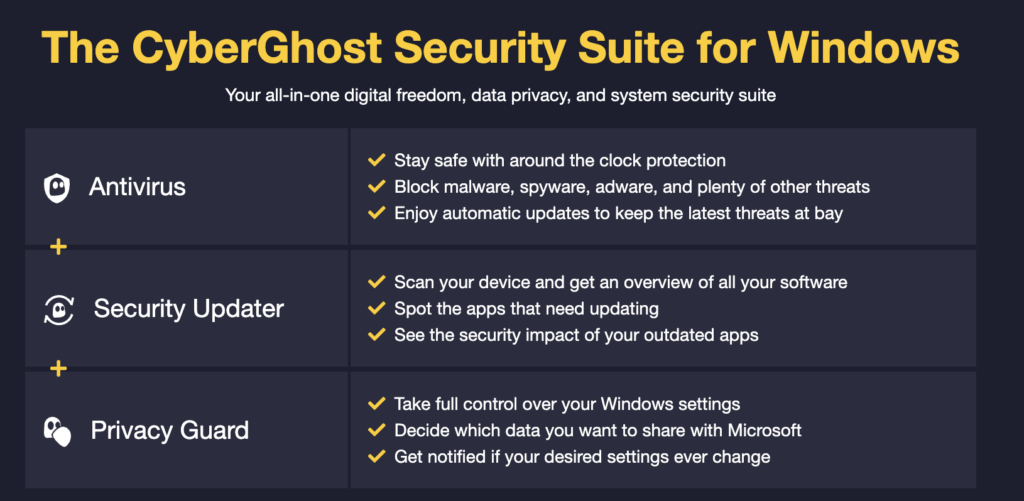
Read on to learn more about what trojan viruses are, how to remove them, and the best ways to protect yourself going forward. If you’re looking for a best-in-class security solution, the CyberGhost Security Suite offers protection against trojans, malware, and network attacks while keeping you safe online.
What Is a Trojan?
A trojan horse, or trojan, is malware that invades your computer disguised as legitimate software. Cybercriminals use it to spy on your online activity, control your device, and steal your sensitive data. That threatens you with fraud, identity theft, and blackmail.
What Do Trojans Do?
Trojans hide within seemingly harmless file attachments or web apps. When someone downloads or installs them, they release malicious code that can:
-
-
-
-
- Log your keystrokes to steal your passwords or account numbers.
- Browse your hard drive to acquire sensitive data.
- Delete files or the entire hard drive.
- Send spam from your email account.
- Freeze, shut down and/or take over your computer.
-
-
-
Many trojans lay dormant on your computer awaiting instructions from their “central command”. Others may download additional malware to help them bypass your security settings. Some hijack your computer to facilitate criminal activity.
How Does a Trojan Virus Spread?
A trojan isn’t technically a “virus” because it doesn’t self-replicate. Instead, trojans spread when you unknowingly download or install an application that hides the malware.
Common trojan infection methods include:
-
- 👾 Email attachments: Trojans often hide in emails that appear to be from someone you know. The emails can contain an attachment, such as a Word doc, PDF or Excel. Another technique is to get you to click on a link that downloads the malware in the background. As soon as you open the link or attachment, though, the trojan infects your computer.
- 👾 File sharing websites: You’re probably familiar with file-sharing websites that offer copies of your favorite series or the latest game patch. Cybercriminals use these torrent sites to promote free file downloads to unsuspecting users. If they take the bait, a trojan virus infiltrates their device.
- 👾 Infected websites: Unsecured websites are easy targets for cybercriminals, allowing them to upload malware or even take over the entire site.
- 👾 Spoofed messages: You could receive a “spoof” message on an online chat app. That’s a message that appears to be from someone you know but actually isn’t. The “spoof” message may have an attachment with a trojan-infected file.
Most trojans are delivered through your network connection, adding a layer of protection between you and the public internet is often the best way to prevent your devices from getting infected. CyberGhost VPN stops malware, trojans, and other network attacks in their tracks.
Examples of Trojan Viruses
Since the trojan’s invention, several notable examples of the computer virus have inflicted a lot of damage. Here’s a list of some that you’ll want to avoid.
Zeus
Also known as Zbot, Zeus is a malware package that infected 3.5 million+ computers in the US. This included computers at the Bank of America, NASA, and the US Department of Transportation.
Zeus steals banking details and other financial information and sends it back to the criminal server. The trojan malware also has several variants like Ice-X, which can control browser content to extract information during financial transactions.
Rakhni
Rakhni is malware that originated in 2013. More recently, it started delivering a cryptojacker (or ransomware) to computers. This allows cybercriminals to hijack your computer and mine for cryptocurrency.
ILOVEYOU
Released in 2000, ILOVEYOU caused the world’s most damaging cyberattack, costing the world $8.7 billion in losses. It spread via a phishing email that read, “Kindly check the attached love letter coming from me”. The email also had an attachment named “ILOVEYOU”. Those curious enough to open the file had their machines infected with malware. It would overwrite files in their devices and then send itself to their entire contact list.
Trojan Types
Since the trojan’s debut in the 1970s, millions of its variants have plagued the digital world. Take a look at some of the most common trojan types.
- Backdoor trojan: Creates a “backdoor” on your computer, allowing a malicious third party to control your computer and steal your data. They can also use this backdoor to upload more malware to your device.
- DDoS-attack trojan: This type of trojan performs Distributed Denial of Service (DDoS) attacks by flooding a network with traffic to take it down.
- Remote access trojan: Allows cybercriminals to fully control your computer through a remote network connection, which lets them log your keystrokes and steal your information.
- SMS trojan: Hijacks the SMS functionality on your phone. It uses it to send and intercept text messages, or to message premium-rate numbers to hike up your bill.
- Downloader trojan: Targets your already-infected computer, downloads and installs more malware, including trojans and adware.
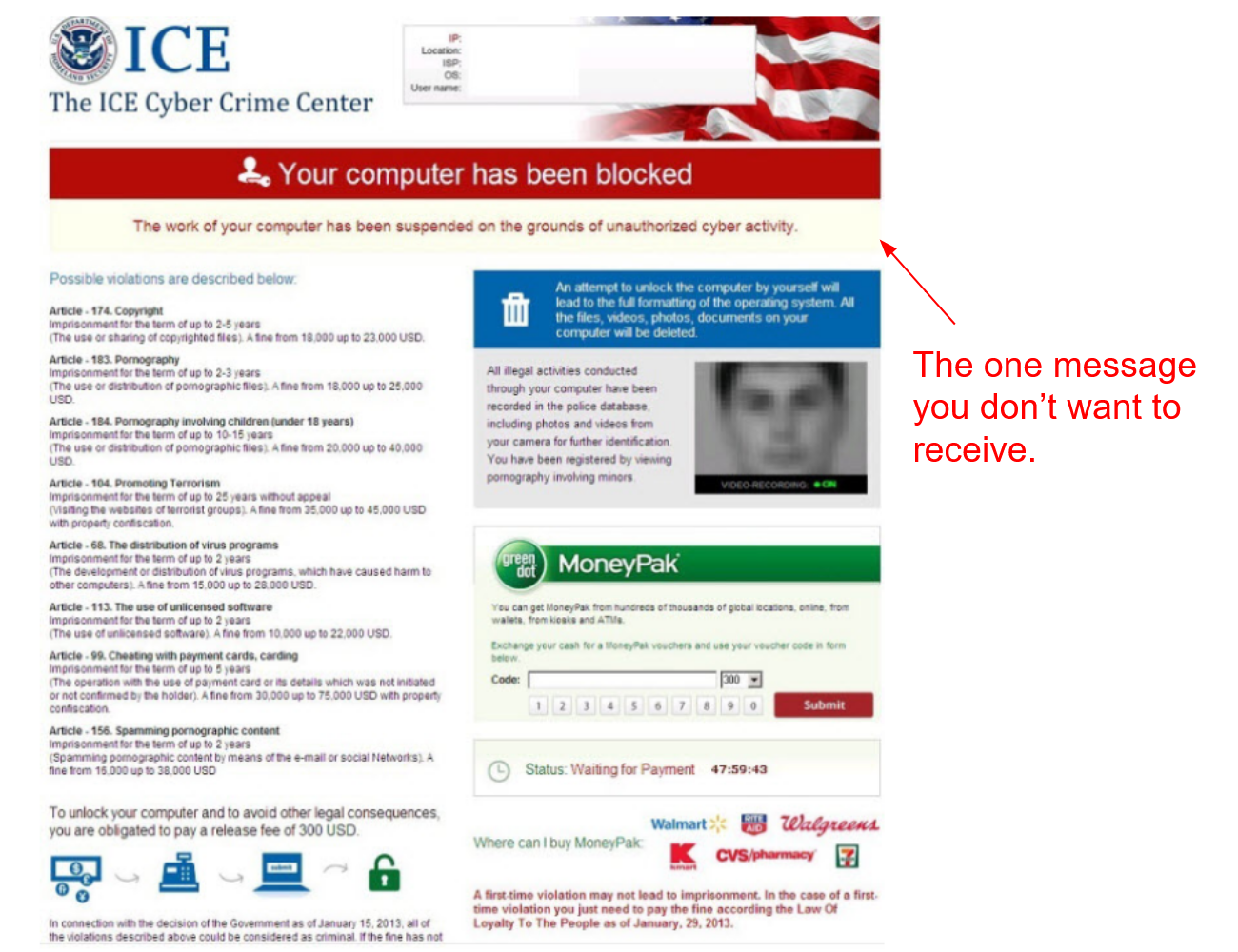
- Ransom trojan: Malware that seeks a ransom to undo the damage done to your computer, like impairing performance or withholding data.
How to Know If You Have a Trojan Virus
Trojans are very good at going undetected, meaning by the time you notice the problem, it’s already too late. That said, you can look for some subtle hints that may indicate a trojan infection, such as:
- ✔️ Impaired device performance, like frequent crashing and freezing and slow downs.
- ✔️ Increased browser and pop-up ads promoting antivirus products or scans. When you click on them, they download more malware to your device.
- ✔️ An altered desktop appearance, including changes in color or screen resolution.
- ✔️ Your taskbar has changed or disappeared completely.
- ✔️ More spam emails than usual.
- ✔️ Programs you don’t recognize and never installed appear in your task manager.
- ✔️ Your browser redirects you to unknown websites when browsing online.
Can a Trojan Virus Infect a Phone?
Yes, trojans can infect your mobile devices. The malware usually disguises itself within a convincing fake app. Unsuspecting users download this app from unofficial or pirate app markets by unsuspecting users. The hidden malware can then steal personal information from your phone. It can also allow cybercriminals to profit by sending premium-rate SMS from your device.
Thankfully, if you have an iPhone, the odds of getting a trojan infection are smaller. This is thanks to Apple’s “walled garden” security protocol, meaning third-party apps need the App Store’s vetting and approval. iOS apps are also unable to interact with other apps or gain deep access to your phone’s operating system.
That said, iOS malware is becoming more common, whereas a jailbroken iPhone won’t have the same protection against malware.
The best way to keep your mobile devices safe from trojans is to use CyberGhost VPN when you go online. The network has built-in malware, trojan, and spam filters that eliminate threats before they get to you.
How to Protect against Trojan Viruses
Practicing good cybersecurity hygiene is key to protecting your devices against trojan malware.
| Protecting Yourself Against Trojan Viruses | |
| Do | Don’t |
| Install reliable and robust antivirus software that can protect all your devices. | Download or install software from an untrustworthy source. |
| Update your operating and security software as soon as new updates are available. | Connect to public Wi-Fi without a VPN. |
| Protect your online accounts with secure and unique passwords. Use mixed characters, letters, and numbers. | Visit unsafe websites – safe websites always have a padlock icon next to the URL. |
| Keep your sensitive information protected behind firewalls and encryption. | Click on unfamiliar pop-ups and banners, particularly those warning you your device is infected. |
| Backup your files to prevent you from losing anything important in case you fall victim to a malware attack. | Open attachments or links sent via email from an unknown sender. |
Trustworthy VPNs are a great barrier against trojans and malware because they filter your traffic through their own network before it gets to you. Download CyberGhost VPN and keep trojans at bay on all your devices.
How to Remove a Trojan Virus
Trojan removal is a complicated process that’s best left to a trustworthy antivirus or (if it’s a custom-designed malware) actual cybersecurity experts.
You can remove certain trojans by disabling start-up items on your computer that aren’t from trusted sources. Be sure you know what programs you’re fiddling with because you could seriously impair your device’s function.
Here’s tried-and-tested step-by-step method of removing trojans from your computer:
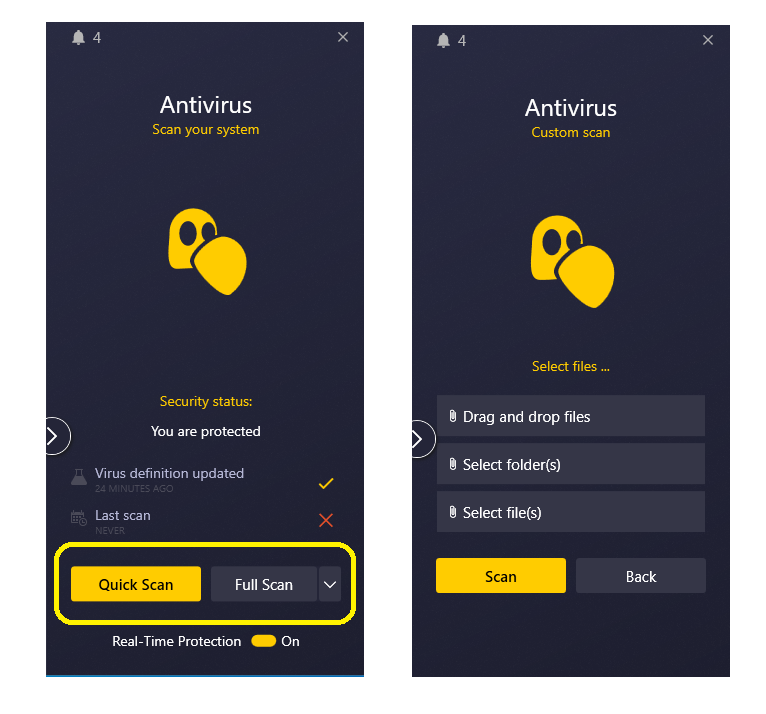
- Get a good antivirus. If you already have one and you still got infected by a trojan, you need a better solution. The CyberGhost Security Suite comes with a built-in, cutting-edge antivirus.
- Reboot your computer in Safe Mode. This will disable most unnecessary functions and software. Hopefully, this includes everything associated with the trojan.
- Install your antivirus and make sure it updates to the latest version. If the virus definitions are not updated, there’s a chance that the antivirus won’t recognize your infected files.
- Run a full system sweep. Spare no file or folder. The antivirus should either prompt you about what to do with the files (delete, quarantine, attempt clean-up, etc.) or take action first and then give you a full report.
- That’s it! You’re Trojan— free.
 If nothing comes up on the scan and you’re absolutely positive you’re infected, go on to 6.
If nothing comes up on the scan and you’re absolutely positive you’re infected, go on to 6. - Safe backup. The contingency solution for stubborn Trojans is to completely format the device and reinstall everything, OS included.
- Just make sure you safely backup any important files and that no infected files are transferred in the process.
- A good rule of thumb is to archive everything and keep it in the cloud. Make sure to scan the archive when you download the files someplace else, and then do another scan after you unzip the files.
- Format everything & reinstall (factory reset). Once you’re done with the backup process, it’s time for a clean slate. Format all your hard drives and reinstall everything. Make sure the antivirus is one of the first apps you add to the fresh installation and scan your computer once more before setting everything else up.
The Bottom Line
If you notice changes in your computer’s performance or desktop appearance, you might have a trojan. Trojans can cause a serious security risk before you’re even aware it exists on your device. They can monitor your keystrokes, steal your sensitive data, and install additional malware.
Thankfully, protecting yourself against trojan viruses is fairly straightforward and most are easy to remove.
FAQ
Will resetting my PC remove a trojan virus?
Running a factory reset on your PC is an effective way to remove trojan malware and other persistent viruses. The reset will wipe all data stored on your computer’s hard drive, so don’t forget to back up anything important. But make sure you’re not backing up the virus!
That said, a factory reset doesn’t remove infected files stored on backups, meaning a trojan could return to your PC when you restore your data. Get the CyberGhost Security Suite and scan your backup drive for malware before you move anything back to your computer.
How do I make sure a trojan has been removed?
A legitimate antivirus will be able to tell you if the trojan has been removed. Make sure your virus definitions are up to date and run the scan in safe mode if you want to make sure you catch the pesky thing.
The CyberGhost Security Suite is equipped with a cutting-edge antivirus solution powered by Intego.
Who invented the trojan virus?
Computer programmer John Walker is commonly credited for inventing the first trojan virus, back in 1975. Walker’s virus, (PERVADE) piggy-backed ANIMAL software, which were quite popular at the time — ANIMALs were various “games” where the computer would ask you 20 questions to try and guess what animal you’re thinking of.
While users played ANIMAL, PERVADE examined all computer directories available to the player and copied ANIMAL to those that didn’t already have it. While not malicious, PERVADE is by definition a trojan: it hides inside another program and performs actions without the user’s permission.
Use CyberGhost VPN when you go online to keep trojans away. The network filters a lot of attacks and malware when rerouting your traffic, so you’re less likely to get infected by accident.
Can a trojan virus work without the internet?
Once activated, a trojan can block, delete, and copy data without access to the internet. That said, cybercriminals can only steal or send your data from your device when the internet is available.
With your phone, trojan malware can work without the internet. Some of them can use SMS to send and receive data. If you’re not sure how to use CyberGhost’s antivirus to get rid of your trojan, you can always reach out to customer support — they’re super friendly and available 24/7.

Leave a comment
Majeedah Rashid
Posted on 24/04/2023 at 10:07
I just installed Norton and it is not removing the viruses and malware on my computer. What can I do
Ghostie
Posted on 24/04/2023 at 17:55
Hi, Majeedah,
This might be a situation where the computer is too far gone. If nothing else worked, you might want to jump to steps 6 & 7 under the How to Remove a Trojan heading.
It will take a bit of time to do a full reinstall, but at least it’s effective.
Stay safe,